There are many tools available for today’s garden that are designed to make life easier for the interested hobby gardener. This includes the Gardena smart system, which is compatible with various robotic lawn mowers and various irrigation devices. Since the system, similar to Homematic IP, can be controlled exclusively via cloud, special attention must be paid to security. Time to take a closer look at the system.
Gardena, a German manufacturer of an extensive portfolio of gardening tools, was founded in 1961, and since 2007 belongs to the Swedish company Husqvarna AB, but will continue as an independent division. Gardena has a long tradition in the field of garden irrigation, for example, it has had irrigation controllers in its product range since 1985.
In our test, we put the Gardena smart Water Control Set on the security test bench. It consists of a gateway and an irrigation control system and can be controlled via Android or iOS app as well as via web.

Setup
A Husqvarna account must be created as part of the setup process. In order for the Gardena smart Gateway to be linked to this account, it must be connected to the Internet either via Ethernet cable or WiFi. In the user manual, Gardena explicitly recommends the initial connection via Ethernet but does not go into the reason for this. However, this was quickly noticed: When set up without a Ethernet cable, the gateway creates an unencrypted WiFi hotspot to which the smartphone must be connected. After connecting, the gateway’s website must be opened in the browser and the first eight characters of the serial number must be entered as a password. After authentication, it is then possible to search for surrounding WiFi networks.
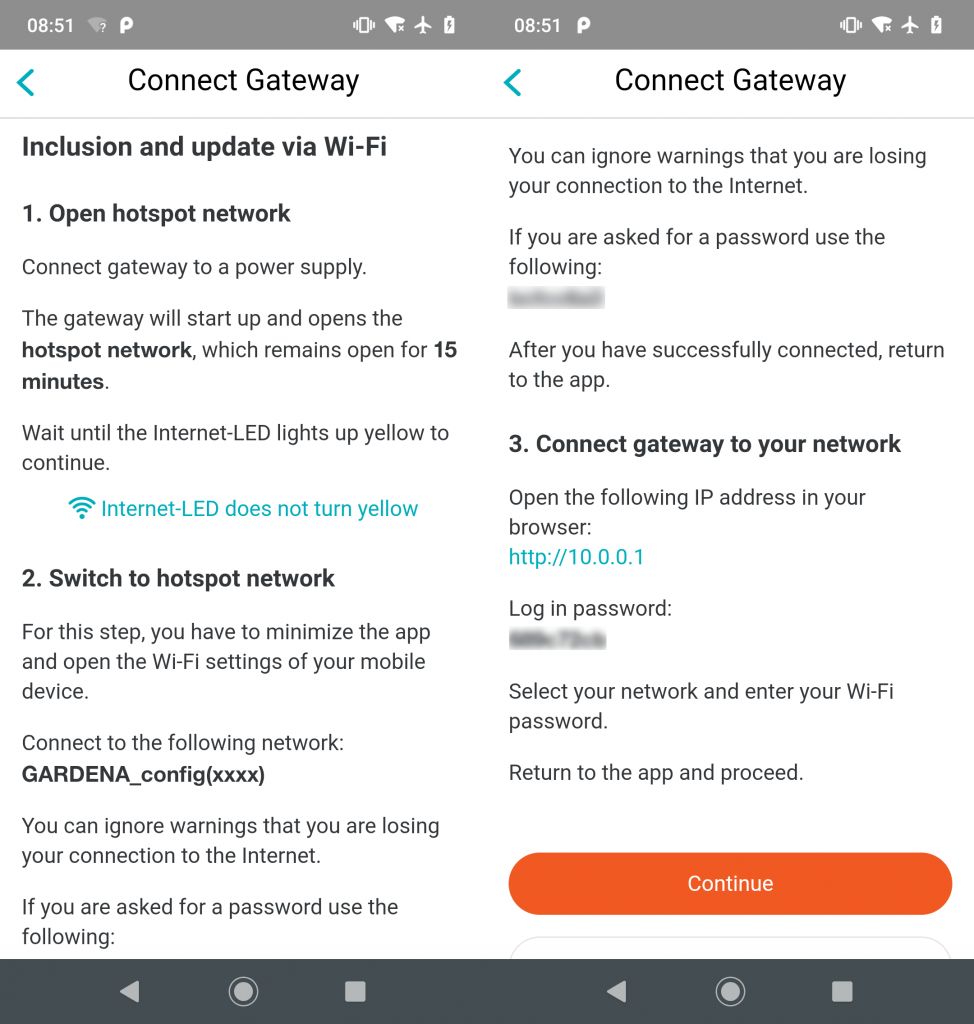
Certainly, the risk for the user of being spied on during setup is low – especially since the WiFi hotspot remains open for a maximum of 15 minutes unless further configuration is made. However, Gardena has taken no further precautions to protect the user in this respect.
Online communication
After startup, the Gardena smart Gateway establishes a VPN connection to seluxit.com, a Danish IoT service provider. The transmission is therefore effectively encrypted at all times.
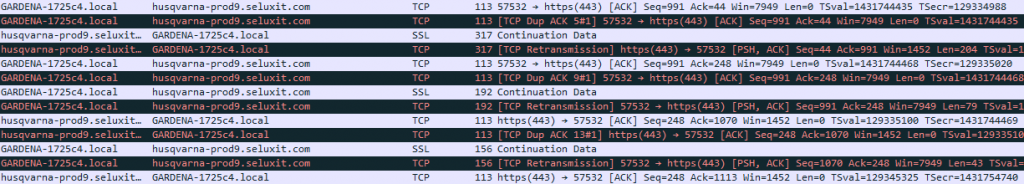
The corresponding app (Android, iOS) always communicates TLS1.2 encrypted. The main communication takes place to subdomains of husqvarnagroup.net. Trackers are also contacted, they receive further attention in the privacy section. The gateway can also be controlled via https://smart.gardena.com.
App
During the analysis of the Gardena smart app, it was noticed that it consists to a large extent only of a web wrapper, in other words the simple display of the Gardena website. Furthermore notifications and trackers are integrated.
Website certificates are correctly validated by the app, but the implementation of certificate pinning was omitted. In older Android versions, an attacker could therefore spy out connections if he could install a certificate on the user’s device. However, this requires access to the device and thus still offers the attacker other, potentially more interesting targets.
Firmware
Before registering with the Husqvarna account, the Gardena smart Gateway downloads a firmware update.
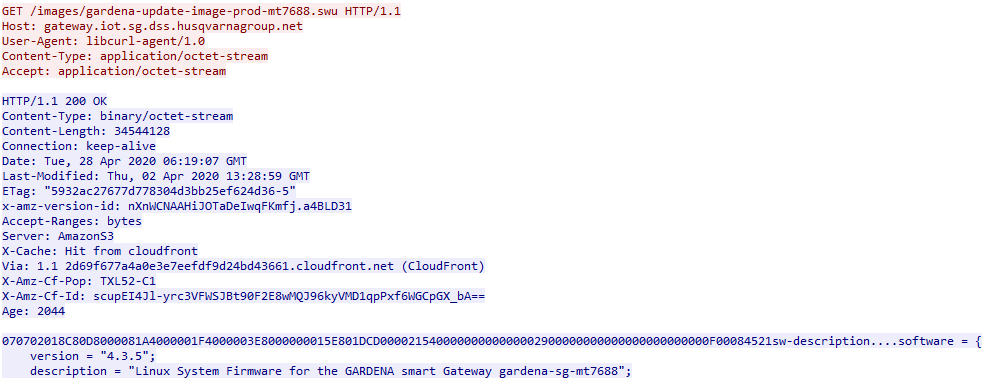
However, this is done via an unencrypted channel. Furthermore, the firmware update itself is unencrypted and reveals some information. Some parts are already known, because Gardena and Husqvarna have been disclosing the used open source components for quite some time now, furthermore they offer the possibility to compile the firmware of the gateway by yourself – even if this is accompanied by the loss of warranty.
The firmware is based on Yocto, an OpenWRT-compatible Linux system for the embedded sector. A package manager is also included in the firmware used by Gardena, so that further packages/applications can be downloaded relatively easily once access has been gained. Furthermore, OpenVPN and Dropbear (SSH server) are preinstalled.
A Github project was looking into reverse engineering of the devices and came across an SSH backdoor of the manufacturer, who according to this information gets access to the gateway via the VPN connection. Although we were able to find the identical SSH key in the firmware update, we can neither confirm nor deny this statement due to the lack of SSH server configuration. A permanently active SSH backdoor would not only allow attackers to access the Gardena smart gateways when accessing the manufacturer’s cloud. The pre-installed package manager could be used to install other tools and thus infiltrate the customer’s network. In order to counteract such cases, we would rather recommend that IoT devices are connected via a separate home network so that other devices are not affected. The manufacturer is advised to activate such accesses (if present) only after manual approval by the user.
Privacy
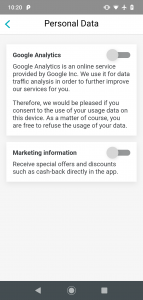
As already mentioned in the online communication section, the app communicates with Microsoft Appcenter, a tracker for usage and crash analysis. Furthermore, Google Analytics is integrated into the website displayed by the app, but can be deactivated in the settings, including the marketing data usage. The data collected by Google Analytics is explained very well in the privacy policy, furthermore the data is anonymized. However, we are missing an indication of which data is collected by Microsoft Appcenter.
Data is processed mainly in Germany and Ireland. If a transfer to other countries is necessary (e.g. for Google Analytics), an adequate level of protection is ensured. During setup, the location of the gateway can be entered. This is used exclusively for weather queries and anonymously for statistical purposes.
Conclusion
As part of this security test, we took a closer look at the Gardena smart system. The solution, which can be controlled via cloud, establishes a VPN connection to the manufacturer and is therefore permanently encrypted. Gardena also earns many points in the app and privacy area. Gardena should bring the setup of the gateway via WiFi up to the state of the art. Until then, we recommend that customers set up the product via Ethernet cable.
The actual security of the system is weakened by the unencrypted downloading of the firmware update. Of course, the download is carried out from the base, from the home network – but you should not always rely on the security of the home network.

