The Xiaomi Mi Band 2 is, like its predecessors Mi Band 1 and 1s, in the entry-level market, but still offers many possibilities. Whether security or privacy was also saved here, we examined within the scope of our fitness tracker tests.
Local communication
After charging, the Mi Band 2 can be paired with the corresponding app “Mi Fit”. A short press on the display is required for pairing. The app then performs a firmware update on the Mi Band 2. After installing the update, it is no longer visible to other Bluetooth devices, connection attempts to its Bluetooth MAC address fail. This feature was introduced at the end of 2017 and is marked as “Discoverable on/off” in the settings. If the Mi Band 2 is switched back to visible, it will also accept connections from any device. Since the Bluetooth services have a meaningful name and data can be accessed unencrypted, it would be easy for third parties to read the data. The default setting should therefore be left as it is.
Online communication
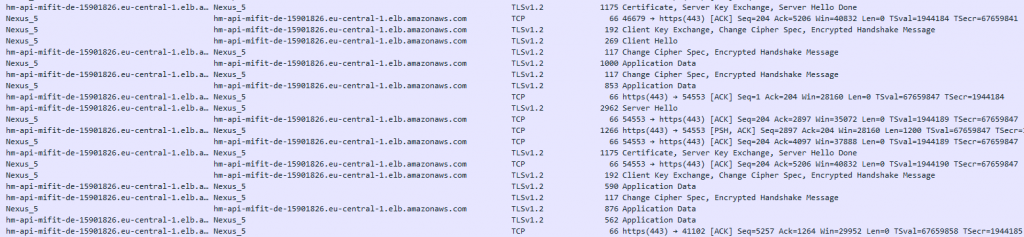
The Mi Fit app from Xiaomi always communicates TLS1.2 encrypted with Amazon AWS hosts, mainly in the EU, but occasionally also in the USA. The encryption used prevents simple man-in-the-middle attacks, but they have not been completely prevented. Since no certificate pinning is implemented in the app, a man-in-the-middle attack could be successful if the attacker can install a CA certificate on the user’s device. However, this would require direct access to the smartphone, which is why we do not rate this negatively.
App
The Xiaomi Mi Fit app version 3.1.6 is obfuscated, making it difficult for attackers to reverse-engineer its functionality. Furthermore, 2-factor authentication via the “Xiaomi Authenticator” app is integrated. Apart from Apple, Xiaomi is the only vendor in our test that has implemented this security feature.
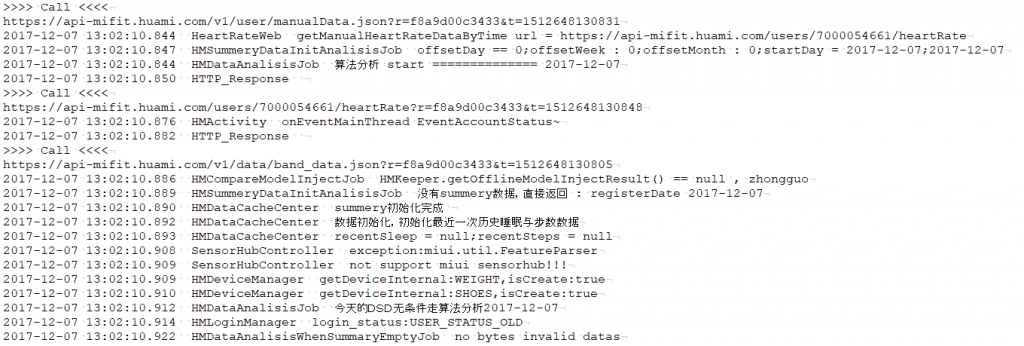
In the appdata folder, a protected area to which only the respective app has access, a detailed log including a relatively easy to read description of the API is written. However, this is only dangerous on rooted devices, which is why this is not considered negatively in the evaluation.
However, the functionality of the app can also be simulated using this protocol. Other developers certainly take advantage of this.
Privacy
The Xiaomi Mi Fit app contains a privacy policy of Huami, a Xiaomi subsidiary. On the Google Play Store, however, a privacy policy for Xiaomi’s Mi Fit program has been linked.
In our test, we focused on the app’s privacy policy and recommend that the manufacturer urgently changes the link in the Google Play Store.
It is easy to understand and available in several languages. Furthermore, it is updated for the GDPR. The recorded data is broken down in great detail. Personal data is used, for example, for target group-oriented advertising.
With the manufacturer’s app itself, pure offline use without data synchronization is not possible. However, there are some third-party apps that offer this.
Conclusion
The Xiaomi Mi Band 2 is a fitness tracker for beginners, which in our test came up with unencrypted Bluetooth communication, but always encrypted Internet communication. Bluetooth communication is invisible from other devices by default, but we would still like encrypted communication and secure authentication. With regard to privacy, Xiaomi processes a lot of data via the fitness tracker, which is also used for advertising purposes, among other things.


Pingback: Which Android app phones home to China? - Is it Mi Fit?
Pingback: Mi Band 2 - Mi Fit - Apps On Google Play
Pingback: Mi Band 1 - Mi Fit - Apps On Google Play