As part of our large fitness tracker test, we took a selection of popular candidates from this product category under close examination and analysed how good security and data protection really are. The first representative we use for testing is Fitbit’s popular Charge HR. The following test report is intended to clarify how securely protected the customer data is against potential attackers and general security problems by one of the best-known manufacturers in this area.
Application Security
With the mobile application (tested version 2.63) Fitbit, as usual, does not allow itself any notable weaknesses: The source code is cleanly obfuscated, which makes reverse engineering much more difficult for less experienced attackers. No sensitive information, such as passwords, certificates or the like, is hard coded, and certificate validation for securing communication between the app and the cloud also seems to be neatly implemented. Furthermore, we could not detect any unsecured storage of any sensitive data on the smartphone – the secured app storage, for example, contains data for the authentication, so that a theoretical danger on rooted devices cannot be ruled out, but this fact can hardly be assessed as a weak point. The application does not output any relevant information potentially usable for an attacker on any other channel, such as the Android logcat, so no reason for criticism here either.
Local Communication
The direct communication between tracker and smartphone is also implemented here as usual via Bluetooth Low Energy. Especially important in this field is an adequate user authentication and encryption as an additional security layer for the transmitted data. In this way it can be practically ensured that recorded user data is not read or manipulated on this transmission path. The Fitbit Charge HR is particularly exemplary in this respect: a clean authentication ensures that a potential attacker cannot establish a Bluetooth connection with the device and can thus request sensitive data. But even if the communication would still be intercepted (which is of course always possible with a radio connection), the data transmitted is also securely encrypted and thus adequately protected in the majority of possible attack scenarios. In the test, we did not notice any significant weak points in regards to local communication.
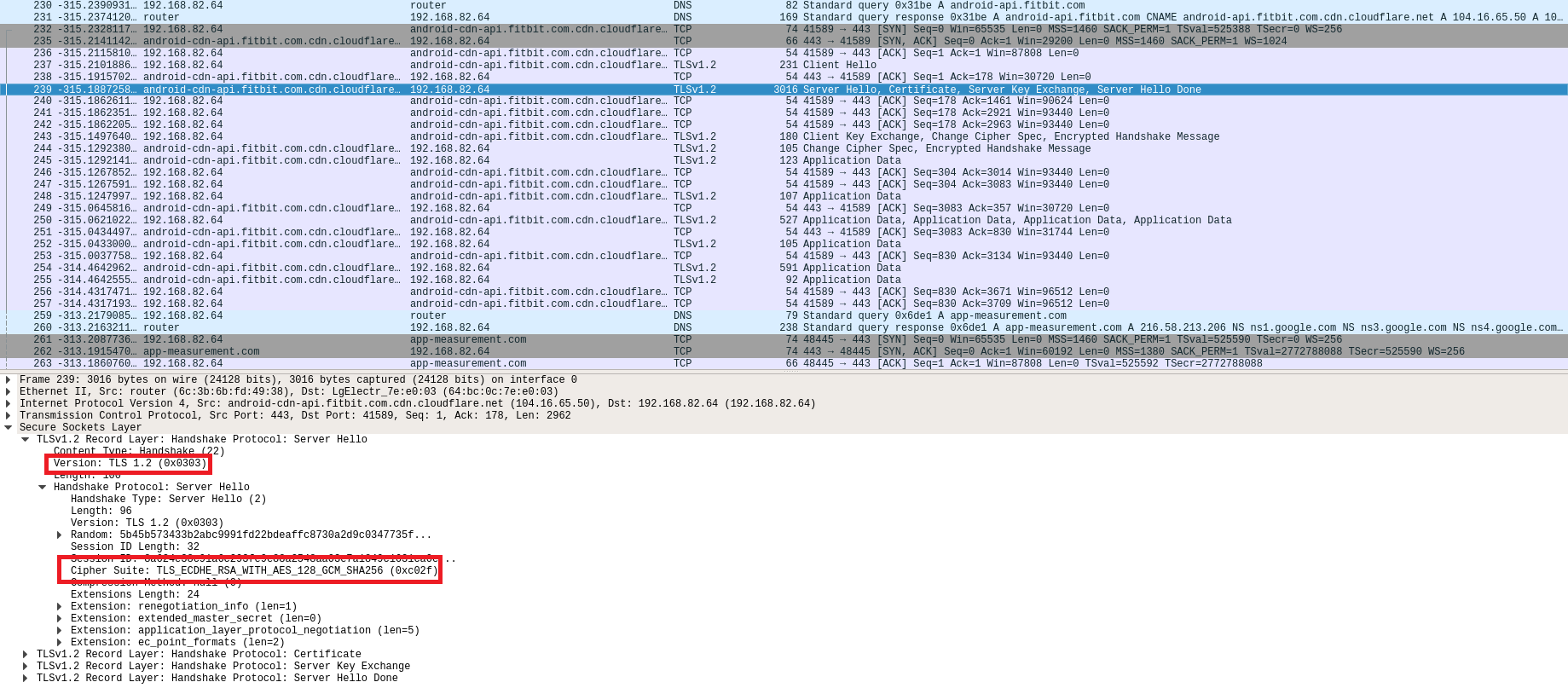
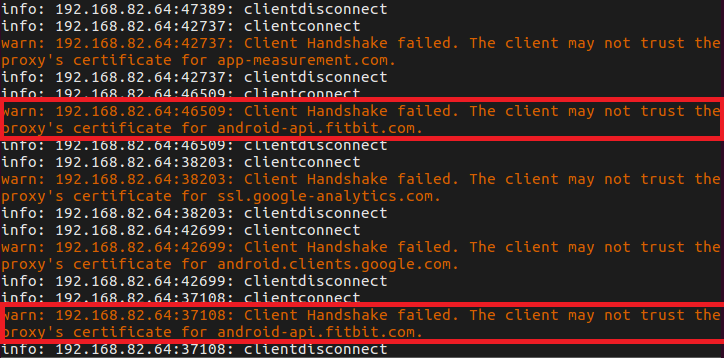
Online Communication
Fitbit also does not allow itself any real weaknesses in the field of online communication and confirms its solid impression. In the test we could not find any obvious weaknesses either – all outgoing and incoming connections, including registration, login and synchronization, were encrypted exclusively with current standards. Even our standard tests for the possibility of man-in-the-middle attacks did not provide any indication of possible vulnerabilities at this point. Good job!
Data Privacy
Fitbit’s privacy policy is well structured and explains easily understandable what data is recorded by Fitbit and what happens to the recorded data. Personal data will not be shared with third parties. However, data that cannot identify the user may be shared with third parties for statistical purposes, for example. Data is also processed in the USA, but this is based on the EU-US privacy shield and thus also on a high level of data protection.
Verdict
After we pointed out some serious vulnerabilities (among other things regarding missing authentication and encryption) to Fitbit in our very first test in 2015 and helped to eliminate the problems, the security level had already reached a very good level at that time. However, nothing has changed in a negative direction up to this test: The concept is still well designed and implemented, the most important security aspects are adequately covered and Fitbit does not have to expose itself to any criticism from a data protection point of view. No real weaknesses and therefore a full 3-star rating!

