Moov, based in the USA, sells a very lightweight fitness tracker weighing 15.1 grams under the product name Moov Now. It is not designed as an everyday pedometer, but mainly for sports activities.

Local communication
The link between the smartphone and Moov Now is established by pressing the tracker. After a short authentication process, the fitness tracker is ready for use. According to our findings, the device itself consists of a gyroscope whose data are sent to the app via Bluetooth and analyzed there. This also explains the small, light design of the device.
After authentication, the app receives the real-time data from the gyroscope via a notification service and analyzes it, calculating the number of steps, for example.
The authentication process used is static and can be simulated relatively easily. This would allow attackers to record the gyroscope data with simple means. However, the attack scenario is mitigated by the fact that this data would then also have to be processed accordingly by the attacker. Furthermore, the point in time at which the owner of the device activates a training by pressing the tracker would have to be adjusted.
Online communication
The communication between the Moov app and the cloud was always TLS1.2 encrypted and thus protected against simple man-in-the-middle attacks. Also, the registration and the firmware update were identically encrypted.
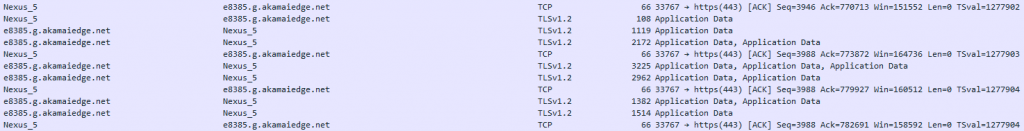
After installing a CA certificate, the communication can be eavesdropped on and manipulated by a man-in-the-middle attack. However, this requires direct access to the device, which is why this point is not rated negatively. A session key is generated for communication between the app and the cloud (X-Moov API session), which is then used to authenticate each data transfer to the cloud.
App
The Moov Android app (version 5.0.2548) is partially obfuscated, making reconstruction of the app more difficult.
An implementation of certificate pinning is recommended to prevent man-in-the-middle attacks. Furthermore, it is recommended to check the implementation of third-party modules, as the implemented Baidu module contains vulnerabilities according to static analysis.
During operation, the app generates a protocol which also contains the above-mentioned session key in plain text. However, since this is located in the protected app area and can therefore only be read on rooted smartphones, this does not lead to a devaluation.
Privacy
Moov’s privacy policy provides information about the recorded data, but leaves some questions unanswered. For example, it is unclear whether data designated as “non-Identifiable data” will be disclosed in anonymous form. Since this also includes localization information, it is doubted that this information cannot be used for identification.
Data processing takes place in the USA, but information about exactly what data is collected by the fitness tracker is missing. According to the privacy policy, however, data will not be sold.
Conclusion
With regard to Bluetooth communication between Moov Now and the associated app, there are attack possibilities, which, however, probably have only a low damage potential. The online communication was encrypted at all times, furthermore a sale of data is clearly excluded by the privacy policy. The general level of security and privacy is therefore rated with two stars.

