Smart gadgets with tracking functions are still in high demand. Not only for (over)concerned parents, but increasingly also when it comes to keeping an eye on elderly people and those in need of care. Back in 2019, we looked at a kids smartwatch (SMA-WATCH-M2) in an initiative test that was supposed to serve the same purpose. Our verdict back then was rightly devastating and ultimately led to a sales stop in Germany. As part of our quick check, we thought it was time to pick out a device from this category and take a closer look at it. We chose the Watch Air from the Dutch manufacturer Spotter. The following review will clarify whether test results were equally devasting to that from 2019. But right away: It will not be quite as scary this time.
Features
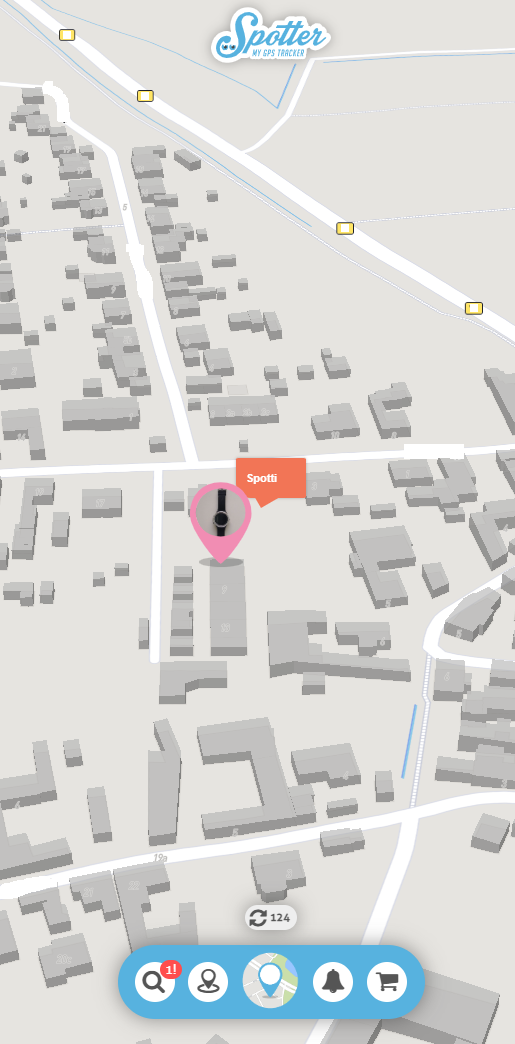
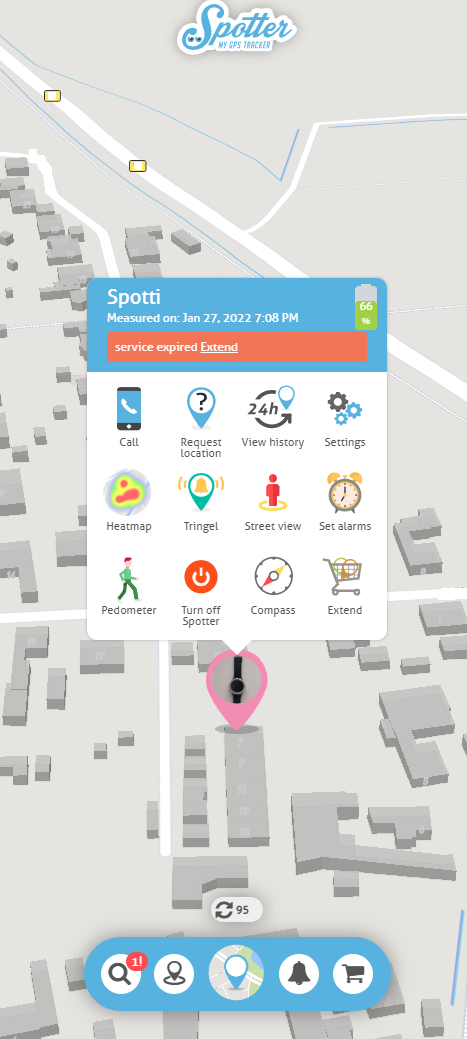
In terms of features, the Spotter watch basically offers everything you would expect here: GPS tracking, geo-fencing, call function, pedometer, an SOS alarm and alarm functions are of course integrated. These features are housed in an IP67-certified, water- and dust-proof casing – so it is completely sufficient for the intended user group. The device also comes with an inserted SIM card and service for one month after registration. What upset us a bit from the user’s point of view was the fact that the watch practically cannot be operated with another SIM – or better: it would not make sense. There is nothing to prevent users from using their own SIM, but if they want to use the watch’s tracking function, they have to pay for a seperate Spotter service anyway. Most other providers that we have tested so far provied this feature without additional costs. However, this point is of course irrelevant from a security point of view.
Applications
The apps on Android and iOS provided the first surprise in the test: Our automated, static analysis rates both apps with scores of 70%. That does not sound overwhelming at first, but compared to the average results we get here, it is actually a very good value. The static analysis normally finds a lot of theoretical vulnerabilities even in practically secure applications, which can be exploited in the rarest cases and scenarios, but still often push the overall score (often far) below 50%. So, on paper, spotter applications offer comparatively little theoretical attack potential. Theoretically.
But if you take a closer look at the applications, it quickly becomes clear where the supposedly good result comes from. The static analysis examines the decompiled source code (or the bytecode itself) of the applications and looks for known and potential vulnerabilities in the implemented methods and functions. So far, so normal. However, in the case of the Spotter app, the app source code itself only serves as a wrapper for an implementation in JavaScript, which is attached to the applications assets and contains the actual functionality. The source code examined in the static analysis therefore has virtually no functionality and thus, virtually no vulnerabilities.
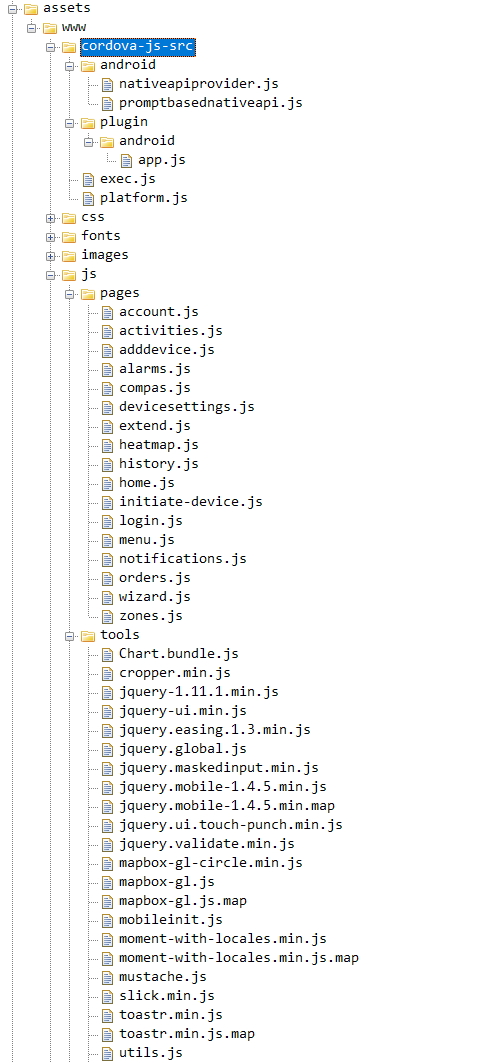
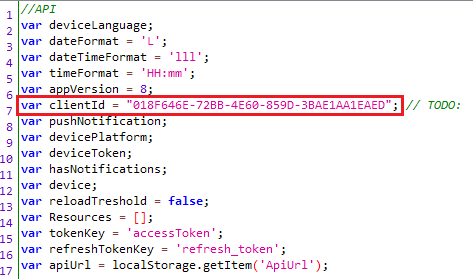
The implementation via JavaScript in attached scripts has the advantage for the developer that the implementation for Android, iOS and browsers is completely identical and only the corresponding wrapper has to be adapted. From a security point of view, however, the whole thing has a few catches. Above all, reverse engineering is made immensely easier. Where decompilation normally only provides a reasonably good and rarely complete representation of the code, which is often difficult to read by humans due to code obfuscation, the original code is available here – complete, without obfuscation and even commented. This means that the entire communication and Web API can be conveniently traced and searched for potential vulnerabilities. Functions and classes that implement and configure communication security, such as the trust manager required for certificate validation under Android, are of course also not implemented in this way. The practical consequences will be explained in the next section.
![]()
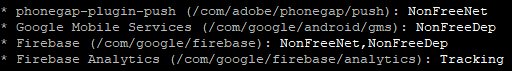
Apart from that, there is not much interesting to report about the static analysis of the applications: The applications’ permissions are appropriate for the intended functionality, and there are no indications for excessive data collection in terms of trackers. Only Google’s Firebase Analytics module is included as a tracker with an entry in the Exodus Privacy database.
Communication
The Spotter Watch Air itself does not have WiFi capabilities and accordingly communicates exclusively via cellular. There is not much more to report about this in terms of security. It is generally known that communication via mobile networks cannot be considered attack-proof, and we already mentioned that there are some attack scenarios especially for the use of these devices with children (caller/number spoofing, for example) in our first kids’ watch review in 2019. This does not change for the Spotter Watch Air. However, the problem is due to the nature of the matter and cannot be held against the product itself.
What we can evaluate, however, is the communication that takes place between the associated apps and the manufacturer’s online services. And there is one big problem in particular that runs through the entire communication: It can be virtually read in its entirety. Whereas we can now hardly observe the old classic problem of completely unencrypted communication in the IoT, we now repeatedly encounter the new classic of completely encrypted, but easily breakable communication. For example, all processes, including authentication, device localization and user details, can be read, manipulated or replayed by a simple man-in-the-middle attack in the Spotter applications – adequate certificate validation when establishing a connection to the server does not take place and using the applications in a public WLAN is therefore absolutely not recommended. The manufacturer should urgently try to improve this, even if we are not sure that this is easily possible in the current, unconventional implementation.
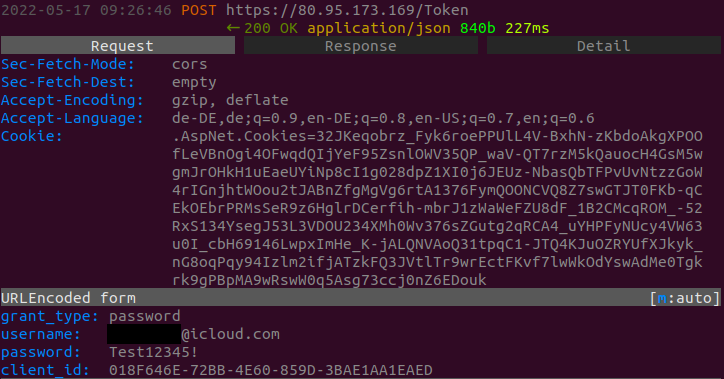
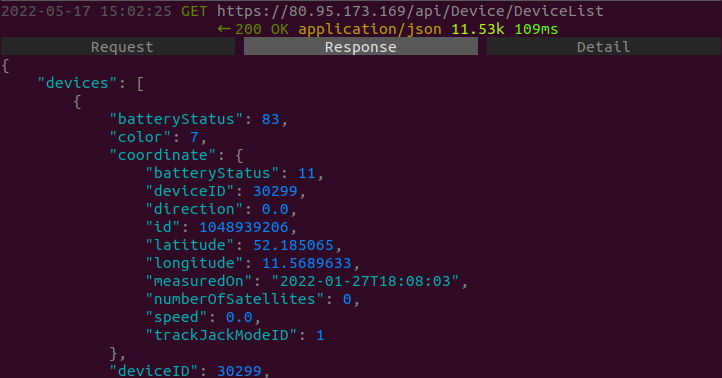
As part of the quick check, we also took a look at the web API to check whether there are more potential vulnerabilities hidden here that might allow access to user data or other devices and user accounts. Due to the narrow scope of the Quick Check, we did not go into depth here, but we did look at the functions that the apps also use to retrieve information about users or devices. In the case of unsecured APIs, it is often possible to gain access to data or functions that are actually outside the user’s own rights by simply manipulating device and user IDs in the corresponding requests, for example. However, we can give the all-clear insofar as we did not encounter any obvious problems. Here and there, we noticed a few peculiarities, but in none of the cases were they to be seen as a direct problem. For example, the user ID, which is transmitted together with email and password in the login request, is hard-coded and therefore the same for all users. However, it can also be omitted during login and is accordingly not checked on the server side anyway – at least strange.
In addition, when we sent a localization request to the server for a guessed device ID, we always only got back “Device not found!” and not “Access denied!”. So we can’t be sure if we just guessed in the wrong ID range or if we were actually denied access. Unfortunately, we only had one copy available in the test, so we could not test using two guaranteed valid IDs. Apart from a few clues, we could not find anything overly suspcious – at least not after a quick check.
Data protection and privacy
In the area of data protection and privacy, however, there is pleasantly little to report. As already mentioned, the applications do not contain any advertising trackers, and we could not find any indications in the communication that would suggest an inappropriate data collection.
The product’s privacy policy is quite comprehensive and provides sufficiently detailed information about all important points regarding data collection, storage and processing. The included Google analytics tracker is also mentioned and its purpose as well as the collected data is explained. Of course, there is always room for improvement in detail, especially in this area, but overall we did not see any reason for serious criticism here.
Verdict
As announced in the introduction, our verdict on the Spotter Watch Air is not quite as devastating as in our last review of a comparable product. However, the fact that the entire communication from and to the mobile application can be intercepted and manipulated does not allow more than 1 out of 3 possible stars overall. And this is only because the product is solid in terms of data protection.

