If a fitness tracker is marketed under the name of the electronics giant Nokia, and it is also part of an entire health and fitness range, this is reason enough for us to once again take a close look at the Steel HR. In previous tests we already had products of the manufacturer Withings, which will soon appear again as a separate brand from Nokia, and we can therefore make comparisons and assess the security technology development again at this point. The following report should show to what extent something has changed there.
Application Security
The static analysis of the mobile application (com.withings.wiscale2; tested version 3.5.3) provided a relatively long list of possible vulnerabilities and problems in the first step of the analysis. The Nokia app is mainly suspected of weaknesses in the implementation of SSL-protected connections – there are indications that some important certificate information (such as the CN – Common Name) is not checked during certificate validation and thus provides a target for man-in-the-middle attacks with specifically forged certificates. These assumptions were then verified in practical tests.
Apart from this, the application makes a solid impression: The source code is obscured by an adequate obfuscation, sensitive information is only stored in the Android-secured app memory areas and no other obvious potential sources of information for possible attackers arose during the investigation.
Local Communication
The communication between Nokia tracker and the application runs via Bluetooth LE in this case as well. Particularly important for us in this point is that the communication takes place encrypted and in any case an authentication is carried out before any data is transmitted via this channel. In both points, the application does not appear completely sovereign. Although both encryption and authentication are implemented, there are places in both points where we suspect at least a theoretical vulnerability. This enabled us to reconstruct certain parts of the communication that do not appear to be completely encrypted. In the test, however, we were unable to identify a direct way of exploiting this circumstance. Sensitive data could also not be read out in this way, so that no devaluation would occur in this case. The use of the Bluetooth LE privacy features, which are intended to prevent 3rd party tracking of the device (for example by dynamically changing the Bluetooth MAC), also delivers a positive impression and is still not standard for all tested devices.
Online Communication
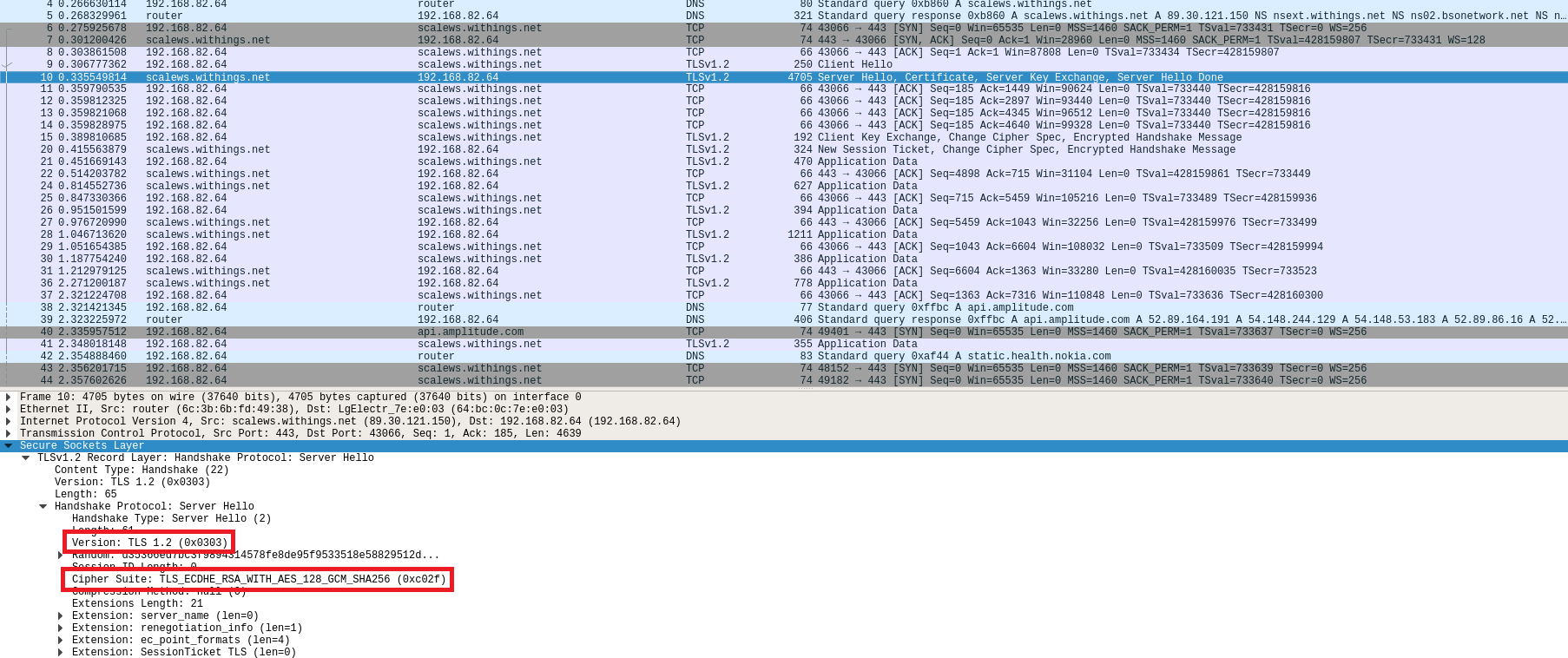
In the practical tests, the Steel HR and the associated application prove to be quite solid. The absolute majority of the observed connections are adequately secured by TLS 1.2 and even our standard man-in-the-middle attacks could not identify an obvious vulnerability, even if the results collected in the static analysis suggest at least theoretical points of attack in the certificate validation – however, these could not be confirmed.
What is relatively noticeable are the many connections for the purpose of analytics and user behaviour recording. Data is transmitted to Google Analytics, Amplitude and AppsFlyer, but not in all cases via HTTPS but at least always concealed.
Data Privacy
Due to the new GDPR, we have again reviewed the data privacy statements as part of our fitness tracker test. As a rule, they were much more detailed. Unfortunately, this is not the case with Nokia. For example, the last data protection declaration dated June 20 2017 still contains information about the purpose for which data is collected. This is no longer the case in the current version of May 24 2018. We suspect that this is an inadvertent mistake – in our opinion, the previous privacy statement was exemplary, as can be seen in the other blog posts on Nokia Health products, e.g. in the post regarding the Nokia BPM+.
Verdict
The Nokia or Withings Steel HR and its application leave a very solid impression. Of course, at least theoretical speculations can be made at some points about possible weak points, but the practical security level of this product can still be classified as high. We consider the apparently relatively extensive collection of information on user behaviour, for example, to be at least questionable and would like to question the necessity of it. Nevertheless, the points listed do not justify a devaluation in one of the relevant security areas and the Nokia Steel HR can therefore be awarded the full 3-star rating.

