Let’s dive into another round of the Quick Check. This time, we’ve taken a look at the most affordable IP camera on Amazon, the A9 Camera. Priced at under 10 euros, it sits at the lowest end of the IP camera price spectrum. But does one also get the security that every IoT product should have for this price?

Features
The A9 Battery IP Camera is distributed by SALUCIA and is available for under 10 euros. It represents a cost-effective solution for security monitoring. With HD quality, night vision, motion detection, and easy installation, it is versatile in its application. The camera allows recording on a microSD card or real-time monitoring via an app, and it proves effective even in low-light conditions. The integrated motion detection feature and the magnetic mounting mechanism complete its profile, providing an affordable solution for surveillance needs.
Mobile applications
In accordance with our standard Quick-Check procedure, the mobile application V720 (com.naxclow.v720 in the tested version 2.1.6 for Android) underwent a static analysis.
The procurement of the app did not proceed without difficulties. Despite multiple attempts, we encountered the message “This app is not available” on various smartphones when attempting to download it from the Play Store. Interestingly, we found the app effortlessly through the PC on the Play Store, where it is actively maintained as well – the latest update was done on July 31, 2023.
The user manual exclusively lists this app as the recommended choice for camera usage. In order to remain consistent with our approach according to the manual, we downloaded the APK file for the app from apkpure and ensured that it is the identical version.
Our static analysis revealed concerning aspects regarding the app. It allows unencrypted communication, which could potentially lead to the exposure of confidential data if implemented improperly – a topic we will delve into further in the “Local and online communication” section. Additionally, we encountered app permissions whose purpose within the app seems questionable.
Within these permissions, the initial one is GET_TASKS, which furnishes details regarding active and recently utilized applications. Equally troubling is the READ_PHONE_STATE permission, granting access to phone numbers, serial numbers, and even phone numbers from ongoing calls. Lastly, the permissions BIOMETRIC and AD_ID are notable. We couldn’t discern a definite use of biometric data, and with respect to Ad_Id, it’s always prudent to exercise caution as their intended purposes warrant careful consideration.
During our analysis, we detected 4 trackers:
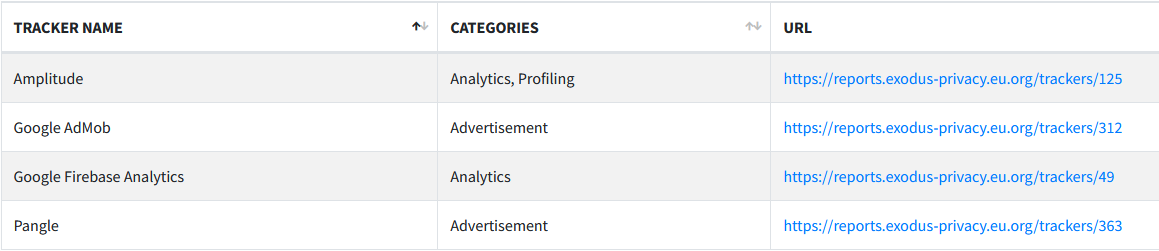
As is now customary, we see Google Firebase Analytics here, which is present in almost every app nowadays and monitors the behavior as well as crashes of the app. In the advertising realm, we find Google AdMob and Pangle, which provide the advertising displayed within the app. Lastly, we encounter Amplitude, which analyzes the behavior of the app user – a practice that is generally regarded with caution.
Local and online communication
The initiation of the online connection occurs in a few simple steps. First, the “Mode” button is pressed until the light flashes rapidly. Subsequently, the configuration of the internet connection is done through the app, followed by a Bluetooth connection. This successfully registers the camera and enables remote access. With this method, communication takes place through a server in Hong Kong. Although the transmission between the app and server, as well as the server and app, seems secure, there are critical points to consider.
Especially, the communication between the server and the camera, as well as the camera and the server, occurs unencrypted in plain text. To ensure comprehensive security, targeted securing of these connections is of paramount importance. While the transmission between the server and the app is encrypted, it should be noted that an additional WebSocket connection always transmits a heartbeat. Since this process is initiated through HTTP, it poses a risk as HTTP is an unencrypted protocol. This could allow unauthorized individuals to intercept and read the messages.
At the start of this WebSocket connection, a token is transmitted. This token serves as an authentication method within the app. Authentication enables the server, with which the app communicates, to ensure that it is indeed the current smartphone sending messages through this app. This token is requested from the server during the app’s installation and remains unchanged thereafter.
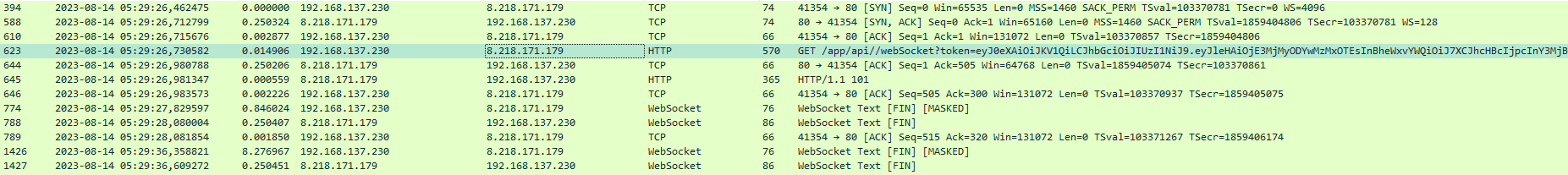
If unauthorized individuals manage to extract this token, they could send messages to the server and impersonate the app’s user. This would allow them to access information about all devices connected to the app. As the example illustrates, a device was identified, displaying both its type and serial number.
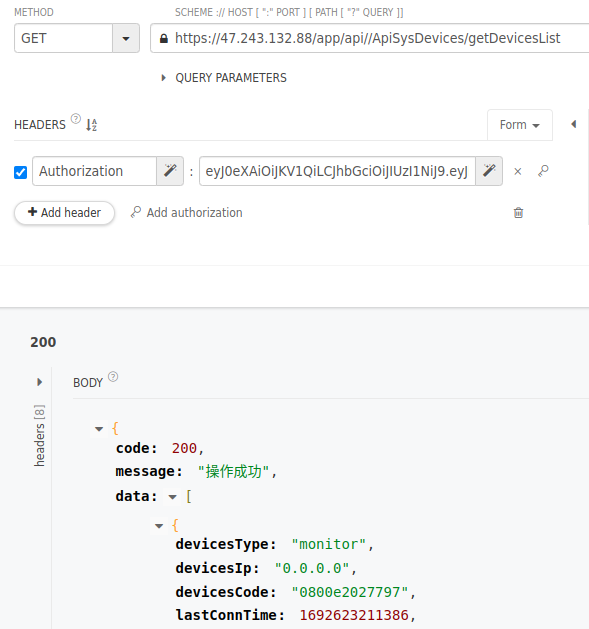
By using the token and the newly obtained serial number, the connection parameters of the video transmission can be queried. This enables an unauthorized person to view the live camera feed without the owner being aware of it.
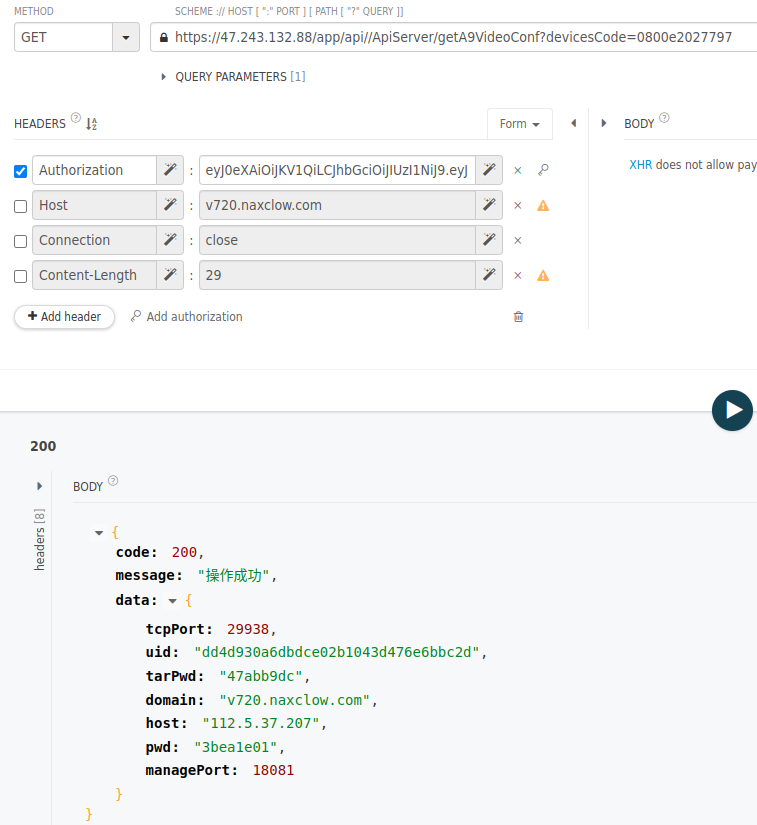
Finally, there is also the option to change the camera’s password.
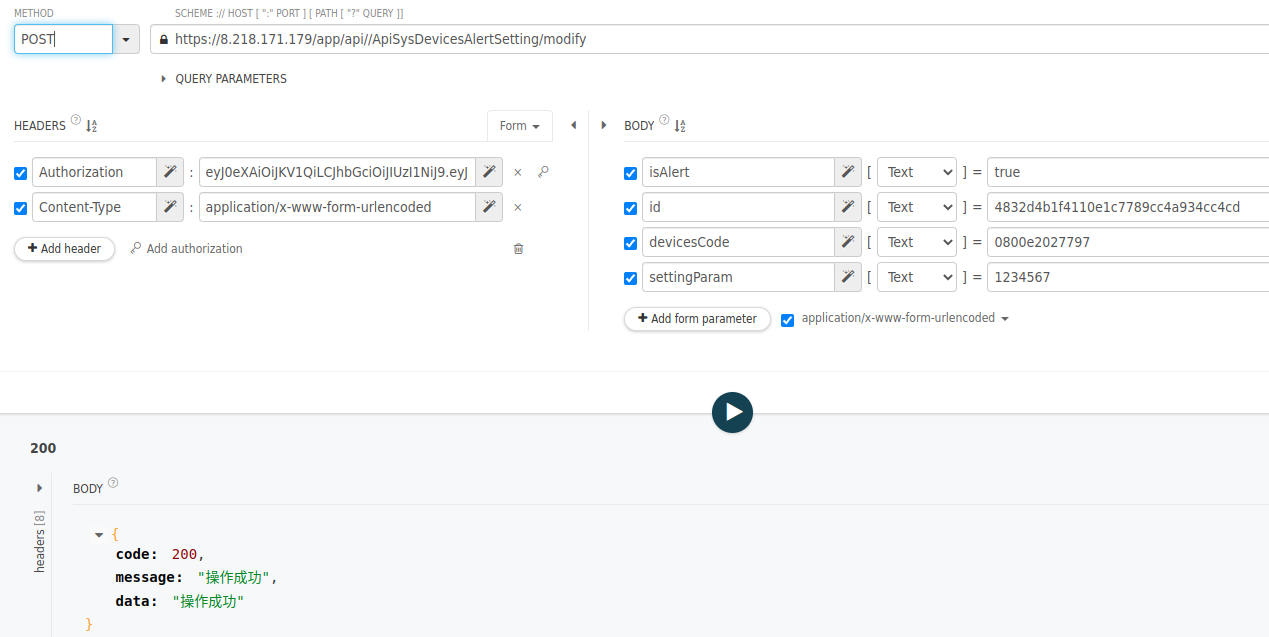
The app itself is not protected with a password and only offers the user the option to individually secure each camera with a password. The default password for our tested camera was blank, and we were not prompted to set one. You have to activate the password protection under settings. Then you can set a 6-digit password, which, however, consists only of numbers and is therefore susceptible to being determined through brute force. What’s concerning is also that through our previously demonstrated query, the password can be changed without requiring the old password. Additionally, with this query, the app’s 6-character limit for passwords no longer applies, allowing longer passwords to be set than in the app. This implies that it would be technically feasible to implement stronger password protection, but the app hinders this process.
The challenges continue during video transmission. In this case, a UDP stream is used, and the transmitted data is unencrypted. This makes the transmission vulnerable to basic sniffing attacks, where attackers capture network traffic using tools like Wireshark. As a result, unauthorized individuals could potentially gain insights into the video stream. Those seeking more detailed information about the format can find further information in the mentioned GitHub project related to the camera.
Against the backdrop of these significant vulnerabilities, it is advisable not to use the app on public networks.
In addition to conventional online communication, the camera offers a second option: the AP mode, which enables local operation. By pressing the “Mode” button again and the rapid blinking sequence lights up, the camera starts a hotspot. Through this, users can connect to the app and use the camera locally without the server. Another aspect is that pressing the “Mode” button also serves as a reset function, which results in logging out from all apps where the camera is registered. Therefore, it is essential to protect the camera from direct access to prevent potential takeovers by attackers.
For those who have concerns due to the mentioned risks or who do not fully trust the server in Hong Kong, there are alternatives. One option is to use the GitHub project “a9-v720” by intx82 to connect directly with the camera. Alternatively, with the help of the project, you can set up your own server to maintain complete control over the communication.
Overall, it can be concluded that the unencrypted video stream and the transmission of an important token in plain text label the overall communication as insecure.
Data protection and privacy
Within the scope of the Quick Checks, our goal was to review the privacy policy. Unfortunately, we found that when attempting to access it, we encountered a “404 Not Found” error message both in the Google Play Store, the App Store, and within the app itself. As a result, an analysis of the privacy policy was not possible.
Verdict
As a camera within the local network, the AP Battery IP Camera is a great and cost-effective solution. However, due to the mentioned deficiencies in online communication, I would not use it over the internet, or only with a self-set up server and thus a personally adjusted security level. In summary, there are issues in all three categories, whether they are the trackers for behavioral analysis, online communication problems, or the absence of a privacy policy. Therefore, as it stands, we cannot give any stars to the device.

