Another product from the Smart Home category was tested in our certification process for its security in the areas of online/local communication, application security and privacy – the LUPUSEC XT1+ Security Kit. In the following, we will explain why it has truly earned the certificate “Approved Smart Home Product”.
Application
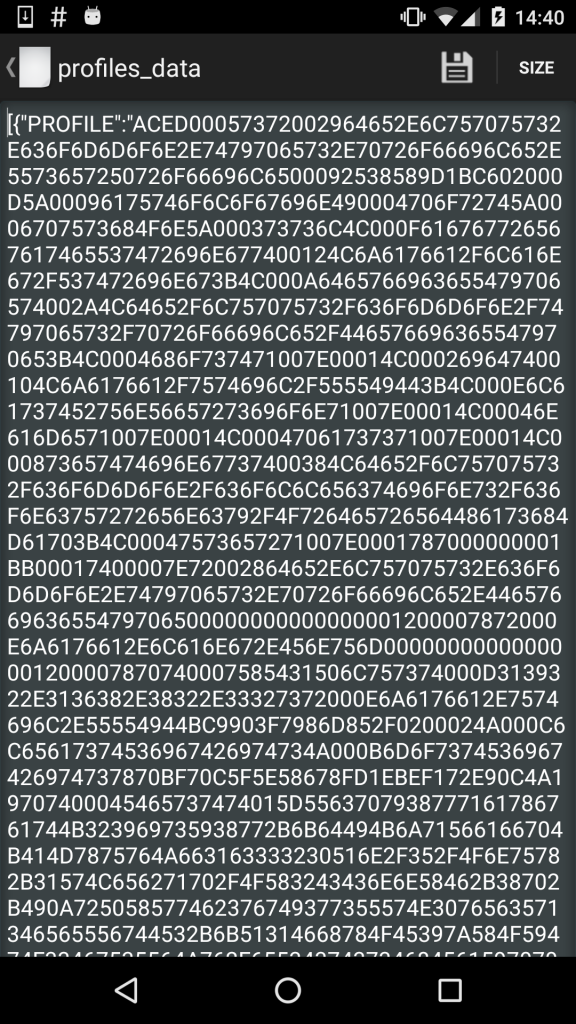
For testing purposes, we took a look at the latest BETA versions of the Android and iOS applications (Android v3.0.0.1407 & iOS v3.0.0.7) provided by the manufacturer Lupus-Electronics. Naturally, we analyze the Android version in much more detail, since Android, as a less restrictive operating system, offers a larger attack surface. In the case of the LUPUSEC Android application, however, we could not identify any serious vulnerabilities: The source code is protected by obfuscation, which makes reverse engineering of potentially security-relevant functions much more difficult. The user data, which is stored locally on the smartphone, is completely encrypted and is therefore adequately protected against access by unauthorized third party applications even on smartphones with root rights. Furthermore, the implementations of critical functions, for example for encrypted communication, do not seem to have any programming weaknesses that could easily be exploited. All in all a very solid presentation!
Local Communication
In the area of local communication, i.e. communication between app and base via the local WiFi, for example, no serious problems could be identified either – sensitive communication only runs encrypted and adequately protected against possible man-in-the-middle attacks once the system has been fully set up.
Nevertheless, we were able to identify a few minor weaknesses, which are hardly significant overall, but should still be mentioned. Thus, the local access via the web interface is only provided with a device independent password by default. A password change is required from the system during setup, but a short period of time with at least theoretical vulnerability between the first connection and setup still exists.
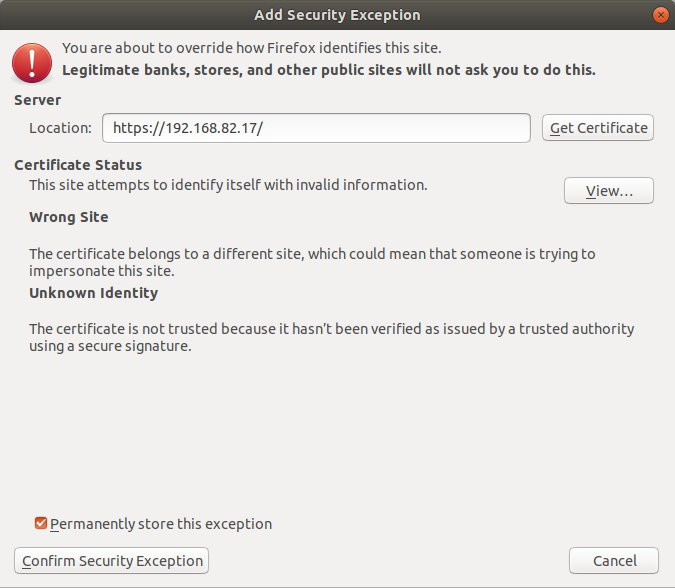
Furthermore, for local access to the base via the web interface, the self-signed certificate must be accepted to secure the connection. The user receives a security warning from all modern browsers, which indicates the potential security risk. Even if the manufacturer’s reasoning is understandable at this point, the technical implementation at this point at least theoretically provides potential for attacks if unneeded users get used to ignoring such security warnings and begin to accept random certificates. However, this circumstance alone does not directly represent a vulnerability per se.
Online Communication
Remote access to the XT1+ system is realized via DynDNS. We do not have anything else to note at this point regarding possible security risks – the communication is completely encrypted and adequately protected against common standard attacks.
During testing the direct communication between XT1+ base and LUPUSEC servers proved to be minimal. It was completely encrypted, but still had a weak point. In the test it was possible to carry out a man-in-the-middle attack on the outgoing connections due to the lack of certificate validation on the part of the base. In the test, however, this circumstance did not prove to be a critical vulnerability, as no sensitive data could be intercepted or manipulated.
Firmware
In this test point, we did not directly examine the source code of the firmware itself for possible weak points, but only the security of the transmission of it via the Internet in the context of possible update processes.
In the current version, the firmware image is transferred in unencrypted form during the update. In order to be able to protect the firmware and the functionality it contains during transmission, the manufacturer has used a digital signature. This signature cannot directly protect against manipulation, but allows the base to check the integrity and authenticity of the image before installation and thus detect possible changes performed during transmission.
Privacy
In the current version, the application contains terms of use, which in turn contain the privacy information: As we suspected and observed during the test, the XT1+ system and app are very cautious in collecting user information: If remote access is used, only device ID, public IP address with port, username, password and email address are stored. And important: No data is shared with third parties. Exemplary!
The activation of online remote access is also optional – if it is deactivated, only the device ID and the public IP of the base are recorded.
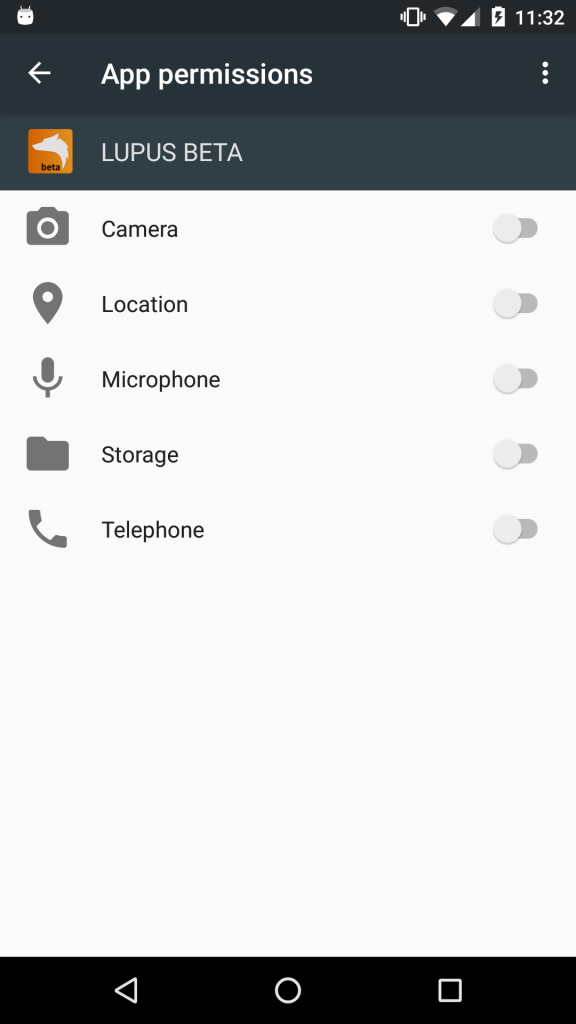
The only additional thing we would have wished for would be a more detailed information on application permissions and their necessity. However, none of the additional permissions were actually used by the application in the test, so that we do not have to raise any further concerns here.
Verdict
All in all, the test showed us a balanced security concept with only a few minor weaknesses. The important areas of local communication, online communication and privacy have been implemented absolutely adequately for the field of application and offer customers a high level of security. In our test, no critical and/or obvious serious weak points were found, so that we can award our certificate “Approved Smart Home Product” to the LUPUSEC XT1+ without hesitation.

