In April/May of this year we have already thoroughly tested the Smart Lock solution Nuki Combo 2.0, from manufacturer Nuki, in our certification tests. Now the Nuki Opener has also successfully gone through this procedure. In the test we examined the opener itself as well as the newest versions of mobile Nuki application and Nuki Bridge. The current versions also convinced our testers in all relevant areas, without providing any reason for serious criticism.
Application
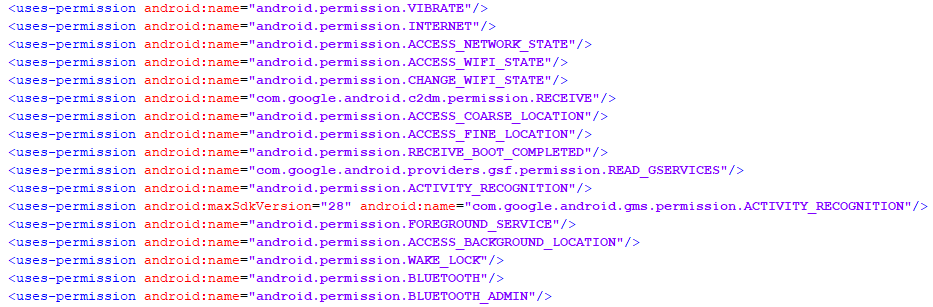
The mobile applications, in the tested versions 2.4.2 (Android) and 2.5.0 (iOS), do not reveal any real weaknesses in both static and dynamic analysis: security-relevant areas, such as the implementation of encrypted communication, including an adequate certificate verification, are implemented correctly and comprehensively – a point that we unfortunately often find different. Also the storage locally on the user smartphone proves to be secured and without the obvious possibility for other potentially malicious applications to access user data. All in all, everything is on a solid security level.
However, there is one point about the actual functionality of the application that we do not like as much, although we can understand the manufacturer’s idea behind it. As we already mentioned in the Nuki Combo test, it is possible to add new users with full rights by default with physical access to the Nuki Bridge, without informing other users and without requiring a password or PIN. The option can be disabled via menu, but is enabled by default. Here we would wish for a PIN query (which in this case would not greatly affect the user experience) or at least a user notification after the bridge was manually operated and a user was added.
Local communication
For the analysis of the local communication two channels come into question with the Nuki solution, which must be considered here: On the one hand the local network traffic and on the other hand the communication via Bluetooth. In both areas, our testers could not identify any signs of potentially critical vulnerabilities: The communication via the local network is completely encrypted and thus protected against attackers in the user’s own network. Against the Bluetooth communication we have run a list of standard attacks, which contains different sniffing, denial and replay attacks. Apart from the typical denial attacks (so-called jamming), for which every radio connection is potentially suspectible, we could not identify any critical weak points either.
Online communication
In principle, there is nothing wrong with the communication via Internet: All communication from and to the application or bridge is completely encrypted and an adequate certificate verification should prevent attackers from sneaking into the connection as Man-in-the-Middle. According to our tests, this works reliably in almost all cases.
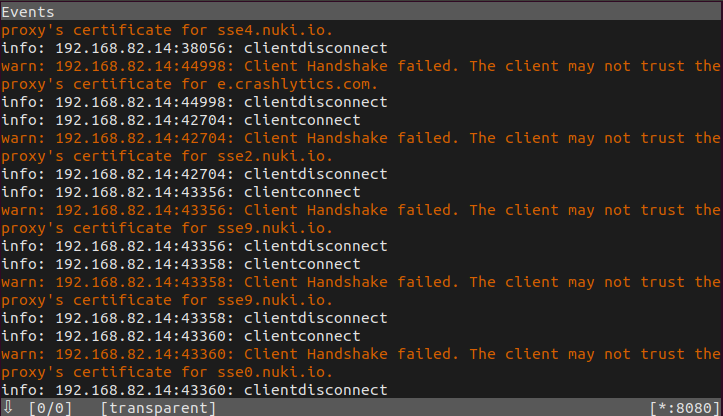
For a few bridge connections alone, we were able to determine that the bridge recognizes the invalid certificate presented by our Man-in-the-Middle and reports it, but explicitly decides to ignore the error and continue the connection anyway. In the observed cases, however, this did not give us a critical advantage as the attacker.
Data privacy
We had already analysed Nuki’s product data privacy statement in this year’s Nuki Combo 2.0 certificate test and rated it with ‘excellent’. The current version of the data privacy statement (May 2018) still corresponds to the one already considered. Accordingly, we did not notice any changes and the positive rating still applies: The statement contains all essential information, described in a simple and understandable way and localized to several languages. User data is only shared with third parties if this is necessary for the provision of product functionality.
Another positive aspect is that the use of Nuki solutions is possible without explicit registration and specification of user data. Only for the web access via Nuki Web a registration under indication of mail and password is necessary. This is a practice that we unfortunately only observe very rarely.
Only information and a reference to the additional data collected by Amazon (Alexa) and Google (Assistant) (if used) might have been desirable.
Verdict
All in all, as in the previous tests, the consistently positive impression is also confirmed for the Nuki Opener: All security-relevant areas have been implemented and secured in an absolutely adequate manner and we can also attest to exemplary practice in the area of data privacy. Although there are a few minor points of criticism, they do not cloud the overall impression significantly and could be easily eliminated by the manufacturer. Accordingly, the Nuki Opener successfully passes our certification process and is awarded the seal “Approved Smart Home Product”.

