Air fryers are trending in many places, especially due to the lower-fat cooking, for example, of French fries during our testing engineers’ lunch break. We subjected the app-controlled Cosori CS158-AF to an extensive security test.
Technical data
The smart air fryer CS158-AF has a 5.5-liter cooking chamber and heats it up with a specified power of 1700 W. It can be controlled with 11 automatic programs, but also manually – both via the control panel and via app or voice assistant. After the short setup, the fryer is permanently connected to the home Wi-Fi and can also be controlled on the go. The device is controlled via the VeSync app (Android, iOS). Recipes can also be viewed and started via this app – the recipe shows the necessary settings of the fryer. Similar to Xiaomi, the VeSync app is not only focused on fryers, but also includes numerous products from different areas of life, such as lighting, air purifiers and fitness equipment.
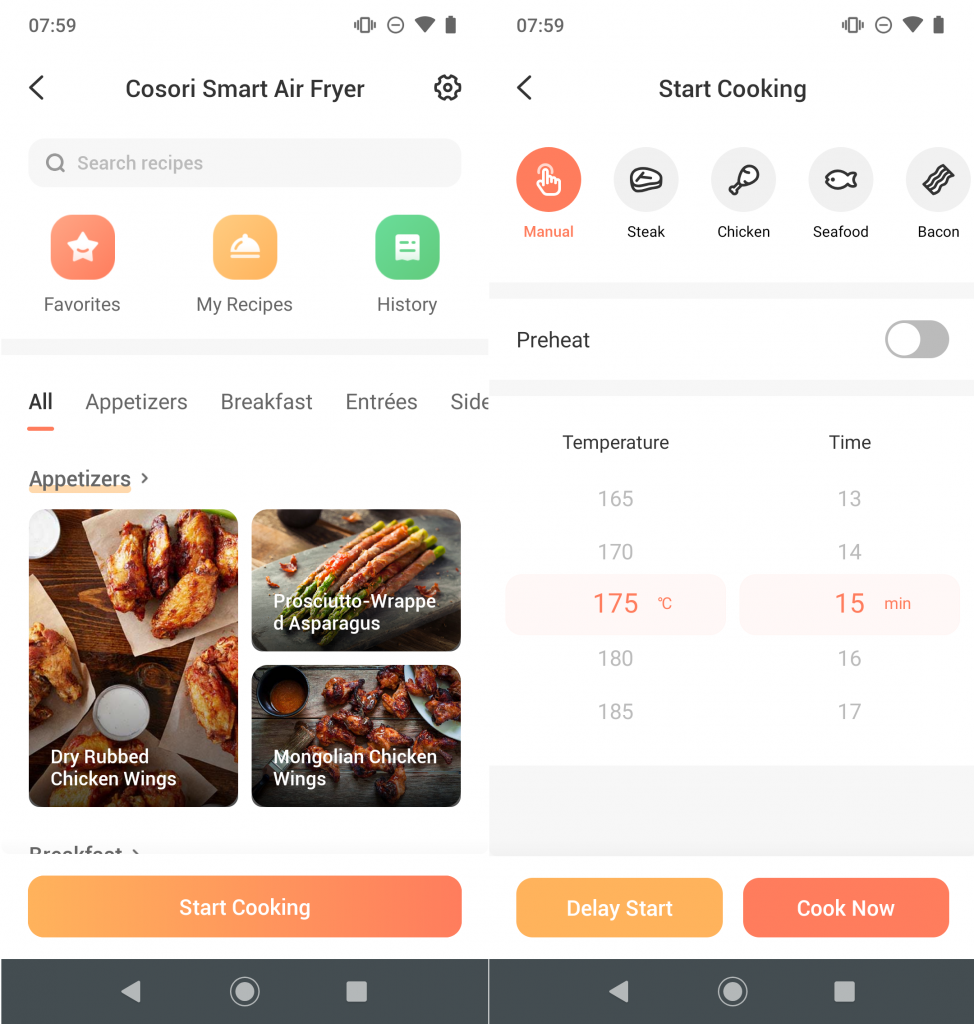
App
We subjected the VeSync app (version 3.1.32) to a static and dynamic analysis. It has very extensive permissions, for example GPS, contacts, call history, running apps and access to the camera. These are only requested if they are needed. The basic configuration of the application allows unencrypted communication to any server and, according to the static analysis, overrides various certificate validation mechanisms. Furthermore, access to numerous activities and services is shared with other apps, which could be a potential entry point for malware. Another possible entry point is at least one insecure WebView implementation in which Remote WebView Debugging is enabled. This could give full access to the application’s data even on non-rooted devices. However, this would require unlocking the smartphone, opening the correct view and connecting the smartphone to a computer with an active Android debug bridge. Accordingly, this scenario is rather theoretical, but it reinforces the impression of an application in need of security improvements.
A look into the data folders that are usually only visible through the application itself, on unrooted devices, shows, among other things, data from the numerous integrated trackers (according to static analysis: Bugsnag, Facebook Login, Facebook Places, Facebook Share, Google CrashLytics, Google Firebase Analytics, Sensors Analytics and TalkingData). Also the access credentials of the mandatory VeSync account are stored in plain text in the user_save_info.xml, where not the password itself but its MD5 hash (#rainbowtable) is stored. Additionally, an access token is stored, which is used to authenticate all further queries to the VeSync API. Reverse engineering was not necessary for this, since the app creates a debug log of every app start in the smartphone’s public memory, where all queries and responses are listed – including the access data used in plain text.
Online communication
The Cosori air fryer is controlled via the already mentioned VeSync API. According to the network analysis, a chip from the manufacturer Espressif is responsible for the Wi-Fi connection, more precisely an ESP8285 – a Wi-Fi SoC with integrated flash memory. The device establishes an encrypted MQTT connection to Amazon AWS US and always keeps it alive. Local control via the app apart from the VeSync API is not possible.

All connections to the VeSync API were TLS1.2 encrypted, but the API also allows older, insecure TLS versions such as TLS1.0. Therefore, there is no protection against downgrade attacks. Open source projects have already documented the API in detail. In a test of the important functions, including the check for an existing account of an e-mail address and the login itself, it was noticed that the API does not seem to use any rate limiting mechanisms and opens the door to attacks, for example using rainbow tables. In our test, it was not possible to control the fryer above its maximum temperature of 205°C, but a successful attack can still be dangerous.
The fryer itself validates certificates correctly, and the app has also implemented certificate pinning for all VeSync API queries, contrary to contradictory statements in the static analysis.
Previous hacks
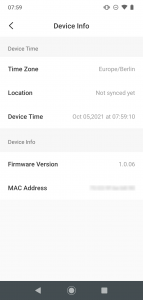
The Cisco Talos Intelligence Group discovered two vulnerabilities in the device registration process in April 2020. (CVE-2020-28592, CVE-2020-28593, firmware version 1.1.0) It exploited the open Wi-Fi hotspot that is available at the beginning of the setup and sent a corrupted configuration packet to the device, which could be used to open a debug port and execute arbitrary code. According to the report, physical access and resetting the device was required to exploit the vulnerability. In April 2021, Cosori released a firmware update that closed these vulnerabilities, according to Talos. It is interesting that the fryer we tested seems to have an older firmware version and still claims to be up-to-date.
Privacy
To learn about the privacy of the VeSync app and the Cosori air fryer, you first need to find the correct privacy policy. For example, the version of the privacy policy linked in the stores (as of 03.12.2020) is not tailored to European users, but it already contains information about the VeSync app. This is at least unusual, as most companies we know implement the GDPR guidelines globally. For European users, a separate privacy policy (as of 25.11.2020) is available, which, however, does not contain any information about the app, but refers to a separate, third privacy policy (also as of 25.11.2020). In the app itself, a privacy policy is also available in the language of the smartphone, but its content differs from the English-language version, at least the German one. In terms of content, we are therefore guided by the English-language app privacy statement as of 25.11.2020 – However, it remains generally only advisable to consolidate the privacy policies.
The privacy policy is not adapted to the GDPR; furthermore, the text, which is almost 6000 words long, only slightly addresses recorded data. For example, the numerous trackers integrated in the app and the data they record are not mentioned. Furthermore, the extensive app permissions are not mentioned. These should definitely be described in more detail, including their purpose.
Conclusion
The Internet of Things is expanding into many areas. Smart appliances are also gaining in popularity in the kitchen, for example the Monsieur Cuisine Connect, which we also tested. However, the Cosori CS158-AF air fryer leaves us with mixed feelings. Of course, one can argue about the sense and nonsense of a fryer that can be controlled via the Internet – but what is not debatable is that the access must be secured and the data collection only to the extent that the purpose requires it. Both points are rather questionable in the case of the device from the US manufacturer. The online communication, which is always encrypted, does not hide the high data collection by many analysis tools and trackers. Furthermore, both the VeSync app and its API are in need of improvement.
For this reason, we award the Cosori CS158-AF one out of three possible stars.

