Smart kitchen appliances are gaining in popularity. In addition to the Thermomix from Vorwerk or Krups Prep & Cook, discounters like Aldi and Lidl have also jumped on the bandwagon. In the following test, we put the Silvercrest Monsieur Cuisine Connect from Lidl on the security test bench.
The German discount chain Lidl has launched Monsieur Cuisine Connect, a product that competes with other kitchen machines such as the Thermomix. In addition to a 7″ touch display, it also features WiFi, via which new recipes are automatically downloaded. The function called “Cooking Pilot” displays recipe steps one after another and controls the appliance almost automatically.
Technical data
The Monsieur Cuisine Connect is equipped with an 800 Watt motor and 1000 Watt heating power. A 4.5 liter stainless steel mixing bowl, an integrated scale up to 5kG and a temperature range of 37-130°C complete the package. The motor rotates from 120 to 5200 rpm, the built-in knife is used for stirring in left-hand rotation and for chopping the ingredients in right-hand rotation. The speed can be adjusted in 10 steps, furthermore three automatic programs for kneading, steam cooking and browning are programmed.
Software/Firmware
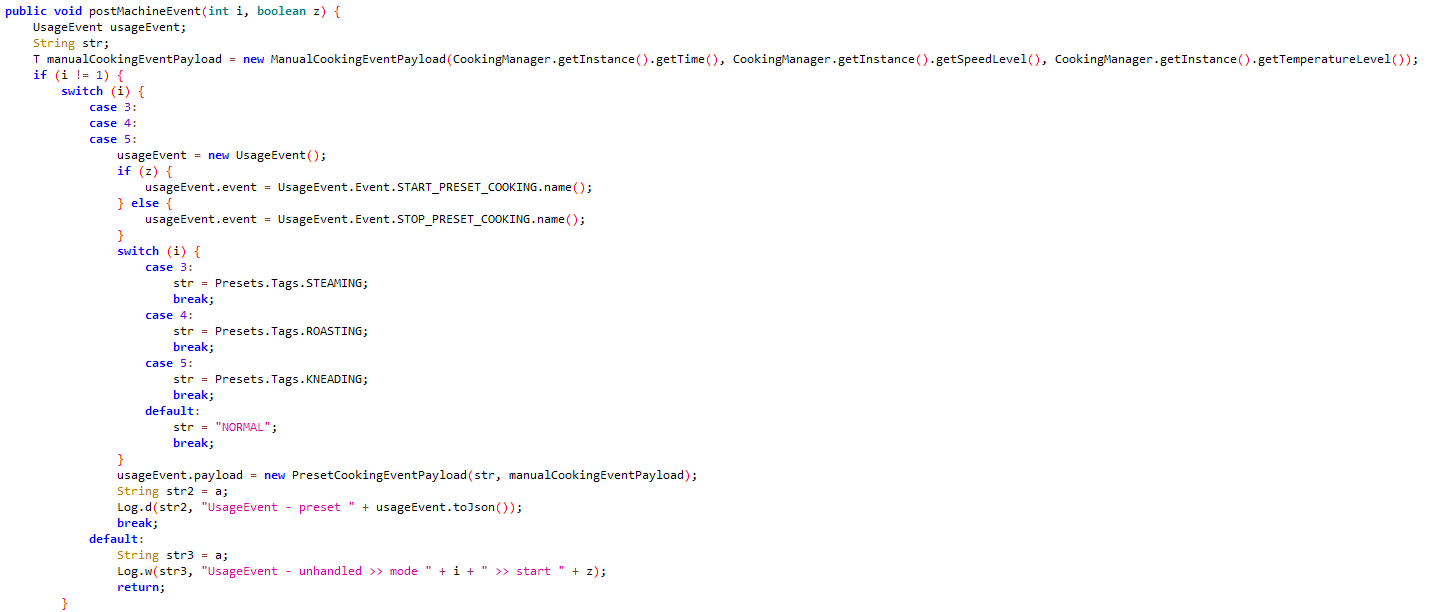
In addition to the motor and heating element, the Monsieur Cuisine Connect mainly consists of a control unit and a customized 7″ Android tablet. Android 6.0 is pre-installed on the tablet, which is driven by a Mediatek MT6580 Quadcore processor. However, this is well isolated by default. For example, the device cannot be accessed via network, all ports are closed. When starting the device, the pre-installed “MCLauncher” app loads – the user interface. With this app, the device can be completely controlled, WiFi can be set up and the device can be updated. Also pre-installed is the “MCUpdater” app, which is called by the launcher for the purpose of updating. Both apps come from a Hamburg-based company, Silpion IT-Solutions GmbH.
The “MCLauncher” app handles the serial communication, i.e. it sends the control commands integrated in the respective recipe for heating, tare/measure scale, motor direction and speed, etc. to the hardware.

Getting to the insides of the Android system is not trivial, but it is now well documented. (Github, Blog) The security of the device is compromised by this, because besides the rooting of the device, other apps can be installed, which are a high risk due to the outdated Android system.
Apps
Lidl also provides an app via the Apple App Store or Google PlayStore.
However, this only has the same range of features as the Monsieur Cuisine website. Both enable the users to view recipes curated by Lidl or published by other users or to post them themselves. Recipes can also be marked as favourites. If the cooking instructions are provided by Lidl, the recipes are synchronised with the Monsieur Cuisine Connect.
The app developed by the Bremen-based company Appfarms always communicates TLS1.3-encrypted with servers of the domain monsieur-cuisine.com. The website is protected by CloudFlare, therefore all requests are routed via American servers of the provider. Since CloudFlare is also the certificate issuer, it is technically possible for this service to view all transmitted data in plain text.
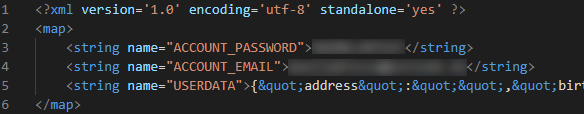
The app stores the user’s credentials in the app data folder in plain text. In the default setting, this storage area can only be accessed by the app itself, so it is not critical in this respect. However, on devices rooted intentionally or by malware, this can lead to the data being spied out. We recommend the implementation of the Android KeyStore to store the access data additionally encrypted and secured.
Online communication
Since the Monsieur Cuisine App in the end only displays the website, we focus in this section exclusively on the communication of the device itself.
At the beginning and end of each action of the appliance (kneading, cooking, chopping etc.) “mc20.monsieur-cuisine.com” TLS1.2 encrypted is addressed. Transmitted information contains information about the use of the appliance, including, for example, the integrated programs (steaming, roasting, kneading). Even during longer periods of operation, only very little Internet communication was detected.
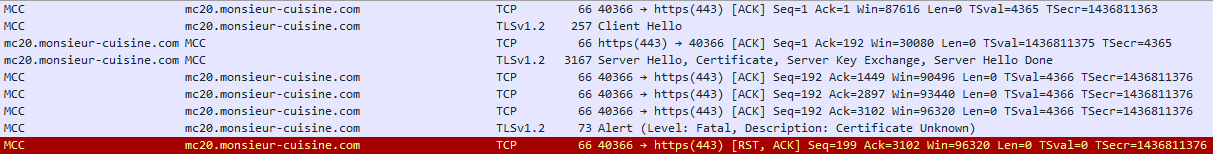
Encrypted traffic to the Lidl server terminates due to expired certificateDuring the test, communication failed because the domain’s certificate issued by Let’s Encrypt had expired. However, this has been renewed in the meantime and the problem has been solved for the time being at least until 26.05.2020.
Privacy
The privacy policy is primarily related to the website and its app. The Monsieur Cuisine Connect is mentioned only casually. Since usage data is also sent to the cloud by default, we are missing a passage on what data it contains. Although there is a point in the settings of the device where sending usage data can be deactivated, data was still sent at the start and end of each action during the test.
Apart from sending usage data, the device is very data-friendly, and no customer account needs to be created to put it into operation. The fact that the manufacturer’s website is protected against attacks by CloudFlare is not mentioned in the privacy policy and must be added. The not uncontroversial service provider (in this case data processor) can technically read all data transmitted via the website.
A few weeks ago there were several articles about the device having a hidden microphone and “hackers” might be listening in. We cannot confirm that Lidl is recording data without authorisation. Both pre-installed Lidl applications currently have no permission to access the microphone. This is secured by the permissions concept of Android. Only if the user decides to “open” the Android system and install other apps using the above-mentioned methods, there is a theoretical possibility of use and thus the danger propagated by many news agencies.
Conclusion
With Monsieur Cuisine Connect, Lidl has launched an attractively priced, smart kitchen machine under the Silvercrest brand. The Android version used is outdated, but well protected by factory settings. In the area of privacy, there are complaints that have led to us deducting a star from the overall ranking.


Great review, leaves me with just one question though.
Can it function without internet connection though?
I.e. are the recipes available for use during a temporary internet outage or do I have to operate it ‘manually’ or is the device effectively a brick during that time?
Hi Dennis
I am a total noob.
I was scanning my monsieur cuisine and noticed an open port that is currently unassigned. tcp 46644.
I could notice any traffic to mc20.monsieur-cuisine.com
Can you help me to understand?
Thank