Another newcomer from the Smart Locks category joins the list of IoT products certified by us: The Smart Door Lock and Keys combo from French manufacturer Netatmo. How it performed in its first test run and why it undoubtedly deserves the title of “Approved IoT Product” is explained in the following report.

Features
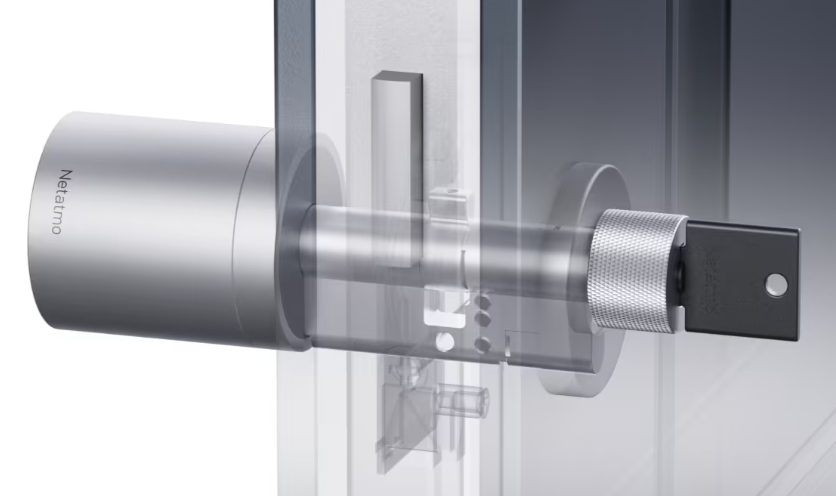
Netatmo‘s Smart Lock takes a slightly different approach to all the Smart Locks we’ve tested so far, and to the majority of all commercially available Smart Locks. Unlike pretty much all of its competitors, the Netamo lock completely waives the concept of motor-controlled operation of the locking cylinder. Here the device which is applied to the locking cylinder does not move it directly, but merely blocks it or releases it accordingly. The physical movement of the locking cylinder then takes place quite classically through muscle power. The right to move the locking cylinder, i.e. authentication, can then take place in two ways: Firstly, a time-limited release can be obtained via a mobile application and Bluetooth, within which the authorized user can open the lock by physically operating or turning the external cylinder attachment. In addition, as the “Keys” in the name of the solution already indicates, there is also the option of opening the lock classically with a paired smart key (basically a transponder in the form of a key). This does not require prior approval by the app, and the whole thing basically works like a classic door lock. However, digital invitations and time-limited authorizations can also be sent easily, so that the solution practically brings together the advantages of both worlds.
The smart lock itself does not establish an Internet connection – communication with the cloud is handled by the mobile applications, which in turn control the lock via Bluetooth.
Mobile applications
The developers do not allow themselves any serious mistakes in this area: The implementations for Android and iOS (tested app versions com.netatmo.camera 3.12.0.4 and 5.1.10, respectively) are adequately realized and security-relevant, critical areas, such as certificate pinning, are cleanly implemented. Otherwise, as with practically every mobile application, there were a few theoretical weaknesses here and there that could still be eliminated to further increase the security level. These are, for example, as is so often the case, deployed libraries that do not use all of the recommended memory access protection mechanisms or a configuration that allows the app data to be exported with physical access and developer mode enabled – realistically irrelevant. General but often forgotten security aspects, such as password security and complexity, are also taken into account and the user is obliged to use secure and sufficiently complicated passwords.
Local and online communication
As mentioned earlier, the Netatmo Smart Door Lock itself has no Internet connectivity and is only accessed via Bluetooth. Of course, this was also examined in the test and exposed to some standard attacks, but it proved to be robust. An extended code analysis for this area also did not reveal any obvious and/or critical weak points.
The same applies to the online communications of the applications. The observed communication was always encrypted according to current standards and important security mechanisms, such as certificate pinning, are implemented cleanly and effectively. In order to gain access to the plaintext communication for analysis purposes, we had no choice but to modify the application itself so that the encryption could be broken. An attacker would need physical access to the unlocked user smartphone to do this. However, the analysis did not reveal any major surprises: The authentication runs via classic bearer / token authentication. Here, a token is requested from an authentication server with the help of the user’s credentials, which is then used to authorize all further access to resources and services – adequately implemented and configured, there are actually hardly any points of attack here. Without additional knowledge about user credentials, an attacker can only use brute force. In this case, however, this is prevented by activated rate limiting, i.e. after a few requests with incorrect credentials, no further requests are answered for a while, and the server responses to requests with incorrect credentials do not provide any information about “how” incorrect the request was. Here it also happens that a server response contains information about which part of the credentials was incorrect, username or password but in this case we could not elicit such information from the Netatmo authentication server.
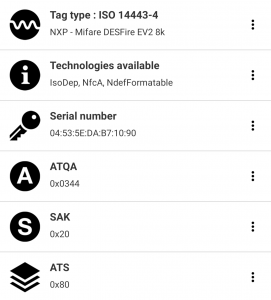
There is not much more to say about the smart keys either: The MIFARE DesFire EV2 standard used is security-certified according to EAL5+ and is thus considered by us as adequately secure. Of course, we still tried to read, copy and emulate the keys, but as expected, were unsuccessful.
Data protection and privacy
When it comes to data protection, the solution does not allow itself any more weaknesses. The implementation of the privacy policy is really exemplary, with all important information detailed and yet clearly presented. Here, the user really has the opportunity to look up what data is collected from them when using this or that service. Thus, an informed decision can be made whether and to what extent one wants to use which service or which product of the manufacturer. That said, the Netatmo product is really not a massively data-hungry solution. Only the two Google trackers CrashLytics and Firebase can be reliably identified, and there were no other indications for excessive or unnecessary data collection.
![]()
Verdict
All in all, the Netatmo Smart Door Lock and Keys solution proves to be exemplary in its test debut and in all relevant test areas – the solid security concept paired with the very good data protection implementation really leave us little room for criticism. Accordingly, we gladly award our certificate “Approved IoT Product”. Bon travail, Netatmo!

