ITEAD from Shenzhen (China) sells a series of ESP8266-based smart home products under the Sonoff brand, which is enjoying increasing popularity in the hobbyist community. The ESP8266 is a programmable SoC with WiFi, UART and SPI interface. It can be flashed with any firmware and is therefore suitable for many projects.
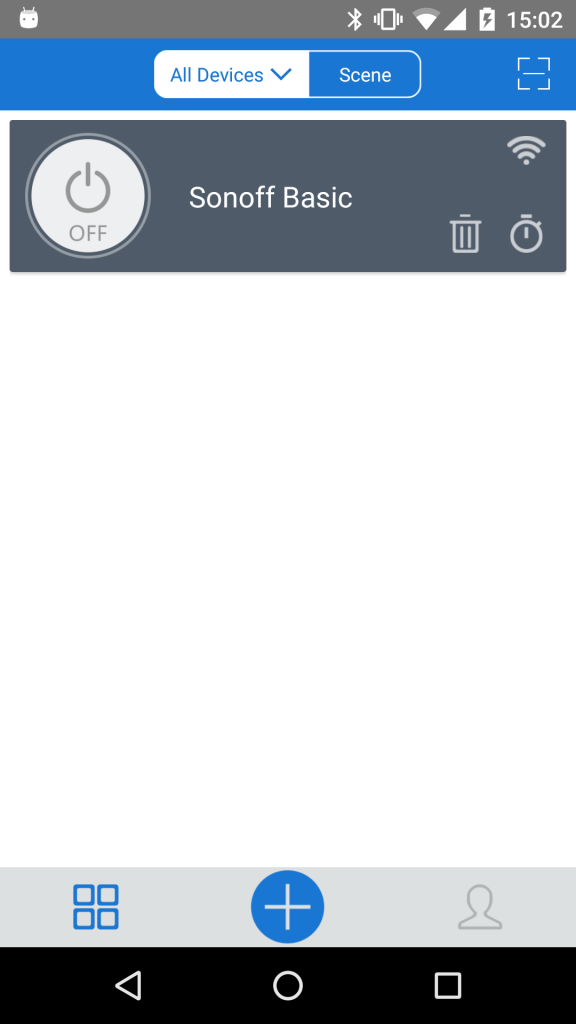
For our test we used the Sonoff Basic WiFi Wireless Switch including the original firmware and the corresponding app “eWeLink“.
Setup
For initial setup, the pairing button of the device has to be pressed for 5 seconds. It then opens its own, secure WiFi network, via which it can be paired. After entering the data of the WiFi network to be connected in the future, the Basic Switch is displayed in the app.
Online communication
Apart from the setup, there is no direct communication between the app and the Sonoff device, all switching commands are routed via the cloud (Amazon AWS EU).
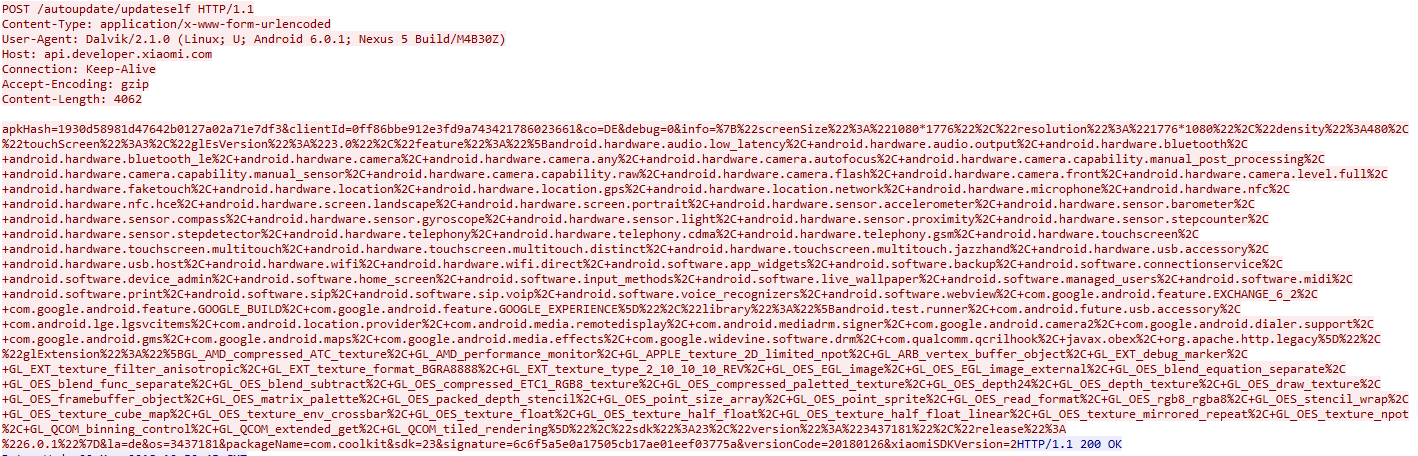
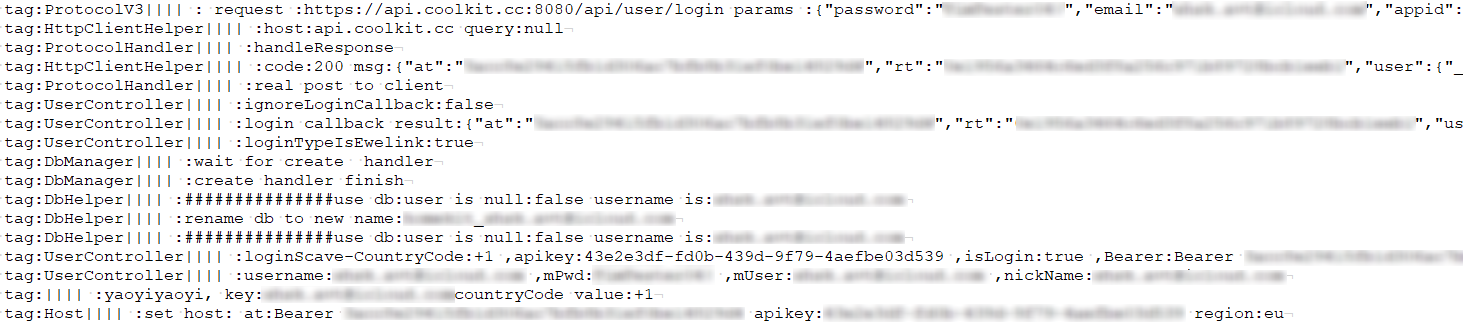
The connection between the Sonoff switch and the manufacturer’s cloud is TLS1.2 encrypted and therefore well protected. The app communicates identically encrypted with the cloud servers, but after closing the app some unencrypted connections take place, mainly to analysis services of Tencent and Xiaomi.
App
After decompiling the app, we found some well obfuscated classes. In the absence of a certificate pinning implementation, the encrypted parts of the web requests are only protected against simple man-in-the-middle attacks. However, a successful man-in-the-middle attack would require the attacker to install a certificate on the user’s device so that the communication can be eavesdropped or manipulated unnoticed.
Important data worthy of protection, such as the WiFi password, is stored in the secure app’s data folder in plain text. However, this does not lead to a devaluation, as this app area can only be read without restrictions on rooted smartphones.
More serious, however, is the detailed log file that the app stores in the public part of the storage (readable by everyone). The plain text log file contains tokens, API keys and also the access data for the Sonoff account.
Firmware update & hardware
The firmware can be updated via the app. Up to now, developers had also made use of this procedure in order to be able to install their own firmwares on the device. (e.g. SonOTA) This made it possible to install freely available firmware such as Tasmota or EasyESP, which were not part of this test.
With firmware version 1.6.0 available at the time of testing, the firmware update procedure was changed and 3rd party software was excluded from OTA updates.
Another way to install an alternative firmware has been left open or intentionally placed by the manufacturer. After opening the housing, solder points for a serial or FTDI interface are visible, via which the ESP8266 can be flashed directly.

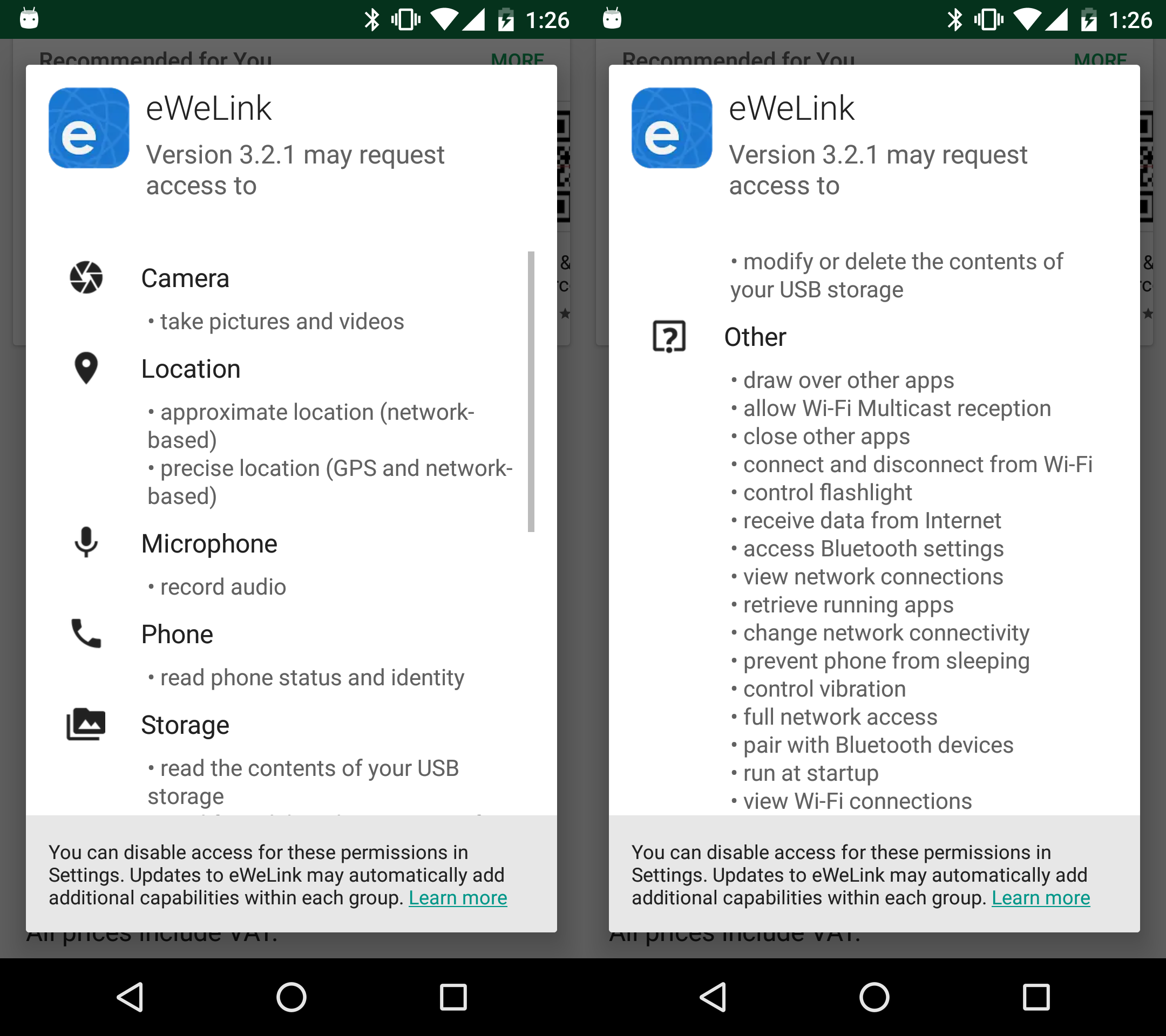
Privacy
Unfortunately, no points can be awarded for privacy, as no privacy statement was available at the time of testing. Only a short description of the required, but also numerous android app’s permissions is available. These go far beyond the necessary functional scope of the app, which leaves the premonition that personal data could be collected and analyzed by Chinese companies.
Conclusion
The pure functionality of the app and the Sonoff Basic WiFi Wireless Switch is well encrypted and protected against simple attacks. However, the overall impression is severely clouded by the unencrypted communication to Chinese analysis services, the many permissions of the Android app and the detailed log file stored in the public storage area of the smartphone.


Pingback: Sonoff Basic WiFi – AV-TEST Internet of Things Security Testing Blog - IT Notes of TaLubu
I just sent an email to the security team at the Play Store. That eWeLink app is pretty much malware. I wouldn’t recommend that anyone purchase these devices unless you are skilled enough to install a third party firmware. The app took over and trashed my network. Not impressed. I bought the Sonoff stuff since it could also be controlled with an RF remote. The devices are far from the router.
Lol, guess I got what I deserved for being lazy. That app just don’t look right from the get-go.
Pingback: Using a NodeMCU ESP8266 as a passthrough serial converter chip · Anson VanDoren - Techg8
Pingback: Who's using IoT? That's right, you are - here's how to stay safe - SYNAPSYS | Authorized Acronis Distributor
The only good solution you have is to use your own server component in your home. I use text messages for alerts sent by python and the bridge functionality is not allowed on the web, my router an Archer series supports a VPN server and I use that to admin by a custom webpage once connected. This all seems a lot of work but necessary for privacy. Its the same for all the IP cameras and the Asian cloud connect services