In our test of six children’s smart watches, one of the candidates is the Pingonaut Kidswatch. The watch has many features, like realtime localization of the loved ones, geofencing, telephone function as well as voice and text messages. In the following blog-post we present our findings.
App checked
Important classes and functions are obfuscated which makes Reverse-Engineering more difficult. An API-Key is being used for authentication between App and server. The API-Key is stored unencrypted, but in the secure App’s folder. Because this folder can only be accessed by others, if the phone is rooted, we don’t consider this as a major issue. All features of the App can also be used via API requests, e.g. localization or sending text messages.
The App uses SSL encrypted connections for every communication, but hasn’t any Certificate Pinning implemented. Therefore, a Man-in-the-Middle attack could be possible, by making the user install and trust a crafted certificate.
Online communication
The whole online communication of the Pingonaut App is TLS1.2 encrypted and therefore protected against simple replay- or man-in-the-middle-attacks. Servers of third parties are also contacted with encrypted connections only.
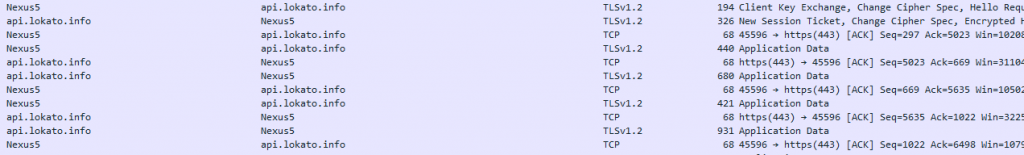
The manufacturer’s API (api.lokato.info) doesn’t have Rate Limiting implemented. Because of that, many Brute Force attacks are possible in a short amount of time, without being recognized or blocked. The probability of a successful attack is quite low (1:3236), nevertheless we recommend to fix this issue.
Privacy tested
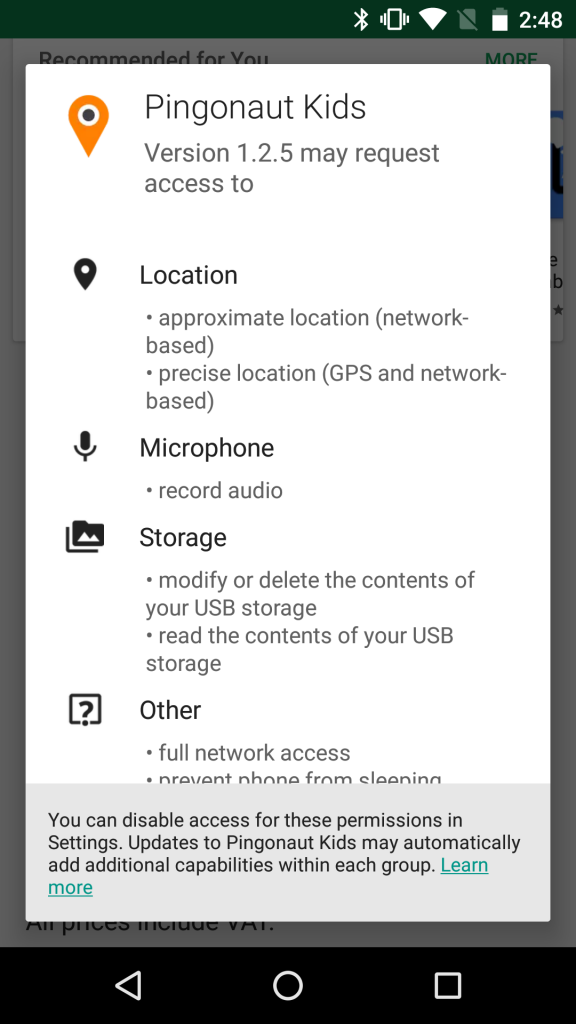
The privacy policy of the Pingonaut Kidswatch is easily understandable and informs in clear terms, how and for what purpose recorded data is being processed. According to the document, the manufacturer doesn’t share any data with third parties, also location data is being deleted after 30 days. Data is usually being processed in Germany and in anonymized form. If processing in the USA is required, the manufacturer only cooperates with service providers, which are part of the EU-US-Privacy-Shield and guarantee privacy on EU-level. The Android App requires only a few permissions which are required for the functionality:
- Location: Showing the parents location on the map
- Microphone: Recording voice messages
- Storage: Saving voice messages
Conclusion
The german manufacturer Lokato built a solid solution in regard to privacy and security and is being awared with a top rating of three stars in our comparison test.

