If one of the big names in the electronics sector presents a new fitness tracker, which also attracts attention due to its comparatively low price, it is of course worth a look. Therefore, as part of our large fitness tracker test, we have subjected the Lenovo HW01 to our extensive security tests. As the following report shows, some of the problems we found were of a more serious kind and will be explained below.
Application Security
The corresponding mobile application “Lenovo Healthy” (in the tested version 1.3.0 (170920)) was checked by us for potential conceptual and implementation-related security gaps. The first step, the static analysis, provided a longer list of possible critical problems. Especially possible weak points in the implementation of SSL secured communication were detected several times. In addition to a few unsecured URLs found in the source code, problems with certificate validation were also detected, so that actually secured encrypted connections could also be vulnerable to certain attack techniques, such as man-in-the-middle attacks. The possible difficulties identified in this way were then further investigated in practical tests.
The subsequent manual analysis of security-relevant code areas also revealed further possible security risks. In many cases, the crypto functions used are implemented using static calculations (e.g. XOR functions) and outdated hash algorithms (MD5), whereas keys can be found for other parts (for example, for AES encryption), hard coded in the source code. Both techniques are unacceptable from a security point of view, especially since the lack of obfuscation makes it easy even for inexperienced attackers to locate and make use of these code passages.
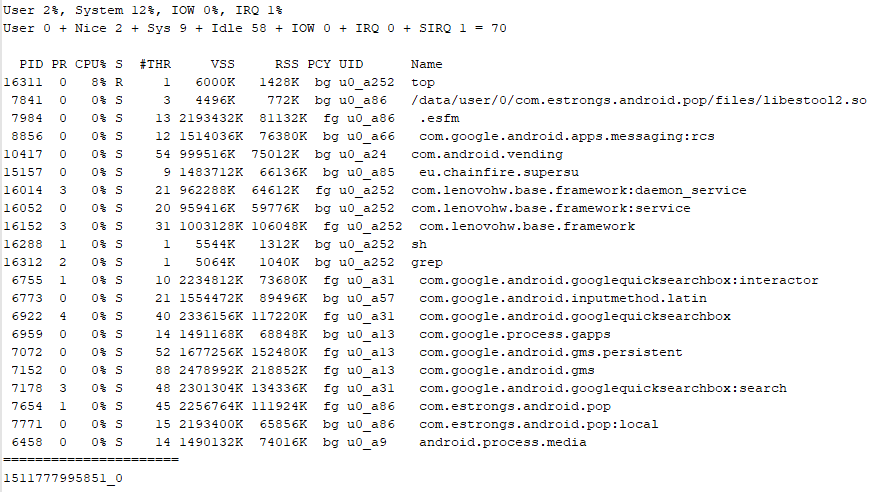
In addition, there is excessive data aggregation outside the secured app storage, which leaves this data freely available on the SD card for any other app on the smartphone. Mainly system and process information is stored in this way. For example, data on running processes and resources used can be found in the logs – it is not possible to determine reliably why this data is collected and stored and whether it is also transferred to the cloud. However, the fact that this data even exists and that the application also requires a conspicuously high permission level does not necessarily inspire confidence on user side.
Local Communication
Local communication between the app and the tracker is implemented via Bluetooth LE, as with all other tested devices. In this point, the Lenovo product has only one obvious weak point: For pairing, a physical confirmation at the tracker is required by default, so authentication was considered. However, in the test we were able to use the device in parallel with two different user accounts without having to unlearn or reset it again, and thus share collected data between different users without any problems. Therefore, the Lenovo HW01 is not recommended for use in insurance bonus programs or the like – at least from the insurer’s point of view.
Online Communication
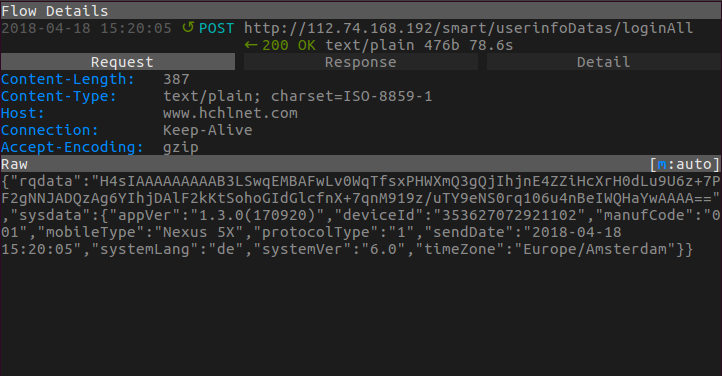
As the static app analysis already indicated, the area of online communication is also not free of potential weak points. The first serious problem is the fact that the login process is completely handled via an unsecured HTTP connection. The data transferred in this way cannot be read directly in plain text and is at least concealed at first glance. The further test showed, however, that the login can be carried out via a simple replay attack, i.e. the recording of the login process and a “replay” at a later point in time. This means that an attacker can still gain access to a user account through a relatively simple attack, even if he cannot break the supposed data concealment itself in order to access the login data directly.
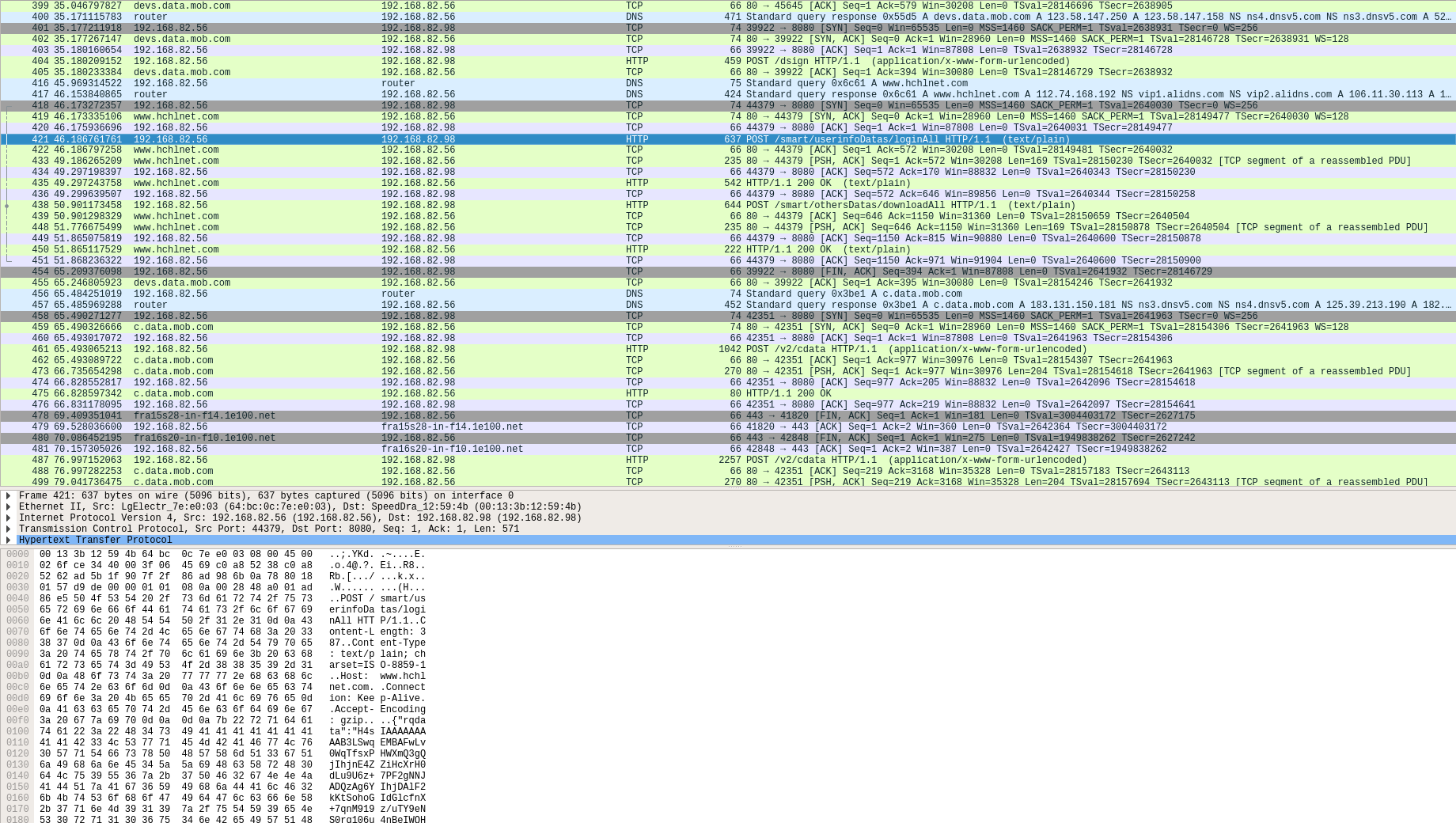
In addition, we observed in the test a communication with countless different domains, where it was not always clear, for which purpose, which data and to whom data is transferred at this point. This fact further leads to a rising user suspicion in regards to the product.
Data Privacy
The Lenovo Healthy App Privacy Policy is hosted on Facebook (as of May 18, 2016) and is not very informative. The data processing takes place in China, furthermore it was noticed in the test that the app communicates with a variety of different domains. To what extent a privacy statement hosted on a social network is valid can only be clarified by legal advice – nevertheless, this leaves a very unprofessional impression on us.
Since the app also claims a lot of permissions and thus secures extensive access rights to the user’s data without the reason being stated in the data protection declaration, we unfortunately cannot award any points for data privacy and privacy statement section of our test.
Verdict
The Lenovo HW01 has potential vulnerabilities in all tested areas that can pose a practical threat to the user and his data. A partial incomplete, faulty and unfavourable implementation of important security areas within the applications leads to some more critical gaps in the security concept of the product. Overall, therefore, only 1 star can be awarded out of the possible 3 stars.

