Nuki successfully passed the re-certification of its Smart Lock with the current version, the Nuki Smart Lock 2.0 (firmware version 2.4.5) including the associated bridge. Once again this year, the combination of Smart Lock and Bridge convinced the testers in our laboratory so that we can once again award the “Tested Smart Home Product” certificate. Already in April 2018 we had the then current version of the Smart Lock in our labs for certification. The product of the Austrian manufacturer went through all our tests without major issues and could easily be certified by us.
The following test report explains in which points and in what way exactly the Nuki Smart Lock 2.0 scored during the tests.
Application
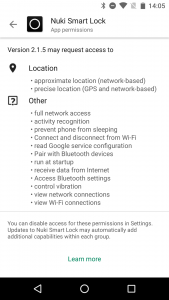
The current application versions (for Android v2.1.4, for iOS v2.1.7) were analyzed statically as well as dynamically for possible vulnerabilities during our test procedure. As in the previous year, the Android application is still well protected against possible reverse engineering attempts: The application source code and the security-relevant functions it contains are protected by obfuscation, no log data or other sensitive information is stored unsecured on the smartphone, and even the output on Android’s Logcat debug log is remarkably sparse.
In terms of implementation, we also found no obvious weaknesses in the security-relevant areas for authentication, communication and their encryption, both local and online.
The static analysis for the corresponding iOS version is of course more difficult, but the application behaves dynamically analogous to the Android version. This means that no vulnerabilities could be identified there either.
Local communication
In the case of the Nuki Smart Lock 2.0, the local communication between smart lock and smartphone respectivley application takes place via Bluetooth in the new standard 5 (Zigbee wireless hardware is already installed, but is not yet actively used in the current version). The payload of this communication is adequately encrypted and effectively protected against standard attacks such as replay attacks. Bluetooth technology itself, like all radio communication, is fundamentally susceptible to certain denial attacks, such as radio jamming, which under certain circumstances can generate certain theoretical threat scenarios. In practice, however, we were not able to identify any critical and/or obvious weaknesses in this area.
To register a new legitimate smartphone at the lock, invitation codes can be used or the registration can be carried out directly by pressing a button on the lock. In order to generate invitation codes, the security PIN of the lock must be known. However, this is not necessary if the second variant is used by pressing the button. This means that the physical access to the lock is directly used as legitimation for its control and no further authentication is required. This is certainly permissible for most application scenarios, especially in the private sector. If, however, the user cannot assume in his application scenario that every person with physical access to the lock should also have potential control over it, this login method should definitely be deactivated via the app. This is also possible without further complications. Nevertheless, we would simply like to see a PIN query for direct login as well as a user notification when registering a new user smartphone.
Online communication
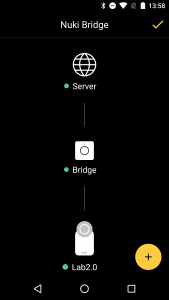
Via the Nuki Bridge, the user has the possibility to operate the Nuki Smart Lock 2.0 while on the move. In addition, it can also be controlled via web browser – this requires an account, which can be registered via the Nuki app under the item “Nuki Web”.
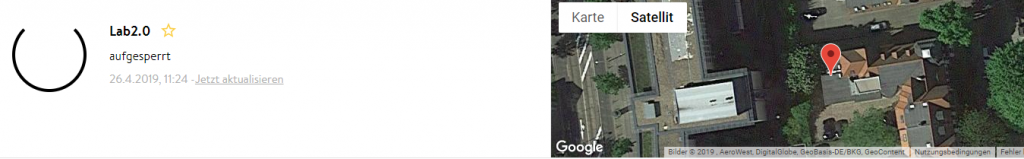
In this case an advanced password checking algorithm is applied that recognizes and prohibits common passwords. Since this algorithm does not necessarily recognize every weak password, we recommend that users use a sufficiently long and complex password (at least 8 characters, upper and lower case, special characters, etc.) – not least because access to the Nuki Web account not only provides the option of controlling the lock itself, but also provides the exact position of the lock.
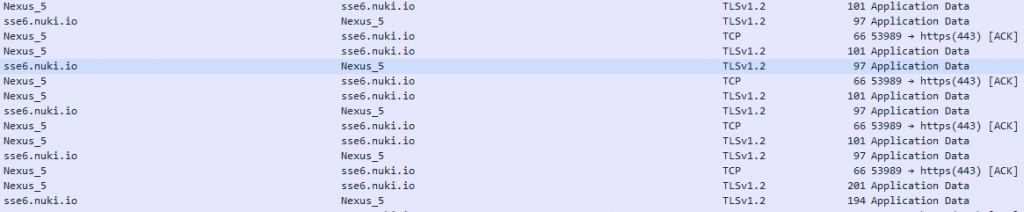
In the actual communication via the Internet between the application and Bridge itself, no weak point could be found – all connections are adequately encrypted according to current standards and effectively protected against the usual standard attacks, such as man-in-the-middle.
Amazon Alexa Skill
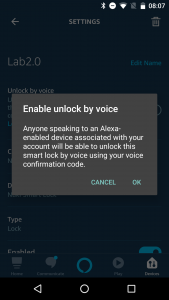
The Nuki Smart Lock 2.0 can also be controlled via the corresponding Alexa Skill. The online communication, like all communication via Amazon Alexa, is securely and effectively encrypted. In order to be able to use the lock via the skill a PIN must be configured for Alexa.
The Nuki application itself already points out the possible dangers when using Alexa together with the Smart Lock 2.0 when setting up the skill. However, we would like to emphasize once again how much the otherwise very high security level of the Nuki system is reduced by using Alexa. In our opinion, the possibility that an unauthorized person might eavesdrop the loudly spoken Alexa security PIN is too high a risk, especially in the highly sensitive door lock scenario, for which we would recommend to not use the skill. At the very least the user should be aware of the potential danger.
Data Privacy
Nuki can also score points in the area of data privacy. The privacy policy is easy to understand and written in several languages. In addition, it contains all essential information on data collection, storage and processing, which we attach particular importance to. According to the data privacy policy, only the data necessary to ensure functionality will be collected and processed. We are only missing one section on using the system together with the voice assistants Amazon Alexa and Google Assistant – A brief explanation of the implications of using these systems could at least be mentioned briefly.
Otherwise, it should be noted that the Nuki system can be used extremely data efficient – even to use the web account, only an e-mail address and the corresponding password is required. Normally, a large amount of additional user information is requested for setup purposes, and the NUKI system is positively cautious in this respect. Very good!
Verdict
The current version 2.0 of the Smart Lock from the Austrian company Nuki convinces our testers in all security-critical aspects. The manufacturer can still refine at a few points to even further increase the security level. All in all, however, we found a security concept that was adequately implemented throughout and that met our test criteria in all relevant areas. Accordingly, we can award our certificate “Approved Smart Home Product” to the Nuki Smart Lock 2.0 again this year.


Pingback: Kurztest: Nuki2 – Smartes Türschloss in Version 2.0 | macmaniacs.at
Pingback: Recensione – Serratura smart Nuki – Antonio Loi