VisorTech advertises its Smart Lock: “Never locked out again: Because you simply close your front door with a tap of your finger! Alternatively, open your door lock via smartphone app or transponder”. Unfortunately, opening the Smart Lock is all too easy. In order to open doors in which the VisorTech lock is installed, attackers only need to copy the access data stored unencrypted on the supplied transponder with a free app. Meanwhile, Pearl has responded to the transponder’s insecurity and wants to equip new locks with transponders, which have been fixed regarding the discovered vulnerability. Whether customers of previously sold locks will be informed and will receive secure transponders, was left unanswered by Pearl. Since the VisorTech TSZ-580.fp is anything but smart when it comes to security, the AV-TEST Institute has decided to warn against its use.
Manufacturer informed in advance
Smart door locks are extremely practical, but also have some attack vectors conventional locking systems don’t have. In the worst case, an unsecure smart lock can be overcome without the attacker needing physical access. In such cases, it will also be difficult to subsequently prove the burglary, since corresponding physical traces are missing. Although products of this category have been able to provide adequate security in past tests, there are also candidates with blatant security flaws that open doors wide to attackers. This category includes the VisorTech TSZ-580.fp.
After revealing serious security flaws in the IoT laboratory, AV-TEST decided within the Responsible Disclosure procedure to withhold publication of this test report for two months and to inform manufacturer VisorTech resp. its distribution partner Pearl beforehand. The aim of “Responsible Disclosure” is to not endanger the users of affected products and to give manufacturers sufficient time for security updates or other appropriate responses to the situation. Accordingly, AV-TEST informed Pearl’s press office on May 29, 2019 of the detected security leaks on the VisorTech TSZ-580.fp. On the advice of AV-TEST Pearl responded on July 25 with modifications of the transponder. AV-TEST tested the updated device provided by Pearl and confirmed that at least the simple copying of access data via app in this test device was no longer possible. All other security leaks mentioned in the test were still open.
What problems the VisorTech TSZ-580.fp has and why the AV-TEST Institute warns against the use of the Smart Lock, is explained in the following test report.
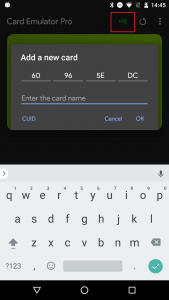
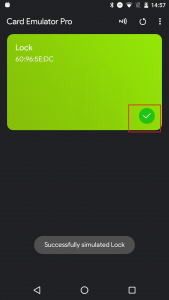
Vulnerability transponder (local communication)
The most obvious weakness of the VisorTech lock are the transponders. These can also open the lock, which is otherwise opened by fingerprint or by using the smartphone app. The transponders and the data saved on them are however completely unsecured and can be easily read by potential attackers: As tests in our labs showed, the transponders can easily be copied and emulated within seconds using freely available apps. This way anyone can easily open the corresponding VisorTech TSZ-580.fp. This extremely easy to exploit vulnerability allows for effective attacks and was ultimately crucial for the notification of the manufacturer by the AV-TEST Institute.
Users of this lock are advised to refrain from using the transponder, as long as the manufacturer has not demonstrably eliminated this risk.
But the unencrypted transponders are far from beeing the only security flaws in the VisorTech product.
Insecure app
Starting with the analysis of the mobile applications (Android and iOS) the testers brought other flaws to light. For example, the essential part of the app, at least the main functionality, is written completely in the programming language C and is integrated into a JAVA stub by so-called shared objects (.so) in order to be able to run on Android. Function calls (via so-called natives) are obfuscated within the stub app. It is questionable whether this implementation was chosen for security reasons, especially as the patching of the app is prevented or at least severely restricted. Some obvious vulnerabilities of the application, for the identification of which a deeper reverse engineering is not necessary at all, raise justified doubts about this intention.
For example, the Android application contains various implementation errors, including so-called implicit intents and public content providers. With their help, third-party applications can access data from the app and might get potentially sensitive information. In addition, the implementation of encrypted connections seems to be flawed. But more on this in the corresponding section on online communication. A further complicating factor is that the app stores the QR codes necessary for setup and connection between the lock and the smartphone unsecured as a JPG image on the SD card of the smartphone.
Apart from that, the app demands some critical permissions on user smartphones. For example, they have to allow processes to be started and stopped unnoticed in the background without informing the user. The test also showed that even with the main application closed, processes in the background communicated over the Internet, transmitting data to Far Eastern domains such as “ipush” and “alibaba” – classic data collection.
Unencrypted online communication
The online communication of the mobile applications was also analyzed. A large number of unencrypted HTTP connections could be observed in the lab. It is particularly critical that even the login process ran on the unencrypted Internet protocol. Although account data such as username and password were not transferred in plain text – the data was at least veiled – but this credentials could be intercepted and used for authentication attempts. Because neither app nor online service provide timeouts after several failed attempts, attackers can use the data for classic replay attacks. Thus, attackers can intercept login data and successfully complete the login process.
Privacy does not seem important
In the privacy statement of App and online service of VisorTech, the shortcomings continue. The privacy policy does not cover, as legally necessary, the product and several points in the field of “App” and “External Communications” suggest dubious privacy practices. A quote from the privacy policy, which also incorrectly links to the Chinese version in Google Playstore, illustrates the lax handling of the manufacturer with minimum legal requirements: “Without revealing the privacy of individual users, we reserve the right to analyze the entire user database and the user database commercial use. ”
Conclusion: Warning of use of VisorTech TSZ-580.fp
In addition to the risk of unencrypted transponder data, which allow any attacker who can operate a smartphone, to open the VisorTech-Lock, the Smartlock also has unencrypted data transmission, inadequate authentication, insecure storage of data and non-privacy-compliant handling of user data and other significant defects. Therefore, the AV-TEST Institute advises against using the VisorTech TSZ-580.fp. The deficiencies described in this test report were only determined as part of a quick-check. It can be assumed that with more intensive examination further security deficiencies might come to light.
The German retailer Pearl, who provided the Smartlock on request to AV-TEST, was informed with a notice period of two months about the security problem by using unencrypted transponder data and asked for proof as soon as this immediate danger would be eliminated. As part of the two-month commitment to non-publication, we received a revised version of the lock from Pearl. In this device at least the reported vulnerability of the transponder was fixed. The post-test showed that other gaps described in this review continue to pose risks. Likewise, the manufacturer left open whether he calls back already sold devices or at least notifies his customers. For this reason, the AV-TEST Institute is now publishing this test report to warn users of the VisorTech TSZ-580.fp. If you want to continue using the unsecure lock, you should at least refrain from using the transponder.
That’s why the rating can not be more than 0 out of 3 stars.

