For cybercriminals, the rapidly growing number of unprotected or, at best, poorly protected devices, are an easy and welcome target. The risk is borne by unsuspecting users of networked devices. They rely on non-existent legal requirements and the manufacturers‘ sense of responsibility and thus risk losing their privacy.
Find the complete Security Report on our website for free.
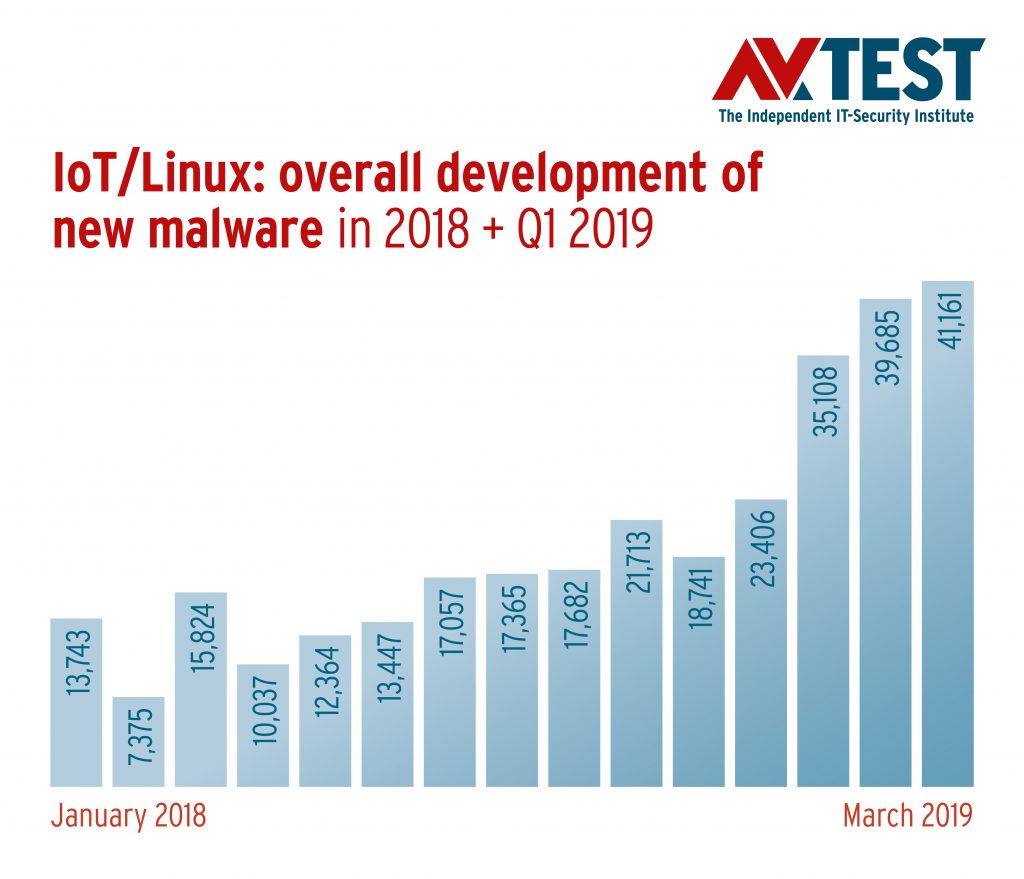
Distribution of malware under IoT in 2018
Given the fact that standard and compatible IoT systems must also run on the microcontroller level, mostly stripped-down Linux versions such as Canonical Ubuntu are used. In the last quarter of 2017, AV-TEST Institute‘s detection systems recorded a rapidly increasing number of newly developed malware for Linux-based IoT systems. In 2018, the number of new malware developments once again experienced a dramatic increase: 15,730 new malware programs for attacks on IoT devices and infrastructures were developed per month last year. And this already critical value for a rapidly growing group of devices, most of which are online either without protection or with poor protection at best, is dramatically exacerbated in the first quarter of 2019: Within three months, the IoT malware sample rate doubled to its current high mark of over 40,000 new samples per month
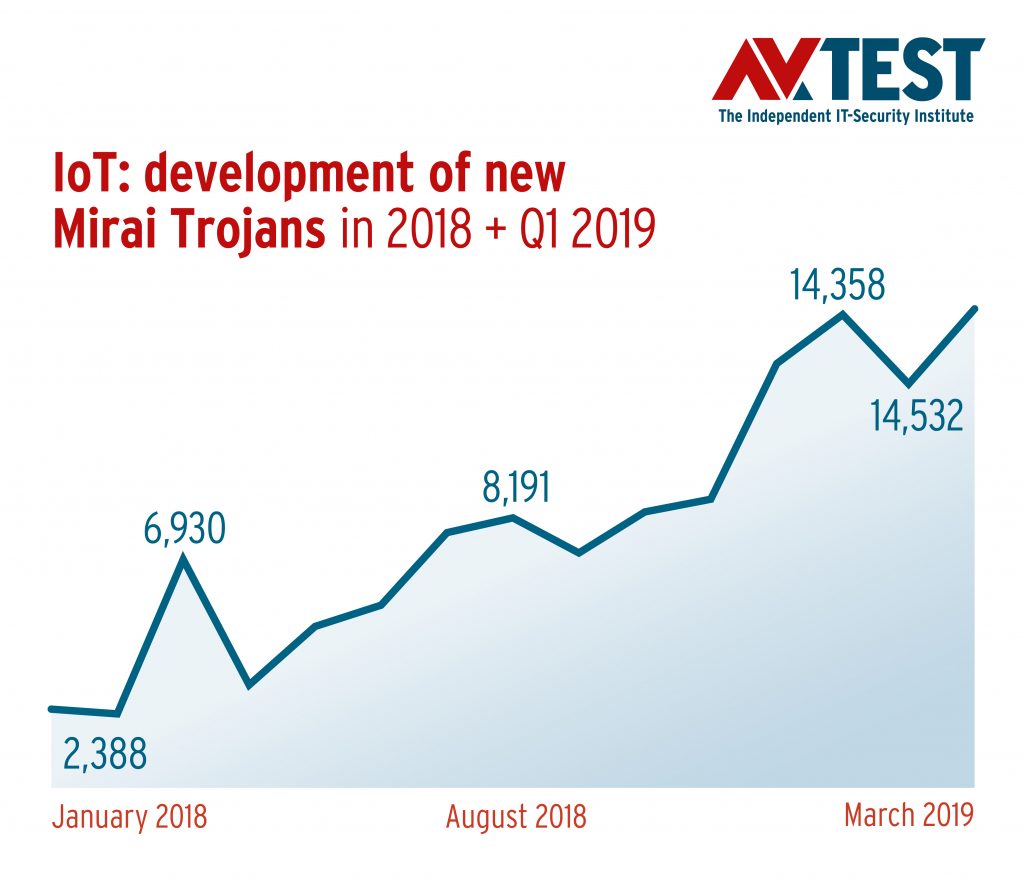
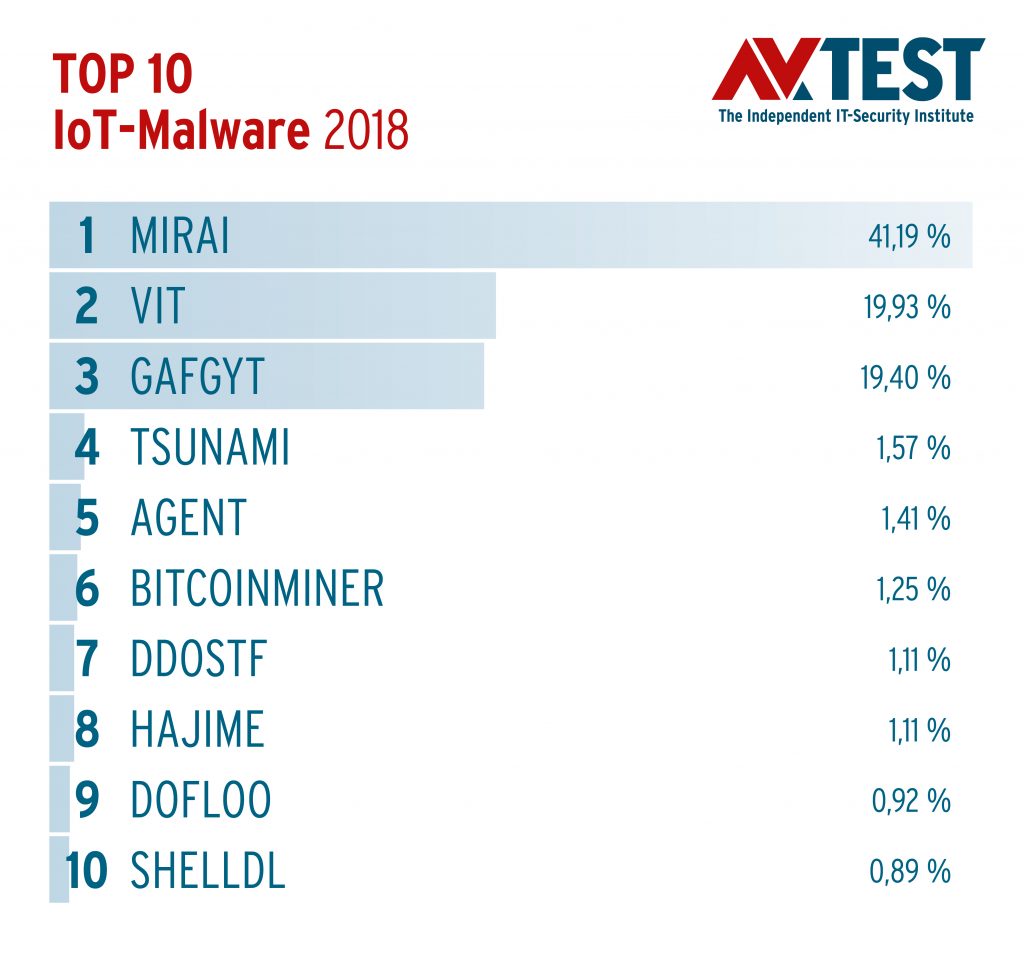
But of course, other IoT operating systems, such as the open source Contiki and RIOT OS systems, along with Google‘s slimmed-down Android version, Brillo OS, are also vulnerable to attacks. The majority of newly developed malware for IoT systems, at 57.59 percent in 2018, involved the category of Trojans. This was due in large part to an „old nemesis“, who already played a lead role in the security reports of the past two years: “Mirai“. AV-TEST‘s detection systems first detected the malware sample in August 2016, and in October 2016 Mirai already unleashed large-scale DDOS attacks against major online services in the US and Europe. Mirai obtained the computing power for this from a botnet of hundreds of thousands of hijacked routers, printers, webcams and online video recorders without effective authentication procedures and with poor or non-existent encryption.
High malware curve versus a low learning curve
Measured in terms of the development figures, the development of the Mirai malicious code for criminals still seems to be worthwhile. The Mirai code accounted for more than 40 percent of the total malicious code for IoT devices (41.19%) in 2018. Unfortunately, the steep development curve of Mirai samples does not indicate a commensurately high learning curve for device manufacturers, who should have been aware of these dangers since October 2016 at the latest. However, a response does not appear to be forthcoming, and criminals accordingly continue to deploy Mirai successfully for attacks on IoT devices and connected infrastructure. The sample numbers of the main malware for IoT devices have been exploding since the beginning of last year. With 78,186 variants, Mirai clearly leads the ranking, ahead of other IoT Trojans such as „Vit“ (37,807 samples), „Gafgyt“ (36,769 samples) and „Tsunami“ (2,959 samples).
One development that surely makes life easier for cybercriminals is the increasing number of known vulnerabilities in IoT devices and the increasing possibility of attacking them via automated malicious code. The available backdoors are increasing accordingly. Last year, a total of 188,754 of these gateways were available to attackers for Linux systems alone. In the first quarter of 2019, this figure had already reached 115,954! Other types of threats, such as digital blackmail or the failure of vital IoT devices, services and functions, are another horror scenario for the digitalized civil society. Although current measurements have recorded initial attempts in the field of ransomware, these cannot yet be identified as an acute threat, at least in terms of numbers. On the other hand, Mirai attacks that have already taken place in 2018, involving roughly 0.01 percent of total malware, indicate that a specialized ransomware code is not necessarily required for IoT-based blackmail models.
Trend 2019
In addition to the long-standing, systematic collection of new malware samples for IoT devices, which continued to proliferate in first quarter, especially for Mirai, Vit and Gafgyt, the AV-TEST Institute has been analyzing the systematic characteristics of attacks on networked devices with its own honeypot systems since 2017. These reveal alarming numbers: In the first quarter of 2019 alone, there were a total of 3,200,000 attacks on the open IoT systems on the Web! In 41,213 cases, attackers tried to use malware programs to hijack the hardware placed on the Web. In 71.44 percent of all successful malware infections, AV-TEST engineers identified the Mirai code as the attacker‘s weapon of choice. In addition, Linux shell commands were often used to access the SSH/Telnet connection of the honeypot systems. In most cases, automated attacks were used to circumvent a possible password protection of the devices. The user names used most often in these attempts were „root“ and „admin“; brute force attacks on passwords most frequently use the terms „admin“ and „default“. This indicates, among other things, how important it is for manufacturers of IoT products to require that standard passwords be changed when customers install IoT products!
Non-existent standards and old security gaps
In a recent study, Juniper analysts estimate the total number of devices that will communicate with each other over the Internet of Things by 2022 at more than 50 billion. Compared to the level of 21 billion in 2018, the IoT cosmos is expected to more than double in just four years. The strong growth of the Internet of Things is affecting virtually all areas of our lives and is bound to also change our working environment, along with our leisure time. Such devices and services can make life easier for us, yet the exact opposite may also be the case. Because more and more devices, which we use as a matter of course in everyday life and some of which we would never suspect, are connected to the Internet. Instead of television sets, cameras and smart language assistants, in the near future, we will begin to see everyday objects such as vacuum cleaners and tooth brushes collecting information about their users and sending it to the manufacturers and their related business partners.
The fact is that security experts like the experts at the AV-TEST Institute have been warning about the dangers of vulnerable IoT devices for years, but these calls continue to fall on deaf ears. And it is precisely the manufacturers of end-user products, especially those that do not originally come from the IT industry, who are committing the same errors that were made 30 years ago with PCs and 10 years ago with smartphones and other mobile devices: Poor or even unprotected access accounts, weak or often non-existent encryption when storing and transporting data, out-of-date software and inadequate or even no security update service, all add up to a field day for attackers for the majority of devices, and the trend is continuing.
Security by Design has a sign
On the other hand, you will find suppliers of IoT devices and services, for which the security of devices and privacy of customers has been an important concern for quite some time. These manufacturers have their products tested and certified by independent testing institutes such as the AV-TEST Institute. Secure IoT products from manufacturers who implement “Security by Design” can be recognized by the AV-TEST certificate.

