Under the Eufy brand, the Chinese technology company Anker has marketed not only vacuum cleaners and robot vacuums, but also smart surveillance cameras for some time now. We subjected the eufyCam 2C to our Quick-Check and evaluated whether the solution designed for high data protection can keep its promises.
Update 11/30/2022: TheVerge reports that a vulnerability has become known that allows attackers to directly connect to the camera stream of the Eufy Cams via the Anker cloud servers using VLC and without authentication. There is no detailed description of the vulnerability, but it can be considered critical even with the known information. The only possible “saving grace” is that the attacker must know the corresponding user ID in order to connect to the camera stream. However, this ID does not just an increasing number or otherwise easily derivable, so that a targeted exploitation should be practically difficult. Since we only had a loaned device available for our short test, we cannot verify the vulnerability or even its fix at this point. During the Quick-Check (time frame only a few days), we only check a short checklist of the most important security features, so the vulnerability did not stand out directly here, even though we could already identify indications for possible problems.
Technical data
The eufyCam 2C set consists of a base station (Homebase 2) and two cameras. Eufy advertises 180 days of battery life, 1080p FullHD resolution and IP67 weatherproof cameras.
Unlike many other surveillance solutions, there are no monthly fees with Eufy. All video recordings from the cameras are processed locally on the base station and transmitted and stored with AES 256-bit encryption, according to the manufacturer. For this purpose, 16GB are available on the base, which can be expanded via USB stick. In addition to an infrared LED, the camera also features a LED spotlight and microphone and speaker for two-way communication via the app.
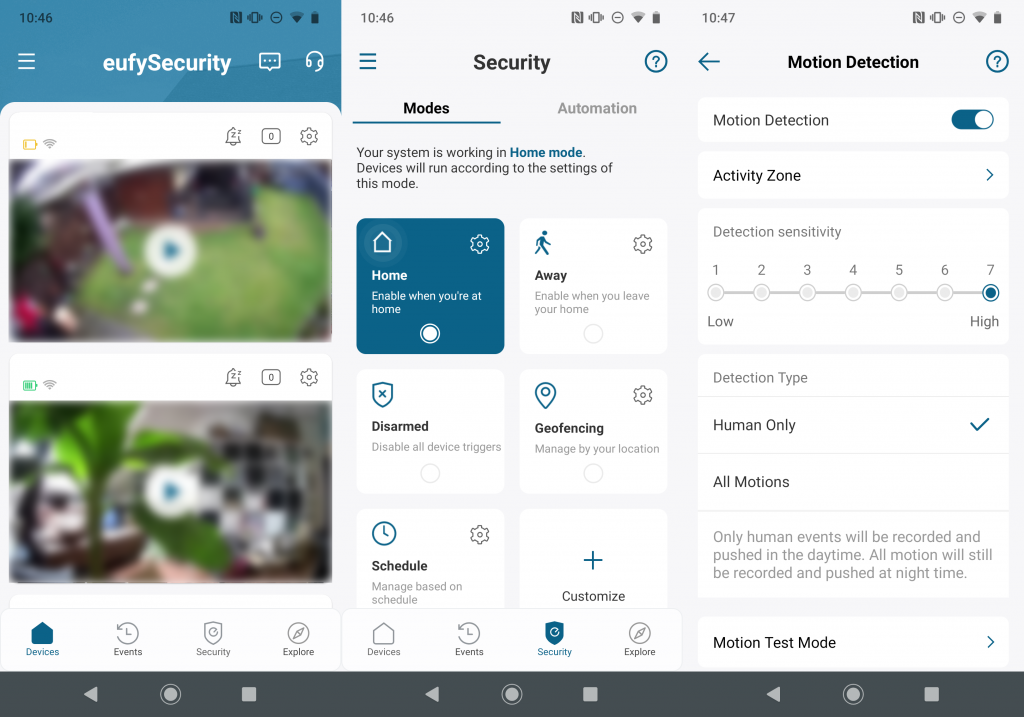
With daylight, the cameras also have human detection so that passing leaves or animals do not trigger a notification via the app. The Homebase 2 can also be expanded into an alarm system with additional sensors.
App
The Eufy Security App (Android, iOS) is largely obfuscated, making it more difficult for attackers to understand security-relevant functions, for example. Certificate pinning has also been integrated so that connections to Eufy and the Amazon AWS cloud infrastructure are particularly protected.
The static analysis identified two trackers in the app (Google CrashLytics and Firebase Analytics) and showed that several third-party modules are integrated into the app, partly also as shared object files. Unencrypted communication is explicitly allowed by build option in both the Android and iOS apps.
The app only allows a simultaneous login with one account. If you log in on a second device with the identical credentials, you will be logged out in the other app with a notification. The login can be further protected with the optional 2-factor authentication, and other Eufy accounts can also be assigned permissions to the cameras or the system itself.
Local and online communication
In the network analysis of the Eufy Homebase 2, it turned out that some network ports are open. One of them is an integrated DNS server, which was probably left active by mistake, just like the other open ports. The DNS server itself queries the DNS server obtained via DHCP when a request is sent to it. No communication with the base station was possible via the other open ports at the time of testing; furthermore, our analysis system could not perpetrate any successful attacks via them.
The Eufy app contacts a few servers in different countries or continents within a short time. (Singapore, Germany, China, USA) The communication between the app and the cloud hosted at Amazon AWS was TLS1.2 or partially TLS1.3 encrypted.
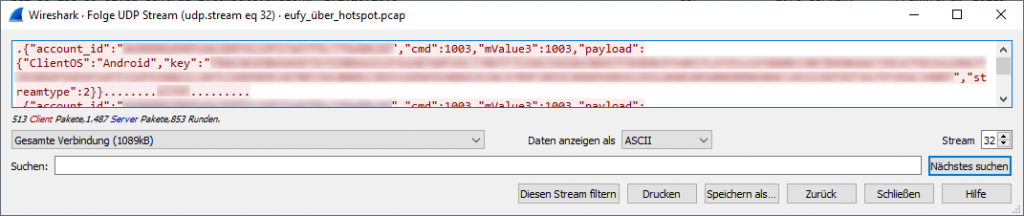
Streaming of the camera image was via UDP, AES-256bit encrypted according to the manufacturer. However, when the camera stream was started, the account ID and an API key were transmitted unencrypted, regardless of whether it was streamed directly locally or online over Amazon servers. Even if the key only seems to be valid for a limited time, Eufy should correct this as soon as possible.
The EufyCam 2C itself is connected to the base station via a WPA2-encrypted Wi-Fi with a hidden SSID (OCEAN_XXXXXX, after the parent company Oceanwing, Shenzhen). The camera system was not very impressed by a deauthentication attack on the ESSID or the EufyCam – unlike other wireless cameras that we have already tested.
Privacy
During the privacy analysis, it quickly became apparent that Eufy should revise and consolidate its privacy statements. On the one hand, the English-language versions linked in the Google Play Store, Apple Appstore, and the apps differ from the one available on the manufacturer’s site in several points. For another, the German-language version, which is only available in the app, is 2 years older than the others. (August 2020 <-> September 2018)
In the context of the further analysis, we only used the English-language privacy policy of the app (as of August 10, 2020). According to it, all image captures and biometric data (person recognition or recognized face displayed in the app) taken by the EufyCam 2C are only stored on the Homebase 2.
The collection of usage data cannot be disabled in the app. Furthermore, the IMEI of the device is used for advertising purposes, for example to get data from advertisers and to place ads in the app. The user does not seem to be able to refuse this, either. The storage period of data is only mentioned quite vaguely. It would be good to know, for example, how long location data is stored, which is used for the geofencing feature, among other things.
The EU-US Privacy Shield was declared invalid in July 2020. Unfortunately, the privacy policy still refers to this. With regard to the storage location of data, it also bears ambiguities. In part, it talks about data being stored in the Anker data centers (China, USA, Germany), but in other places it says that data recorded in the European Economic Area would be stored exclusively in Germany. This is at odds with our findings.
Conclusion
With the EufyCam 2C, Anker has launched a well thought-out product in terms of both security and data protection. Unfortunately, however, we found several issues in both the cloud communication and the privacy analysis that Anker needs to look at promptly in order to fulfill the product’s promises.


Pingback: eufyCam 2C in the security test - BostonHiTech.com - Latest Technology News