In addition to all the things that were unimaginable just a few decades ago that you can do on a modern smartphone, one app category in particular is of course still a big hit: games! People are always playing games, young and old. And that is precisely why games are particularly interesting when it comes to collecting a wide variety of data from different population groups. In the games category, the supposedly free games are of particular interest, because as the saying goes: if a product is free for you, you are the product…
As always with our Android App Privacy test format, when analyzing the selected applications, it is of course particularly important to us not only to compare compliance with the requirements of the GDPR, but also to evaluate the practical impact of using an app on the user’s privacy. The collection of data that is not actually required for functionality, the open information and communication of this based on the privacy policy and potential violations of the GDPR that result from this play a particularly important role here. Of course, the sheer volume and type of data collected is also not irrelevant.
The selection
The top lists that are displayed to a user in the Google Playstore vary greatly from region to region and user to user, because the display is naturally tailored to the user and is constantly changing anyway. We therefore selected 10 games from the top 30 of the “Most successful” category of free games relatively randomly in order to obtain a good sample.
The games (with package name, tested version and link to report overview) are as follows:
Royal Match (com.dreamgames.royalmatch v22168)
Candy Crush Saga (com.king.candycrushsaga v1.279.2.1)
Gardenscapes (com.playrix.gardenscapes v7.9.0)
Fishdom (com.playrix.fishdomdd.gplay v8.1.2.0)
Whiteout Survival (com.gof.global v1.18.7)
Township (com.playrix.township v19.0.1)
Legend of Mushroom (com.mxdzzus.google v2.0.30)
Total Battle (com.totalbattle v327.10.2205-arm64-v8a)
Slotpark (com.platogo.pmp v3.57.4)
Hero Wars (com.nexters.herowars v1.202.000)
Trackers and permissions
In order to assess the data collection possibilities of an application, it makes sense to first look at which known trackers, i.e. software modules that serve the sole purpose of collecting usage data, are contained in the application and which permissions they request. Both are relatively easy to find out statically: To identify the included trackers, we use the free database from the Exodus Privacy Project. This allows us to identify known trackers in the examined applications and at the same time, for later analysis, we also receive the network detection rules that allow us to assign observed communication to a specific tracker in the dynamic analysis. In addition, we also use other tools that recognize third-party software modules that are not or not yet recognized by Exodus.
We can then simply look at the requested permissions in the manifest of the Android application and thus estimate in advance what data could theoretically be collected. In addition, they give us a first impression of how collection-hungry the application in question could be – purely in terms of the functionality of a classic mobile game, not very many permissions are actually required, but if a lot of permissions are nevertheless requested here, this already allows certain conclusions to be drawn.
As expected, the games examined are not reticent in this regard either: the number ranges from a moderate 15 required permissions to 30. We have actually seen much worse here, but compared to the IoT-related applications we usually examine, this is of course relatively high – especially when you consider that the IoT applications here often also require permissions for Bluetooth and localization services, for example, which a game should not normally need. It is particularly noticeable (but not at all surprising) that all of the applications examined request all permissions related to access to the Google AD-ID. This ID is a unique identifier that can be reset by the user, which is provided by Google’s advertising services and enables applications to track user behavior for advertising purposes. Privacy should be preserved here, as no explicitly personal data is linked to the ID, but how private user behavior is in itself is probably a matter of definition.
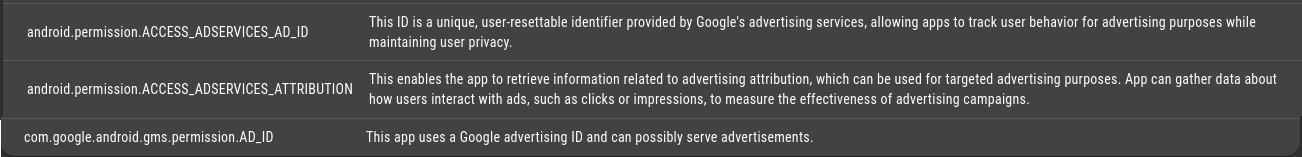
What is also interesting about the permissions around the AD-ID is that these are in the “Normal” category on the Android system side and therefore do not require confirmation by the user in order to be granted. Of course, this is not the apps’ fault, but they are happy to take advantage of this offer.
Apart from this, some of the game apps examined request rather questionable permissions that are difficult to explain with the functionality of the app. For example, 6 out of 10 apps request read and write access to the external memory. And one app (Whiteout Survival) even requests access to the phone status (android.permission.READ_PHONE_STATE). An application with this permission can determine the phone number and serial number of the phone, whether a call is active, which number the call is connected to and so on – legitimate interest questionable.
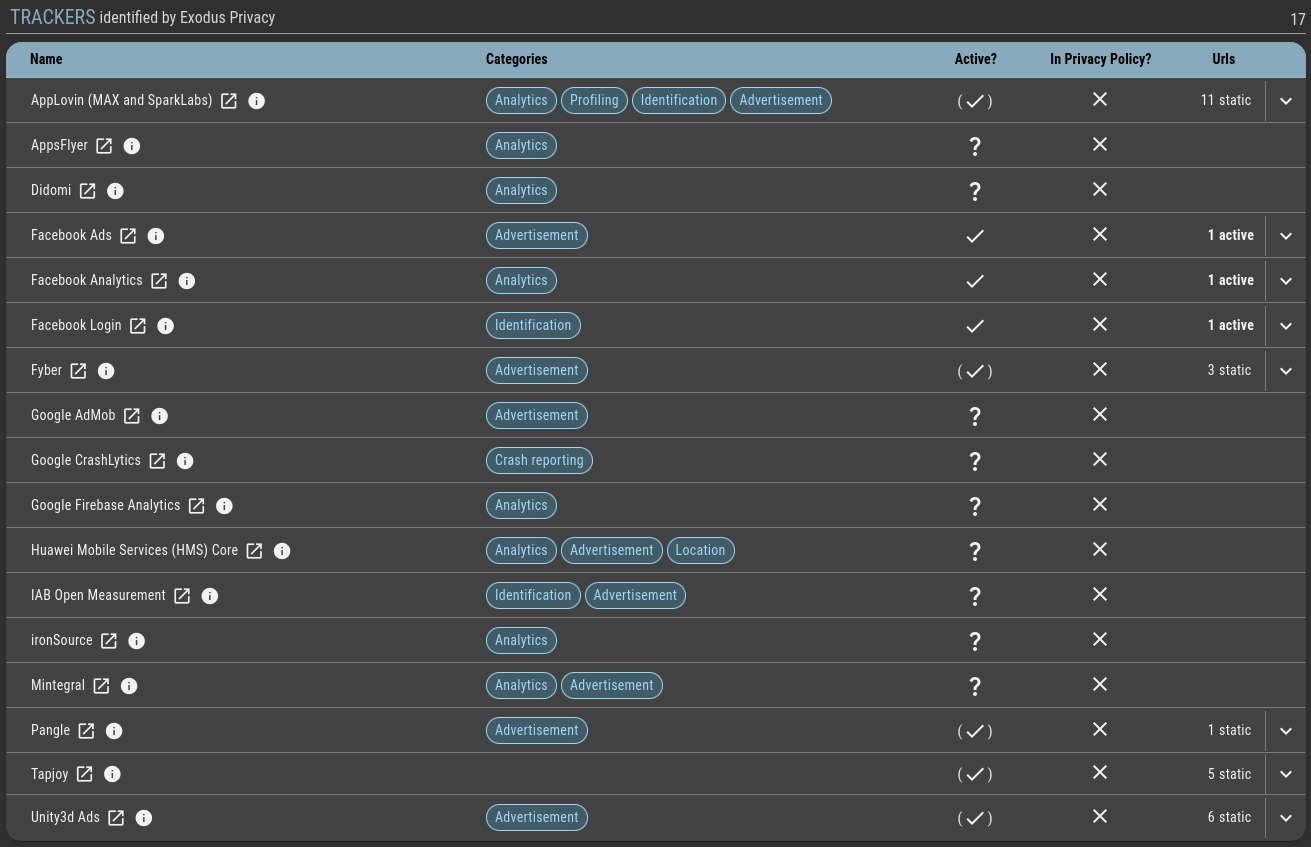
In terms of the trackers included, the apps we analyzed really hit their stride, as expected: the sheer number ranges from a remarkable 7 to 17, although lower numbers would have been an absolute surprise. In total, we were able to identify 26 different trackers across all the game apps examined – AppsLovin, AppsFlyer, Facebook, Google, you name it.
There is nothing wrong with the use of these trackers, as they are of course one of the main sources of income for these games, and from a GDPR perspective, there is nothing wrong with them. At least not as long as these trackers and what exactly they do are communicated to the user in detail, and this is where things quickly become shady: none of the applications examined mention all the trackers they contain in the associated privacy policy. In some cases, not a single one is mentioned by name. To be fair, it must be admitted that in most cases the privacy policies are quite detailed (more on this in the “Privacy policy” section) and also contain the essential information. However, the most important thing for the user is not only what data is collected, but also to whom it is sent.
Privacy policy
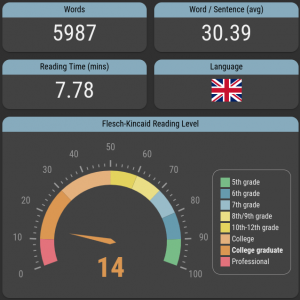
There is not really much more to report on the content of the privacy policy: All applications provide a privacy policy and in most cases these are also quite detailed and contain at least the essential information. Of course, as we have become accustomed to, the readability of all of them is not necessarily outstanding and even the analysis using the readability index we use (Flesch-Kincaid) does not find any text here that does not require at least a university degree to be fully understood. However, as this is in the nature of legal texts, this can hardly be criticized here. Otherwise, there were classic problems here and there, such as inconsistencies or even quite different versions of the privacy policy in the store and displayed in the app. Unnecessary and certainly not user-friendly, but we also see this quite often.
Communication
When examining the communication of the selected game applications, this time we not only looked at where the communication goes (for example, to determine the activity of certain trackers), but also looked at the ratio between the necessary amount of communication and the additional communication (for user analysis, advertising purposes, etc.). We also looked at when the communication takes place, as this can also play a decisive role in GDPR compliance. More on this later.
In order to determine the relationship between the communication that is absolutely necessary for the functionality and all additional communication, we looked at all the communication per application observed in the test and assigned each individual request, each GET and each POST to the identified trackers. As mentioned above, the network detection rules for this are obtained directly from Exodus Privacy. What remains at the end can be seen as the necessary communication with the app provider. Of course, not everything in this communication has to be “necessary”, but in order to decide this, every bit of transmitted data would have to be analyzed and categorized.
Of course, we had already assumed in advance that communication for analysis and advertising purposes would make up a large proportion of the overall communication. However, the actual result surprised us. In 8 of the 10 apps examined, almost 100% of the communication via the Internet is used for analysis and data collection. The other two apps had values of 90 and 75% respectively.
From the point of view of the GDPR, this is of course not really a problem, (again) as long as the user is informed about this in the privacy policy and (important!) BEFORE any data is collected. In practice, it should work like this: The user installs the relevant app, starts it and the very first thing they see is the privacy policy, which they can then confirm or reject. No data collection may take place until the privacy policy has been accepted. And this is where the apps we examined do not comply at all. In virtually all cases, we were able to detect considerable communication activity before the user even had the chance to read the title of the privacy policy, let alone accept it in full. Data was definitely already being collected here before consent was given to the data collection.
Verdict
Of course, the result of our test here was to be expected in advance: It was clear from the outset that the apps examined in this category would exhibit a certain collecting frenzy, as this is actually their sole purpose. However, we were still surprised by how much data is collected here and that, strictly speaking, this is not done in compliance with the GDPR. We are sure that most or even all app providers are not even aware of this and that it is difficult for them to understand what the many integrated trackers are doing, for what purpose and when. Of course, this does not exempt them from ensuring that their applications are GDPR-compliant. The test also shows that in this area, compliance with the legal requirements is still not checked closely and rigorously enough.










