Against all opposition and boycott attempts, the controversial FIFA World Cup is in full swing, and even though the general interest seems rather moderate for obvious reasons, hundreds of thousands of fans from all over the world once again traveled to Qatar to cheer on their football heroes. The Qatari government obliges every entrant to use two official mobile applications in order to ensure an uncomplicated stay. Certainly not without reason, many users therefore look with suspicion at the mandatory apps. But what exactly do they do and what impact do they have on the user’s immediate privacy? We take this opportunity to analyze the two apps in our brand-new Android App Privacy analysis in order to answer these questions.
Purpose and features
The first of the two apps, Ehteraz (com.moi.covid19; examined in version 12.4.7), is the official contact tracking app of the Qatari Ministry of Interior and Health. In principle, it fulfills the same tasks as the Corona-Warn or CovPass app in Germany – no store, no restaurant and probably no airport can be entered in Qatar without it and the proof of vaccination stored in it. Its use can thus safely be described as mandatory.
The second application, Hayya (com.pl.qatar in version 8.1.1.3628), promises “the ultimate fan experience during the FIFA World Cup – all at the touch of a button!”. Through it, the official accommodation agency can be used to find and book hotels, buy match tickets or even find places of interest for sight seeing. In addition, the app implements the digital version of the so-called Hayya Card, which is an entry permit, bus and metro ticket, and fan discount card all in one – so here, too, there’s practically no way for fans in Qatar to get around using it.
It should be noted that both applications can only be used to their full extent in the Qatari mobile network and with valid passport data. Since we were unable to convince any of our colleagues to voluntarily provide their passports for an experiment, our investigations are accordingly based only on the functions that we were able to execute without valid passport data.
Permissions
In the first step of a static analysis of a mobile Android application, it naturally makes sense to first get an idea of the basic possibilities of an app. The requested permissions provide a first rough overview of what the application can possibly collect, process and access.
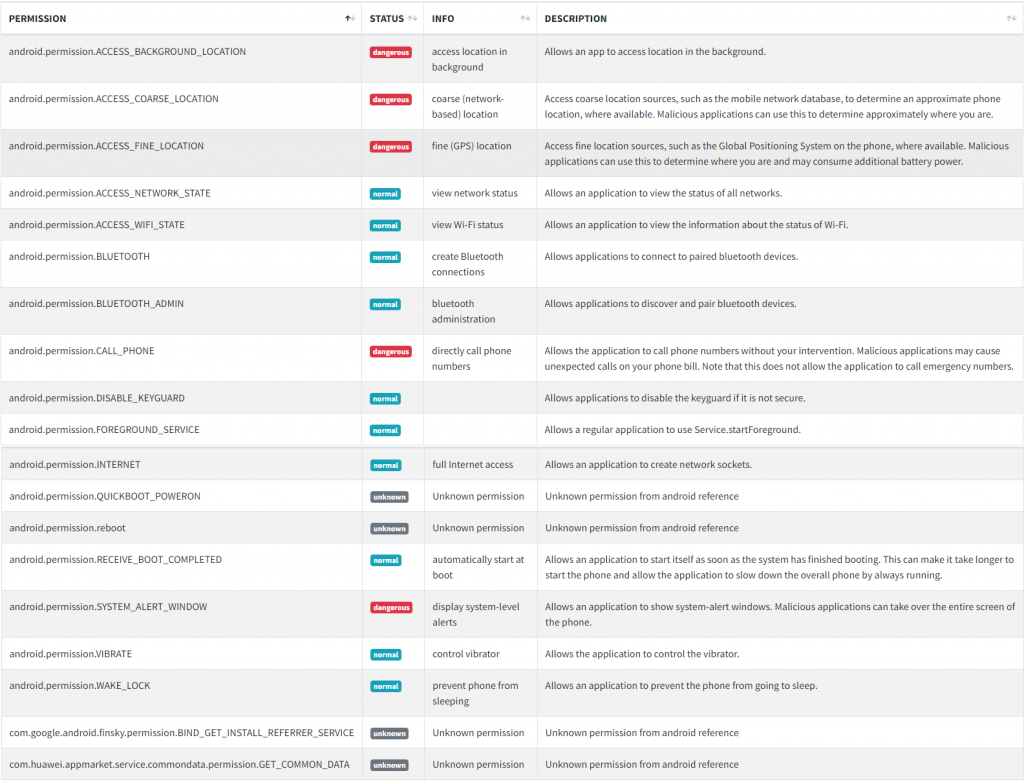
In this area, both applications initially appear quite inconspicuous: The number of permissions that can potentially be requested is limited, and the type of permissions does not directly suggest excessive data collection: Both apps can access location data and have access to WiFi and Internet – both not surprising considering the intended functionality. Just like the Corona-Warn app counterpart, Ehteraz, also has access to Bluetooth functions, which is also not surprising. However, both apps also have permissions that might at least seem suspicious to the user. For example, the Ehteraz app contains the com.huawei.appmarket.service.commondata.permission.GET_COMMON_DATA permission, which suggests the presence of the Huawei Android Analytics Kit. This basically allows the collection of all device metadata, including all possible information about the device itself (brand, model, ROM/OS version, charge level, memory usage, etc.), but also, for example, the user’s Advertising ID and application usage statistics. Even though the presence of the analysis kit alone is certainly not proof of excessive data collection and this is not uncommon in commercial apps, the question why it should be needed for a non-commercial, official app for contact tracking naturally arises.
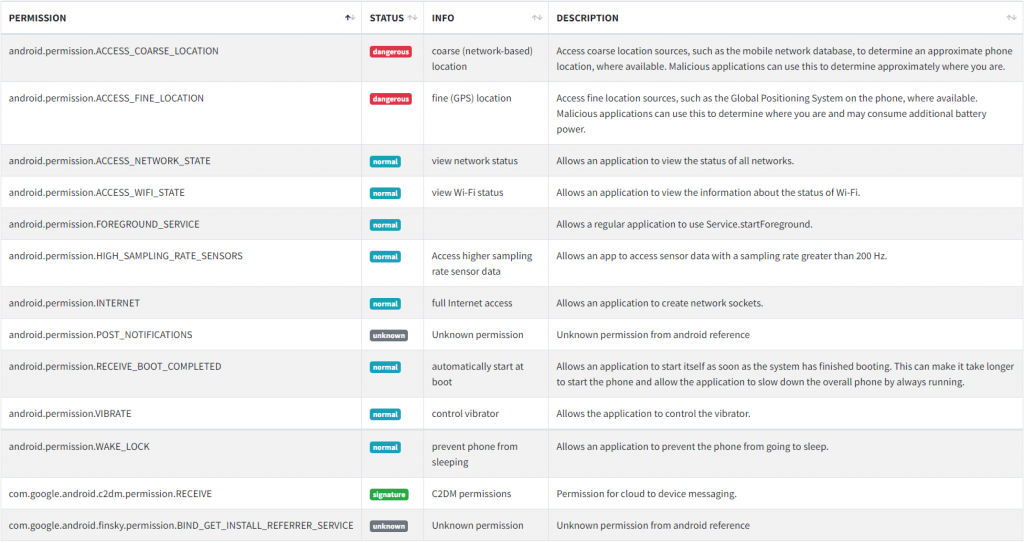
In the Hayya app, which actually gets by with quite slim permissions, only one special permission stands out: android.permission.HIGH_SAMPLING_RATE_SENSORS. This allows the application to request data from the device sensors, such as acceleration and gyro sensors, at the highest possible sampling rate above 200Hz. With the intended function of the application, the question also arises here why this data is relevant at all and additionally even with the highest possible precision.
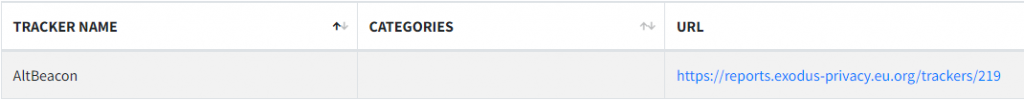
Trackers
The two apps actually differ to a greater extent in terms of the included tracking modules. Where the contact tracking app Ehteraz (besides the presumed Huawei kit) only contains one tracker, Hayya has a handful of trackers included. The AltBeacon module actually serves the app’s functionality. It can be used to implement so-called Bluetooth beacons that interact with each other and can detect each other. This way, the entire contact tracking can be performed via Bluetooth in the Ehteraz app. Of course, the tracker could also be used for user tracking, but we do not want to assume this without concrete evidence. However, there are reasons why the Corona-Warn app, for example, implements this functionality without the use of third-party modules and open source.
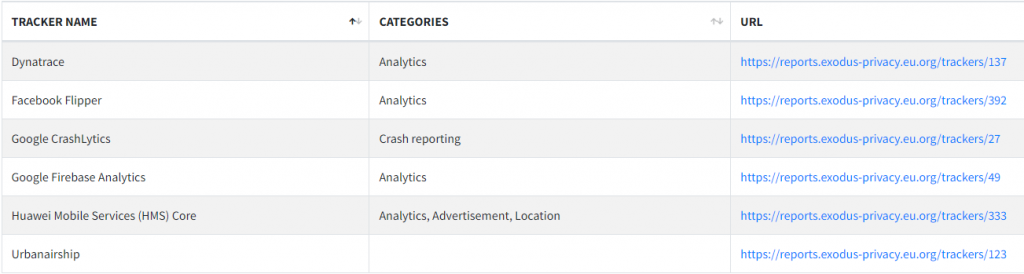
The Hayya app then contains a whole list of analysis and localization tools in comparison, but that is not surprising in an app that is of course supposed to implement commercial functionality. Google trackers can be found in a large number of apps nowadays, and the appearance of a Facebook tracker does not surprise anyone here either. What these trackers can and should do is well known by now. The Dynatrace module also implements analysis options, but they also play a role in terms of security. The Huawei kit has already been mentioned and also serves the aforementioned purposes. The Urbanairship tracker is a bit rarer, but also not uncommon. It also serves various analysis purposes, among other things.
Overall, the Ehteraz app naturally looks tidier for obvious reasons, but the Hayya app also does not appear to be more conspicuous than average here purely based on the observation of the included trackers and the app’s intended goal.
Communication
The two apps also differ fundamentally in this area: If you only look at the unencrypted HTTP communication of both apps, for example, you will see exactly one IP the Ehteraz app is communicating with and transferred data that does not necessarily appear critical. The Hayya app, on the other hand, communicates to dozens of IPs with a lot of transmitted data and user information in the same test. For comparison: In the test report for both apps, the part about unencrypted connections of the Ehteraz app fills exactly two lines – an IP addressed twice, thereby transmitted, the current date. The same section for the Hayya app occupies 64 pages. However, it is only fair to note that most of the communication takes place with Google servers. An activity of the Huawei and Facebook trackers could not be detected here.
Privacy policy
The privacy statements of both applications can best be rated as “okay”: They are fairly detailed and readable, but not very easy to understand. They contain the most important information about data collection, storage and sharing, but do not mention any of the included trackers by name. Even for the suspect permissions that can be found, one searches in vain for an explanation, justification or even mentioning. We have certainly seen much better privacy policy statements in this area. But we have also seen much worse.
Verdict
It certainly cannot be denied that both applications and their mandatory use give reason to criticism and suspicion. The fact that the associated privacy policy statements do not take the opportunity to dispel any doubts certainly does not help much either.
Overall, the Ehteraz app performs much better than the Hayya app in the Android App Privacy analysis. It has relatively manageable permissions and therefore also a limited potential feature set. The fact that Huawei’s analysis kit is included does not seem absolutely necessary here, but excessive data collection cannot be directly assumed because of that. The dynamic analysis of the communication does not show any indications in this regard and the app behaves inconspicuously. However, it has to be noted that the application could only be tested to a limited extent, since the full functionality is only available in the Qatari mobile network. Only a full code analysis would help here, but is not trivial with an app size of over 60MB.
The Hayya app then looks like a typical commercial app in comparison, as you can find thousands of them in the Playstore. It also does not differ much from other “sales apps” in terms of functionality and the obviously collected data. In principle, it would not be any more conspicuous than any other app from this category. Normally, however, the user has the choice whether to use these apps or not – with the Hayya app, he does not have this choice. In addition, it is still questionable whether the collected data is used exclusively for advertising purposes.
