Introduction
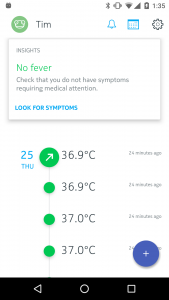
In the recent past we tested the new Nokia products Activité and Body Cardio. In the following Quick-Check we will report on the security of the Nokia Thermo, a contactless Bluetooth- and WiFi-capable clinical thermometer, which provides treatment suggestions after measuring the temperature and entering symptoms.
Setup
In order for the thermometer to measure the temperature at the push of a button, it must first be paired with the corresponding app. During initial setup, you can choose whether the measurements should be transferred to the smartphone via Bluetooth only, or whether they should be synchronized directly with the Nokia account via WiFi. In both cases, the data is stored and processed on Nokia servers.
Firmware update
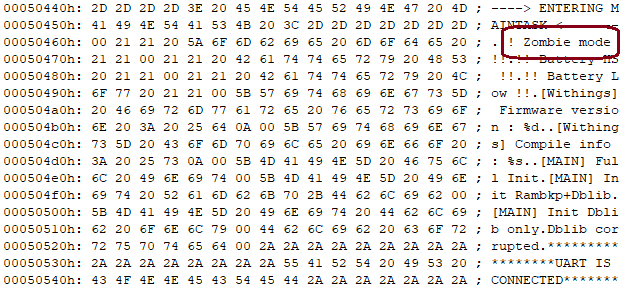
At the initial setup it was noticed that the firmware update is downloaded via a HTTP connection.
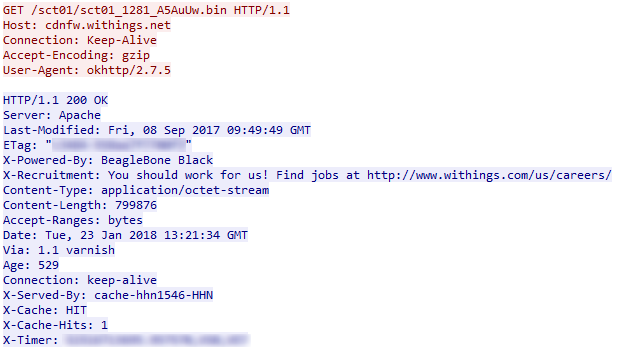
The update file itself is encrypted with a few plain text passages. Nevertheless, when downloading via an unencrypted HTTP connection, there are manipulation possibilities which would be impossible or very difficult to manipulate in an encrypted connection.
Online communication
The measured data of the thermometer is sent to the Withings or Nokia servers TLS 1.2 encrypted. Unencrypted connections beyond the firmware update could not be detected. The connections of the Thermo are also protected against man-in-the-middle attacks and therefore offer very good protection.
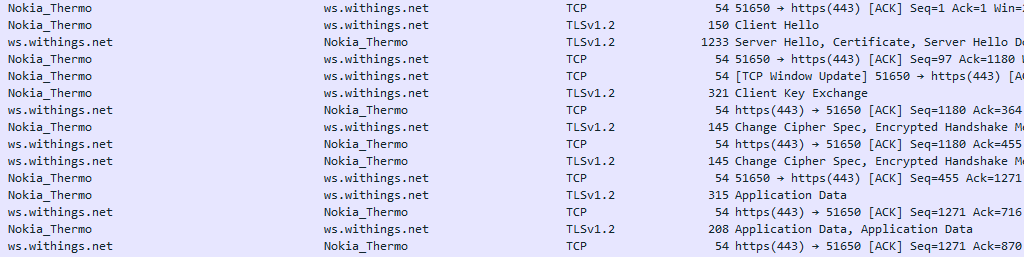
The Internet communication of the Thermo App is also TLS 1.2 encrypted and thus protected against simple man-in-the-middle attacks. In the absence of a Certificate Pinning implementation, however, such an attack could be possible if the attacker could install a certificate on the owner’s smartphone.
Local communication
If communication via Bluetooth is selected during setup, the thermometer and app communicate primarily via RFCOMM, a Bluetooth protocol for emulating a serial connection. Unencrypted data could be found in the communication, for example the user’s name or the session ID for uploading to Nokia. However, since the connection of both devices was invisible or hidden from other devices at any time, this is not considered negative.
App
The Nokia Thermo App is extensive and complex obfuscated, making it difficult to understand the decompiled code. Nevertheless, our researchers were able to take a look under the hood of the app. For example, all measured temperature values are stored unencrypted in a local database located in the protected app storage. This makes it possible for the app to display the temperature values even without an active internet connection. It is noticeable that the password is not encrypted or stored in plain text, but hashed with MD5. We have not seen this approach in Android very often. However, it is perfectly valid, although MD5 is no longer considered safe and many rainbow tables already exist for such hashes. However, this does not lead to any devaluation, because the smartphone would have to be rooted before other applications can access these values. A TLS-encrypted connection is established for communication with the Nokia servers, but no certificate pinning is used in the app.
Privacy
The Nokia Health solution’s Privacy Policy describes exactly what information is collected and for what purpose. Furthermore, it is easy to read from 19 years of age. Data is rarely shared with third parties and only with the explicit consent of the user. Furthermore, the data is only stored on the user’s continent. (Europe – Ireland, North America – USA, South America – Brazil, Asia – Japan/Singapore, Australia)
With eHealth products such as the Nokia Thermo, we pay particular attention to privacy. Nokia is doing a good job here and does not leave any details missing in its privacy policy.
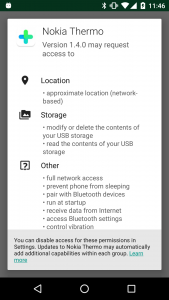
The permissions of the Android app are limited to the minimum necessary scope:
Conclusion
The Nokia Thermo offers a privacy friendly, secure solution for contactless body temperature measurement. However, downloading the firmware updates via unencrypted channels leads to a deduction of points, which is why we award two out of three possible stars.

