“On the way and yet at home.” This is the slogan used by the German product DoorBird. A door intercom system that allows the user to speak with visitors from anywhere via the smartphone, view them and open the door (and with the help of a smart lock). The implied security risks are, of course, intuitively accessible to everyone at this point. One reason for the AV-Test IoT-Laboratory to look at the security concept of the DoorBird and to analyse potential vulnerabilities.
Application
The mobile DoorBird Android application (com.doorbird.doorbird; version 4.20) was examined. The static analysis of the app found indications of potential problems in SSL security. According to this analysis, the certificate checking could show possible weak points and thus enable potential attackers the possibility of man-in-the-middle attacks. Theoretically, the weaknesses found in the code are also comprehensible, but in practice these must be verified in the analysis of online communication. Especially in the case of unconventional implementation of the certificate verification, the theoretical tests can be misleading.
Otherwise, however, the application does not provide any further grounds for complaint – the source code is mostly obfuscated, no sensitive information is stored unsecured locally on the smartphone, and no information is disclosed on the Android Logcat that could be helpful for an attacker in any way.
Online communication
The practical analysis of online communication does not confirm the clues found by the static analysis for possible weak points in the area of certificate verification. The monitored connections to the Internet that are established by the app and device were in all cases secured against simple man-in-the-middle attacks by TLS 1.2 encryption. The transfer of a firmware update was also adequately secured and showed no signs of a weak point.
Local communication
In this area, the analysis highlighted a number of points which we must consider to be of concern. There is reason to criticize the setup of the system: For the initialization, the DoorBird base station provides its own WiFi, which is secured, but only with the standard password “doorbird”. Since the communication that takes place during setup via this WiFi is unfortunately also unencrypted over HTTP, it is quite conceivable for attackers to listen to the setup process and read the transmitted user credentials as well.
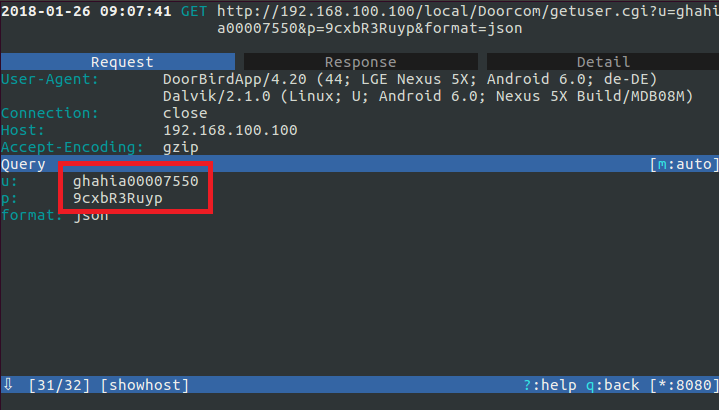
After completion of the installation, the door station communicates via the WiFi assigned by the user, but still unencrypted. The authentication, password changes and image transmission are also unencrypted and can therefore be read by all participants of the WiFi. In our opinion, this fact is not justifiable for a safety-critical application and thus also leads to a devaluation in this category.
Privacy
Privacy protection should be of particular importance for a solution that records images and sound (unnoticed) and offers cloud storage. Unfortunately, the quite extensive data protection declaration of the manufacturer refers only to the use of the DoorBird website and not to the use of the product. Therefore, no points can be awarded in terms of privacy protection.
The permissions of the Android app are limited to the required scope:
Verdict
The DoorBird system, consisting of the door station and mobile application, is actually quite solid from a security point of view – the app itself and the communication via the Internet are adequately secured and do not show any obvious, critical weak points after the initial analysis. However, there is a clear need for improvement in the area of local communication, be it for installation purposes or during operation. Furthermore, the privacy statement does not apply to the actual product or app. All in all, two stars have to be downgraded in our rating, so that DoorBird can be rated with only 1 of 3 possible stars.

