In addition to HD video streaming with night vision and HDR, the Nest Hello video doorbell from Google also offers face recognition and notifications on Google Assistant devices. In the security test, it was checked exactly what it is: a spyhole or a trustworthy companion in everyday life?
The Nest Hello door camera is connected to the lines of the former doorbell, so it is one of the few smart doorbells that still uses the internal bell. Battery changes as with other manufacturers are therefore not necessary. If no compatible bell transformer or similar is available, it can also be connected via an optionally available power supply.
Setup
As usual from Google, you don’t need any instructions for mounting and setting up the Nest Hello, because the app guides you through all necessary steps in detail. After a manual compatibility check with the built-in bell or bell transformer and subsequent assembly, it is ready for use.
Online communication
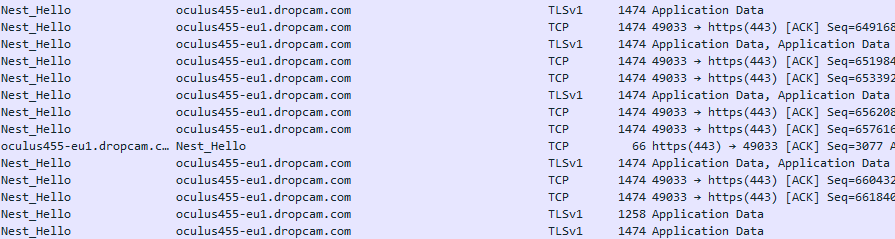
App and camera always communicate encrypted, exclusively via Google’s cloud service. Local communication was not observed during the test.
The video transmission of the Nest Hello to the cloud is only TLS1.0 encrypted. Since this version has exploitable vulnerabilities, this should be adapted promptly. For a successful attack, however, the local network or its transmission path to the Internet would have to be compromised.
If the video doorbell loses its connection to the cloud, a notification is sent to the owner’s smartphone. In case of a WiFi DeAuth attack or a power / internet failure, the user is informed about the status of the camera.
App
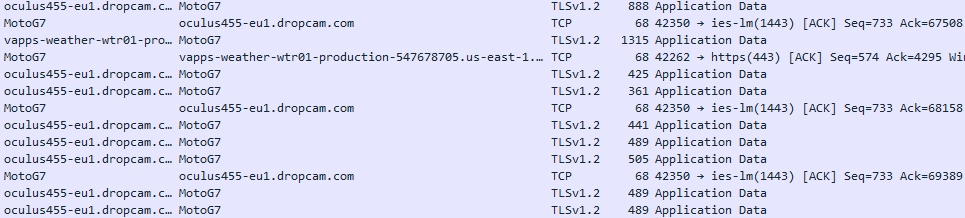
The Google Nest App always communicates TLS1.2 or 1.3 encrypted. Static as well as dynamic analysis did not reveal any significant vulnerabilities in the Nest app. Thanks to the implementation of certificate pinning, no user data can be intercepted in a man-in-the-middle attack, for example, even if the corresponding proxy certificate (by malware or similar) was installed on the owner’s smartphone.
The Nest app scans the local network for other connectable products, such as Xiaomi or IKEA Smart Home solutions.
Privacy
Since one of the last updates, the status LED of the Nest Hello can no longer be deactivated and is always on when the recording is active or someone is watching.
Especially due to face and packet recognition, the data recorded by the door camera is processed separately on Google cloud servers. In addition, sensor data on temperature and lighting level are available.
As usual with Google products, the privacy statement provides very detailed information about the recorded and processed data. It is only available in English.
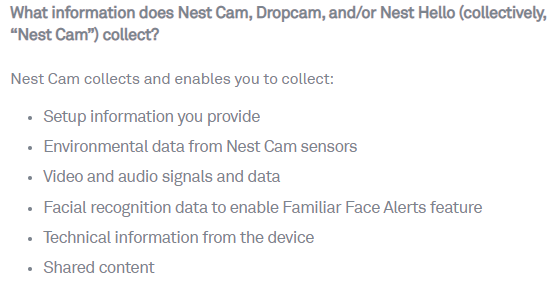
It is special that rights and duties of the processing according to privacy statement remain with the owner – Nest is only the data processor for picture and sound information. Hereby the owner of the Nest Hello is also responsible in terms of GDPR.
As with all cloud solutions, Google Nest shoppers should be aware that the device mounted next to the front door allows the data giant to learn many personal details about the everyday lives of all residents. One can imagine the insight Google gets when this data is consolidated with the interior information received from vacuum robots. We had already noted something similar in the test of the iRobot Roomba 980.
Conclusion
The Nest Hello video doorbell performs great in the test, always communicates encrypted in connection with cloud and app. The solution can also collect many points in the app area. The Privacy Policy is very detailed, but passes many rights and obligations on to the owner.
We therefore rate the Google Nest Hello with three out of three stars.


Pingback: Say “Hi” to Nest Hello - BostonHiTech.com - Latest Technology News
Pingback: The Importance Of Lot In Computer Science – Wovo.org