Even before the time of #stayathome, virtual reality has enjoyed increasing popularity in the recent past. Last but not least, the Oculus Quest from the parent company Facebook contributes a considerable share to this development. The self-sufficient VR headset does completely without cables (apart from the charging cable, of course) and, above all, without the help of a powerful computer that carries out the actual calculations in the background. In contrast to the higher-resolution, but much more stationary versions of the major competitors, the Quest thus has a decisive advantage for the so-called casual gamer group, where enthusiasm for the cable-based solutions has so far been very limited. In addition, the standalone VR headset, with a price starting at 450€, is also significantly cheaper than all competitors. And so the Quest and the software titles releasing on it have been selling like hot cakes since their release in 2019.
A Facebook product equipped with camera and microphone in hundreds of thousands of households? Reason enough for us to take a closer look at the Quest from a security and privacy point of view…
Technology
In the Oculus Quest, a Qualcomm Snapdragon 835 eight-core CPU works in conjunction with an Adreno 540 GPU from the same manufacturer on an Android OS version 7.1.1. The image is provided by two PenTile OLED displays with a maximum resolution of 1440 × 1600, each at 72 Hz. Tracking in six degrees of freedom is realized visually via four black-and-white wide-angle cameras on the outer corners of the headset. In addition, acceleration and proximity sensors as well as a gyroscope and magnetometer are integrated in the headset or controllers. Not surprisingly, the system communicates via Bluetooth and WLAN. The USB type C port is used to charge the headset and to realize Oculus Link, which can also be used to execute PC VR software titles.
Mobile applications
On Android (v55.0.0.1.118) as well as on iOS (v55.0), the applications for the Oculus Quest do not reveal any real weaknesses security-wise: With both versions, online communication is secured at all times by adequate encryption. Even the usual man-in-the-middle attacks come to nothing here. To bypass the implemented certificate pinning, the application itself must be patched. A remote attacker does not have this possibility and even with physical access to the smartphone, this would not be possible without further ado and, above all, would be difficult to do unnoticed.
Although the static analysis identifies some potential weaknesses in the general implementation of the applications, all of them are rather theoretical in nature and in our opinion do not pose a practical threat.
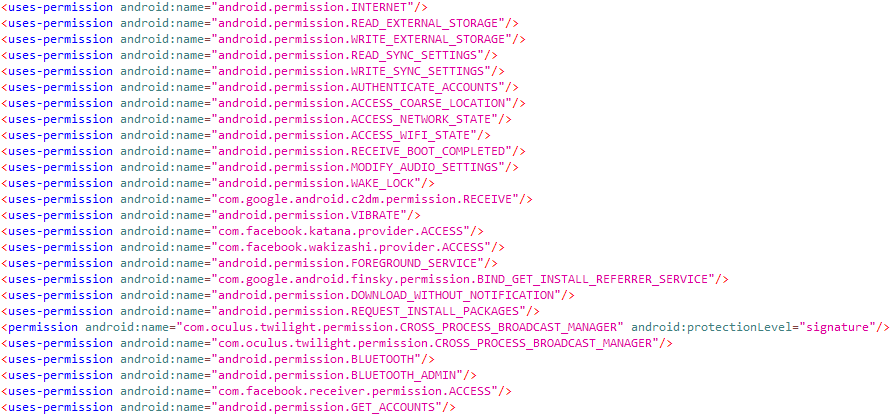
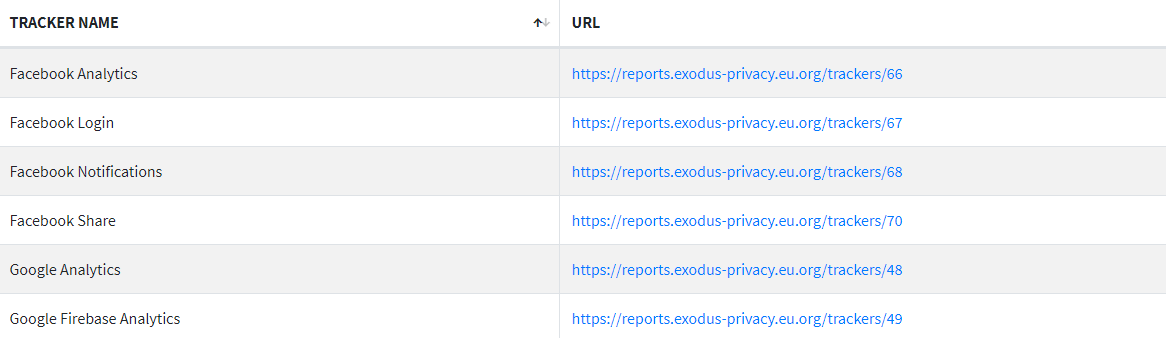
Unsurprisingly, the applications claim a fairly large number of permissions, which give them extensive options for action. These include the permissions for reading from and authenticating via the accounts known to the user device, reading and writing to external memory, reading and changing various system settings and downloading and installing additional content. Together with the various Facebook trackers and SDK’s (such as Instagram) included, it is safe to assume that a lot of usage data is collected here – which should not surprise anyone, after all it is still a Facebook product. However, from a purely security point of view, there is no reason for serious criticism.
Online communication
As already mentioned, the communication of the applications via the Internet is absolutely adequately secured at all times, without any indication of an exploitable vulnerability. The same applies to the communication of the headset itself. The only thing that is noticeable about this is that it communicates almost permanently. As soon as the headset is switched on, it establishes a connection to the Oculus or Facebook servers and then transmits almost continuously. We observed the traffic after switching on, in the main menu, during use and even in standby, and noticed quite a lively exchange with the cloud at all times. Of course, it is difficult to make statements about the content of the communication at this point, because the connections of the headset are securely encrypted and cannot be easily broken even in the lab. However, since the headset can also be used offline, i.e. without WLAN switched on, one can assume that the transferred data cannot be used exclusively for functionality. Apart from that, however, from a purely security point of view, no reasons for criticism can be identified in this respect.
Data protection and privacy
In fact, the Oculus privacy policy is very detailed on this point and addresses the most important issues. Among other things, the user is directly informed that all Facebook systems, including the Quest, run on a common database. The data collected by the Quest therefore converges internally at Facebook with the linkable user data from Facebook, Instagram, Whatsapp, Oculus and any other service that belongs to the Facebook group or simply integrates and uses the Facebook SDK. Accordingly, the recorded data is, if required, also shared with the entire group of companies, to which Oculus has belonged since 2014, and processed worldwide. Linking your own Facebook account to the Oculus account is not mandatory, but from a Facebook point of view this is probably not even necessary in order to perform it internally anyway.

When registering, you have to enter your first and last name in addition to your email address and a nickname. Further data is optional. Data collected about the person is combined with other available and publicly or commercially available data. The use of all content, games and apps is also recorded in order to personalize the services used and to display relevant information. The latter also includes advertising messages and content within and outside the Services. Third parties may also collect information to display advertisements within and outside of the Oculus or Facebook Services, for example, using information collected from various websites or online services over time. Recorded personal information is stored until it is no longer needed, such as until account deletion. In addition to viewing the data stored about the person, this can be done directly online.
Verdict
The Oculus Quest is without question technically a real innovation, which deserves the success it has achieved and makes the entry into the virtual world easier than ever for virtually everyone. From a data protection point of view, it is of course, also (or especially) because of its origin and company affiliation, rather questionable – it offers the company, which already has digital insight into the life of just about every connected person on the planet, the opportunity to now also have an ear and an eye on their analog life. At least Facebook makes no secret of this in its privacy policy, so there is no formal reason for complaint.
The quest thus joins the group of Orwellian surveillance nightmares, the Alexas, Siris and Okay Googles, but is not “worse” than these either. The user should only be aware of the possible implications in each case.
From a security point of view it is in any case on a similar level as the others mentioned and accordingly deserves the full 3-star rating.


Pingback: Oculus Quest 2 Av - Noonokorean