In a manner reminiscent of previous years, we delve once more into the realm of location-enabled smartwatches in this Quick Check. Such smartwatches, equipped with location tracking capabilities, still hold a strong appeal for vigilant parents and come in a plethora of colors, designs, and price brackets. Given our track record of issuing cautious appraisals in the previous years, it’s conceivable that the S12GPS Kids Smartwatch by PTHTECHUS from China may unveil enhanced performance this time, raising the prospect of a paradigm shift in the realm of smartwatch security.

Features
The PTHTECHUS S12GPS Kids Smartwatch presents a compelling array of attributes designed to elevate both security and enjoyment levels. Employing LBS GPS positioning, parents maintain continuous awareness of their child’s whereabouts. The adaptable time format (12/24HR) and integrated calendar foster time management through playful engagement. Voice remote control streamlines operation, while the voice chat functionality enriches communicative capabilities. In the event of an emergency, the SOS signal can be activated, and the tracking feature empowers parents to retrace their child’s escapades. With an IP68 waterproof rating, the watch exhibits resilience against the rigors of daily life. Supplementary features, such as the alarm clock, silent mode, two-way communication, and album functionality, round out the comprehensive package. Moreover, the watch offers support for five languages: English, French, Spanish, German, and Italian, making it an adaptable choice within the realm of IoT security.
Mobile applications
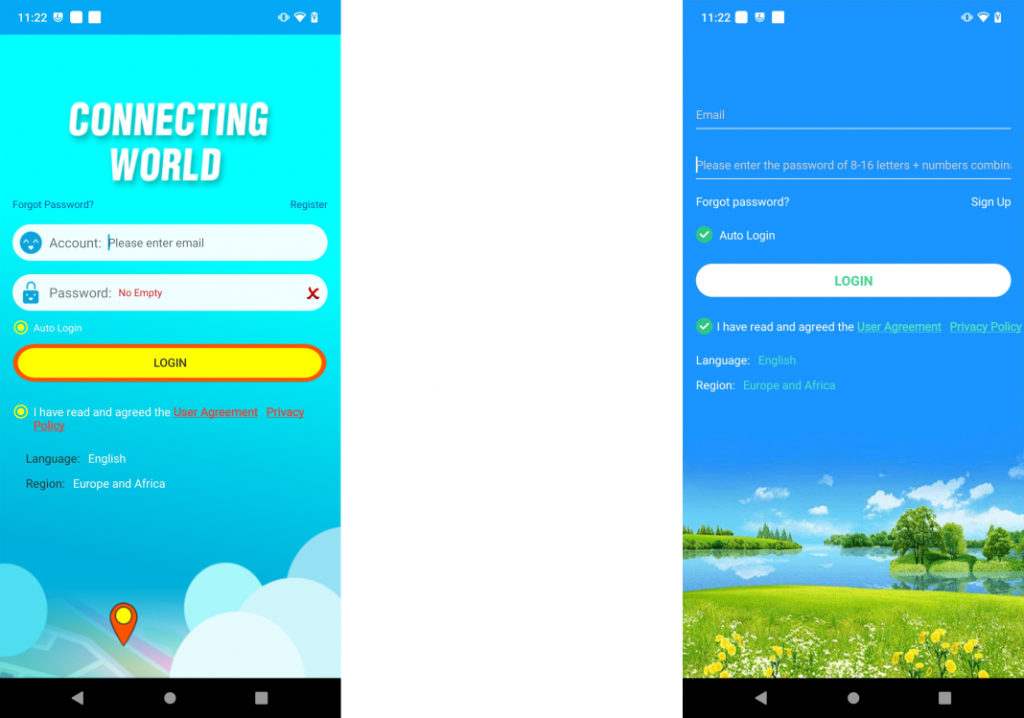
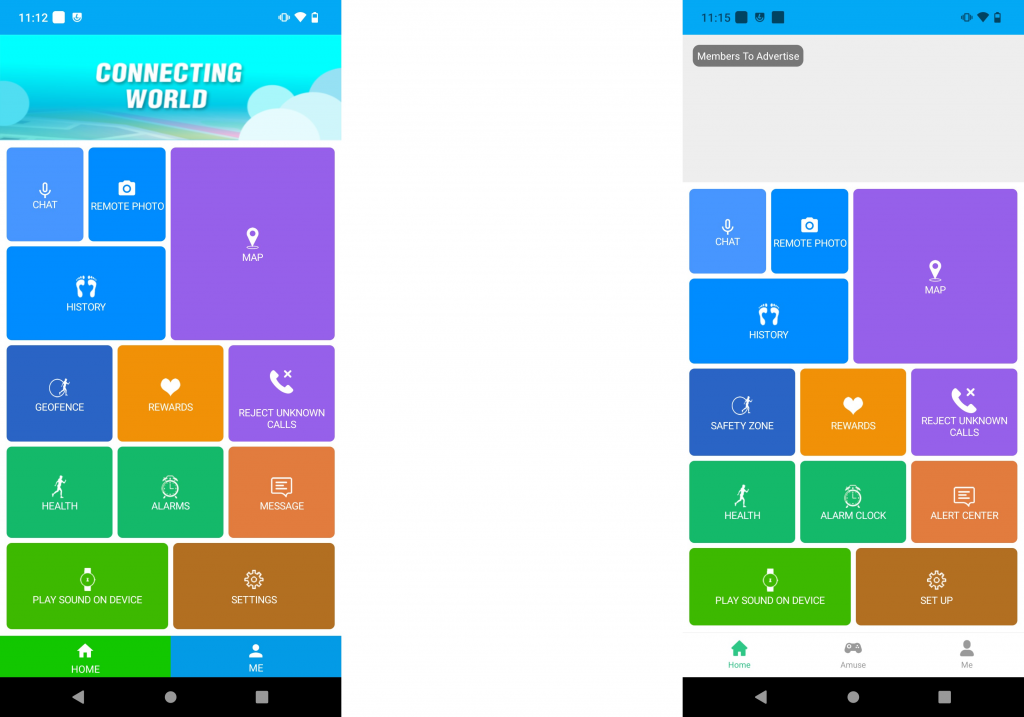
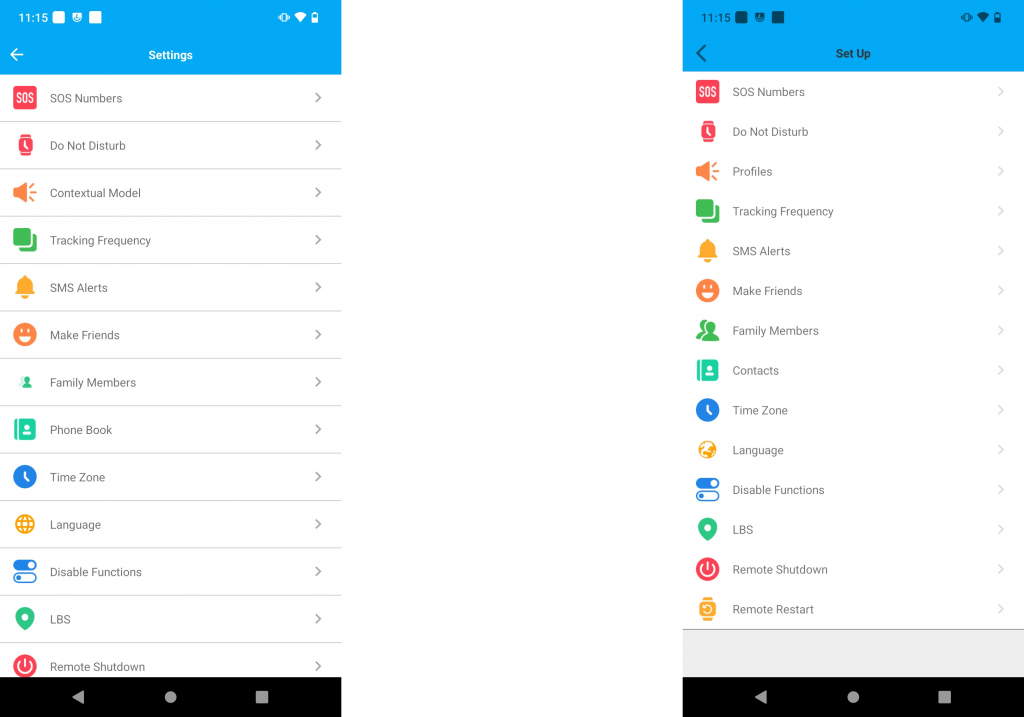
When examining the user manual for the Kids Smartwatch under review, we were introduced to two recommended applications. The first app is CarePro+ (com.tgelec.carepro in the tested version 1.2.2 for Android), while the second is SeTracker (org.zywx.wbpalmstar.widgetone.uexaaagg10003 in the tested version 4.9.0 for Android).
Remarkably, both applications exhibit fundamental similarities in their core functionalities and share account information. Registering with one app allows you to seamlessly log in to the other using the same credentials. Furthermore, their visual interfaces bear a striking resemblance.
Our Quick Check initiated with a static examination of the applications, but it swiftly became apparent that a direct analysis was unattainable. Both applications employed the Tencent Lengu Packer, a tool that transformed the dex files containing program code into a compressed and encrypted format. Consequently, in our initial static analysis attempt, we could only scrutinize the Android app’s manifest. Nonetheless, the Packer demonstrated its effectiveness as a defense mechanism against code analysis and tracker analysis in the realm of IoT security.
To confront this challenge, we commenced an intensive research effort. Despite the limitations of our research findings, what we uncovered proved immensely valuable for penetrating the compressed code. A 2019 blog post cast light upon this packer, prompting the launch of a corresponding project dedicated to decompressing and deciphering the code. Despite the original developers’ discontinuation, this decompression mechanism remains actively tended to and consistently updated by the community.
After effectively surmounting the encountered challenges, we are now embarking on the journey of static analysis. Given the striking resemblance between these two applications, we can consolidate them within this scrutiny. The principal differentiation between the two applications manifests in SeTracker’s propensity for displaying intrusive advertisements and offering an extra section replete with minor games. Notably, CarePro+ exhibits an absence of advertisements, and there exists no avenue to curtail them through a subscription model, unlike SeTracker. This subscription undergoes automatic renewal.
An in-depth examination of permissions reveals that CarePro+ mandates full access to specific functions within the app, a requirement shared by SeTracker. However, SeTracker, as anticipated due to its integrated advertisements, also necessitates the use of the Ad ID. While the allocation of this identifier may not be flexible, it proves to be an essential element when considering that the app’s financial sustenance depends solely on advertising revenue.
As we delved into the Android app manifest during our investigation, we made a significant discovery that has already highlighted potential vulnerabilities in some of our other Quick Checks. In the SeTracker app, plaintext communication is enabled, meaning that unencrypted information could be transmitted. In contrast, this feature is deactivated in CarePro+, and with this Android takes proactive measures to prevent any form of unencrypted communication. This revelation underscores the critical importance of IoT security.
In the context of trackers within mobile applications, our investigation revealed that CarePro+ had no trackers, whereas SeTracker contained several identified trackers.
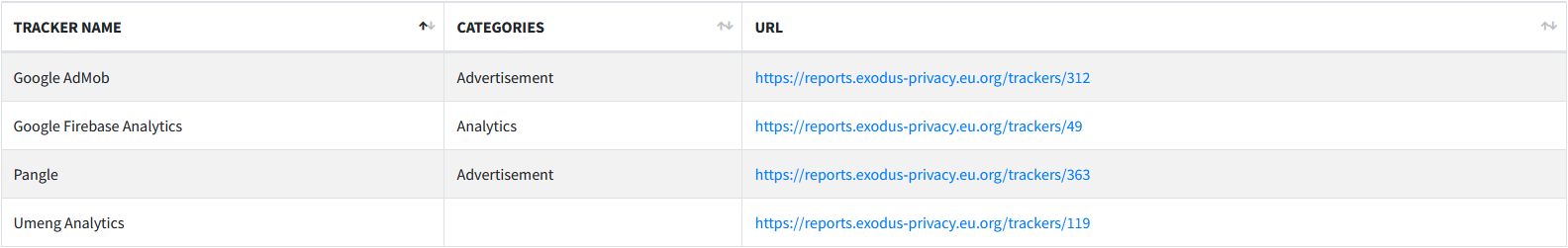
In our exploration of IoT security, we have come across several tracking mechanisms that contribute significantly to understanding the intricacies of app behavior, encompassing aspects such as crashes and performance. Notably, the “Google Firebase Analytics” tracker plays a pivotal role in this regard. Additionally, “Google AdMob” and “Pangle” are instrumental in monitoring the delivery of advertisements, ensuring a seamless user experience. On the other hand, “Umeng Analytics” specializes in behavior analysis, data collection, and statistical insights.
Local and online communication
In the context of local communication, there is relatively little to report since the application exclusively communicates with servers, and the kids smartwatch also communicates solely via the mobile network. Consequently, there is no local communication between the app and the smartwatch.
During our investigation of online communication, we found that both applications fundamentally secure their communication through encryption mechanisms. They employ TLS 1.2 and 1.3 to protect communication and utilize QUIC.
When it comes to enhancing security measures, distinctions emerge between these two applications. CarePro+ enables the use of standard system certificates, whereas SeTracker relies on SSL pinning.
In essence, a certificate serves as proof that a public key is linked to a particular website. Public keys play a crucial role in encrypting communications and are decrypted on the server using the corresponding key. This mechanism ensures secure communication. To ascertain the key’s legitimacy with the website, certification authorities sign the certificate only after verifying its authenticity. This process forms the basis of the security framework in CarePro+.
In the dynamic landscape of IoT security, SSL-Pinning emerges as a pivotal technique, adding a layer of robustness by demanding a specific public key that corresponds to a designated server within the application. This requirement transcends the typical prerequisites of a correct, up-to-date certificate signed by a reputable certification authority; it mandates a precise alignment with a designated public key.
Utilizing SSL-Pinning provides an extra layer of defense against Man-in-the-Middle attacks, significantly reducing the pool of trusted certificates. Moreover, it serves as a robust shield against potential assaults on certification authorities, where counterfeit certificates could be forged, potentially leading systems to mistake them for genuine, thus facilitating connections with malicious actors seeking to intercept data traffic.
By implementing SSL-Pinning, we reinforce our IoT systems against the perils of Man-in-the-Middle attacks, characterized by eavesdropping, decryption, and potential data manipulation, while also enhancing resilience against phishing attempts, particularly those involving fraudulent websites.
In the realm of IoT security, SSL pinning stands out as a highly recommended practice that we consistently encourage implementing. However, it does come with its fair share of challenges, which squarely fall within the purview of developers. The initial implementation of this mechanism undeniably demands a certain level of effort. Additionally, each certificate has a finite lifespan, necessitating frequent app updates to incorporate the most current certificate. Failing to do so would render a connection impossible. While this initially requires heightened resource allocation and entails increased maintenance, it concurrently ensures enhanced security for user data.
In the context of our Quick Check, we delved deeper into the Web API, primarily to uncover potential vulnerabilities that could potentially enable unauthorized access to user data, devices, or user accounts. Due to the limited depth of the Quick Check, we couldn’t conduct a comprehensive analysis. However, we did scrutinize the functions utilized by applications to retrieve information about users and devices. In the case of unsecured APIs, there is often the possibility of gaining access to data or functions beyond one’s own permissions through simple manipulations of device or user IDs in the requests.
While we can offer some reassurance for now, it’s important to note that we have not identified any glaring issues in our assessment. There are, however, certain peculiarities worth mentioning, none of which can be directly classified as security vulnerabilities. For instance, during the login process, passwords are hashed, but without additional security measures such as salting and peppering for hashing. This leaves room for a potential attacker who successfully intercepts the data traffic to decrypt the password using publicly available rainbow tables. Furthermore, the password undergoes double hashing, first with MD5 and then with SHA256. This dual hashing approach does not provide enhanced security but could be viewed more as ‘Security through Obscurity‘ since the algorithms are visible within the code.
Amongst additional instances, it is noteworthy to mention that the cookie created post a successful login maintains its validity for a complete day, and even logout procedures do not invalidate it. Nonetheless, it’s imperative to observe that every message incorporates a signature field, assuring the message’s integrity. Nevertheless, the calculation of the signature value is accessible within the source code and can be reconstructed independently. This presents the potential for replay attacks within a one-day time frame. Considering that security is assessed through the Trust Manager using certificates and SSL pinning, we don’t immediately perceive a significant threat in this scenario.
The central issue lies in the unencrypted transmission of a cookie to a server operated by Hangzhou Alibaba Advertising Co. Ltd, particularly when accessing advertisements. This cookie comprises two components: an active login token and an SID necessary for API path requests. Access to protected API requests would be impossible without this cookie. However, within the confines of our quick assessment, we were unable to retrieve sensitive information solely through the cookie. This task would also require access to the corresponding device ID and the associated login name. By default, the login name is typically the email address used for logging in. A potential attacker could potentially acquire access to both of these pieces of information through alternative means, thereby gaining, for instance, access to the smartwatch’s location. Unfortunately, this situation is exacerbated by the absence of rate limiting on the server. Consequently, attackers are only constrained by the bandwidth in the number of requests they can make to the server to test various email addresses or device IDs.
![]()
In this context, prompt action is urgently required. It is, however, fortunate for us that intercepting this message appears to be somewhat incidental, as we have been unable to replicate it deliberately. Consequently, this attack vector may not be deemed highly critical for an individual IoT device. Nevertheless, it is crucial that we address and rectify this issue promptly. Additionally, the attribute in the manifest governing plaintext communication should be accurately configured to preemptively avert this problem.
Data protection and privacy
The privacy policies of both applications share many similarities. A noteworthy distinction only emerges in the app names and with SeTracker concerning additional third-party providers. Although the privacy policies are written in English, it would be desirable to have German translations similar to those in the user manual. However, an English version is also quite useful.
It quickly becomes apparent that these explanations were primarily not designed for the European market. While there is a contact person mentioned, they can only be reached through WeChat. While WeChat is ubiquitous in China, it is less common here. Furthermore, a clear address is missing. In contrast, comprehensive information is provided about which data is used by which services and for what purpose they are processed. The permissions used are also detailed. It should be noted that, unlike the GDPR, no legal foundations are provided, and the app already requires certain permissions before the user’s consent.
In addition, various scenarios are presented in which data transmission is possible in the context of IoT security. These scenarios include:
- Directly related to national security and national defense security.
- Directly related to public safety, public health, and critical public interests.
- Directly related to criminal investigations, law enforcement, court proceedings, and criminal enforcement.
- To protect the personal information of the individual or other personal lives, property, and other important legal rights and interests when obtaining consent from a person is challenging.
- Personal information collected by us that has been publicly disclosed by the individuals themselves.
- Personal information derived from legally publicly accessible sources, such as legitimate news reports, government information, etc.
- Required to enter into or perform a contract in accordance with your request.
- Required to maintain the safe and stable operation of the software and related services, such as detecting and resolving software and service failures.
- Required for legal reporting.
- Needed by academic research institutions to conduct statistical research or scientific research in the public interest and to anonymize personal information in research results when the results of scientific research or descriptions are disclosed externally.
- Other situations as required by laws and regulations.
The scenarios are seen from China’s perspective, likely belonging to a Chinese entity: ShenZhen Anquanshouhu Tech Co. Ltd.
Regarding user rights, there is a dedicated section. However, not all rights are thoroughly addressed, and some of the mentioned rights are rather cryptic. While the process of data deletion is explained, specific subsections regarding this are absent in our app. A closer examination reveals that the privacy policy was crafted for an advanced app version, enabling chat and profile integration for content sharing. It remains uncertain whether these functionalities are exclusive to China, resulting in the omission of certain rights accorded to us under the GDPR, such as data deletion.
It’s worth highlighting the positive approach of planning to communicate privacy policy updates via in-app messages. However, it’s evident that the privacy policy has likely remained stagnant since 2020, as indicated by the 2020 copyright notice. Furthermore, there’s a noticeable absence of information regarding SeTracker’s trackers.
In a comprehensive evaluation, the privacy policy does offer a detailed breakdown of the data in use. However, it’s essential to recognize the conspicuous absence of many aspects mandated by the General Data Protection Regulation (GDPR). While this positions the privacy policy relatively well in our Quick Check, it falls short of the necessary compliance standards for marketing products in the EU. In such cases, the privacy policy must undergo adjustments to adhere to EU regulations.
Verdict
Within the landscape of IoT security, the PTHTECHUS S12GPS Kids Smartwatch has showcased its mettle through rigorous app static tests. Nevertheless, it is disconcerting to uncover the presence of trackers and plaintext communication within the SeTracker app. As a result, CarePro+ earns a solitary star, while SeTracker remains starless due to its omission of tracker details in the privacy policy. In our evaluation of communication, one star is warranted, given the absence of significant issues. While the overall privacy policy demonstrates reasonable adherence to standards, it falls short of GDPR benchmarks, precluding the allocation of additional points. Hence, our cumulative rating stands at one star.

