Anyone who has ever set up a smart home environment knows the problem: many providers have many different components, but none alone has everything you want. So you usually have no choice but to assemble your system from components from different manufacturers. Even though many systems nowadays communicate via standardized protocols, automation and coordination of the individual components can quickly become more technical than many customers would like. If you don’t have the time or the know-how, the only option is to control the individual components via a number of different apps.
This is precisely the problem that Bosch subsidiary Residential IoT Services wants to address and is developing an app that will enable the control and automation of systems from a wide range of partner manufacturers – all via one interface. “Home Connect Plus” is the name of this application, which is available for Android and iOS – a sensible idea, in our opinion, and reason enough to take a look at the application from a security perspective.
Of course, the whole idea only makes sense if a wide range of manufacturers and associated products are supported in order to cover all potentially desirable types of components. The Home Connect Plus application presents itself well in this respect, and many well-known manufacturers are already on board as partners in the current version. The following list is available on the store pages, and the complete list can be found at www.home-connect-plus.com.
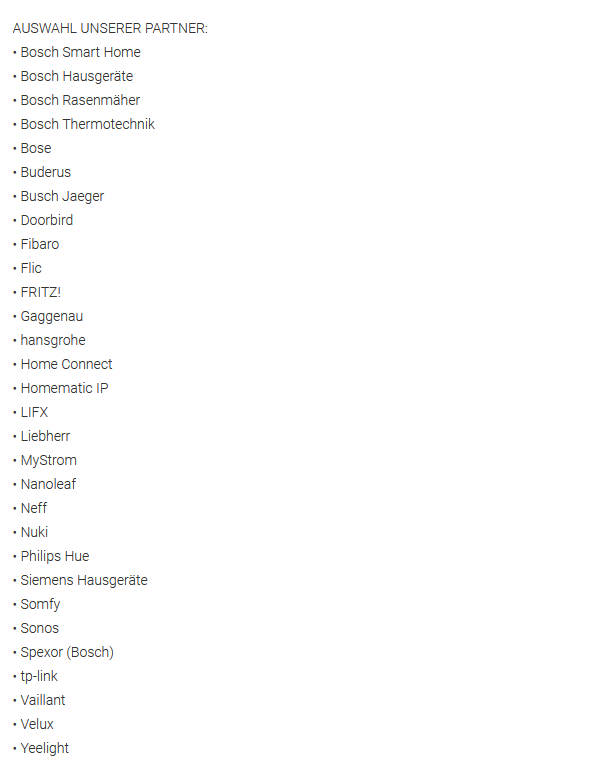
Since the app cannot and will not bypass the security measures of these products, all devices have to be set up via their own platforms and can then be integrated into the app. For some manufacturers, such as Nuki, the option of exporting to another app must also be allowed via the manufacturer’s app – so despite everything, the setup is quite complex, but in the best case it should only have to be done once. For operation, this also means that the devices have to be permanently online in order to be controlled – but that is the case for most products nowadays anyway.
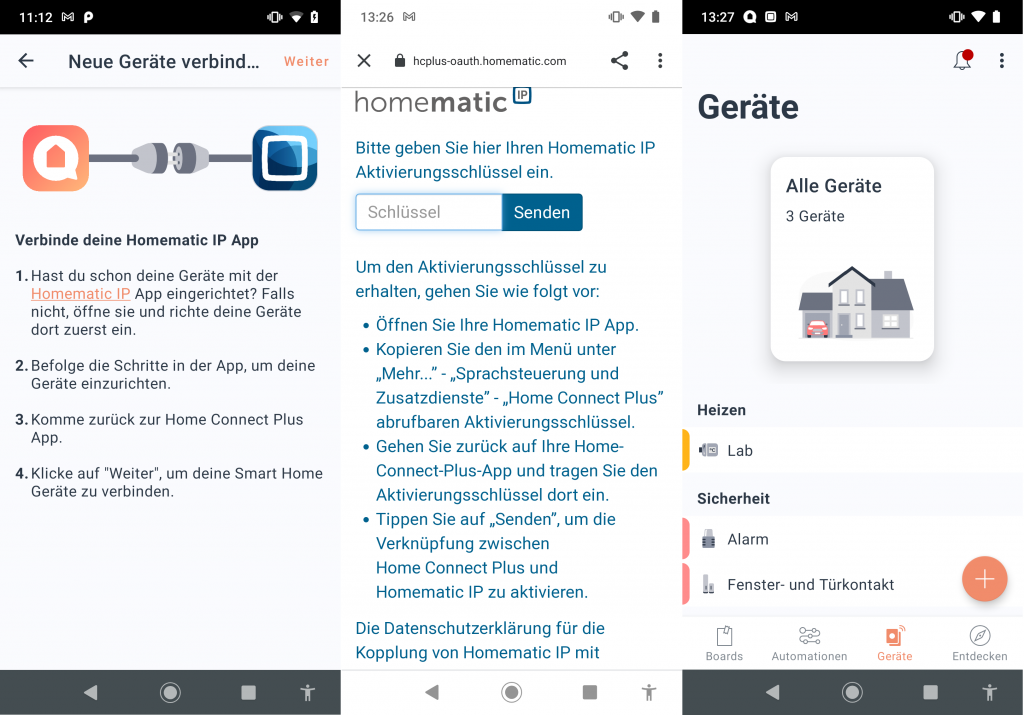
Devices can then be combined, scenarios created and automation implemented via so-called boards. Even if not all functions of each device can be executed via the Home Connect Plus app, a whole lot can be simplified.
Static Analysis
We have subjected the current versions of the Home Connect Plus application (Android v1.0.5 (19107) & iOS v1.0.3 (19052)) to our static analysis to find out if there are any implementation-related potential vulnerabilities to be tracked down. Basically, everything looks satisfactory in this area: The applications do not require any noticeable permissions and the security-relevant areas are implemented cleanly and without any obvious vulnerabilities. We only noticed two things that could at least theoretically offer attack potential. For example, a larger number of shared object libraries (.so) have not been compiled with the PIE flag in the Android application, so that the memory access protection ASLR is not active here. In addition, the transfer security is configured strangely, to say the least. The base configuration is such that basically unencrypted connections to arbitrary domains are allowed. However, only encrypted traffic is allowed for three special domains (namely bosch.com, azure.com and riot-platform.com). There could be different reasons here, but this configuration still seems inconsistent. Normally, you simply disallow all unencrypted traffic here and you are on the secure side of things.
Dynamic Analysis
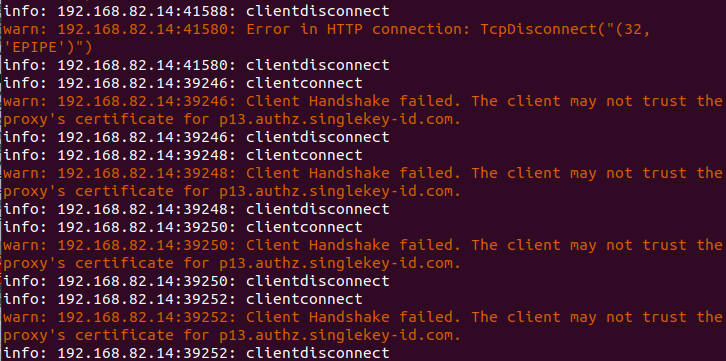
As part of the dynamic analysis, we also looked at both application versions during operation to identify possible weaknesses, for example in network traffic. But even here, we did not notice any noteworthy points of criticism. The communication we observed was always encrypted and all authentication processes, which we naturally always scrutinize particularly closely, are adequately secured against the most common and likely attacks. With a man-in-the-middle attack on the app’s single-key authentication, we were able to read at least parts of the logout process with an installed root certificate – nothing really critical is transmitted at this point, but the developer should nevertheless take another look at why the certificate pinning fails or is not applied. The login process, on the other hand, where real credentials have to be transferred, was completely immune to such attacks, so an attacker actually only has a chance here if he has physical access to the user’s smartphone and the possibility to exchange a patched application version with the original version – Extremely unlikely in practice, especially since an attacker with these possibilities has already won anyway.
Privacy
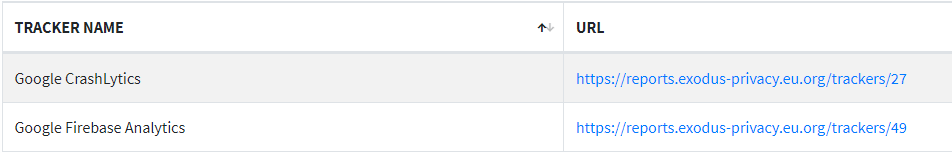
We have taken a closer look at the privacy policy of the Home Connect Plus app as of May 6th 2021. Residential IoT Services GmbH is responsible for the processing of the data (as well as for the development of the app), as already mentioned, a company belonging to the Bosch Group. The privacy policy is only available in the app and cannot be viewed online before installing the app or creating a Bosch SingleKey ID account. In the Google Play Store, the link to the privacy policy is completely missing, and in the Apple App Store, the link refers to a non-existent website – Unnecessary, in our opinion, because the privacy policy itself provides very detailed information both about data recorded by the app, such as location information, and about information required for the connection of other systems. The app’s integrated trackers Google Firebase Analytics and CrashLytics (both now standard in pretty much every mobile app) are also mentioned.
Verdict
All in all, a good idea, implemented absolutely adequately. The range of functions, as well as the final, consistent security implementation are certainly still expandable, but all in all a successful implementation that is apparently still being refined. The completely unnecessary points noted in the data protection area spoil the impression a bit – overall 2 out of 3 stars!


Pingback: What is a Bump Key & How It Works? – Home Inspection Insider